In the Microsoft 365 admin center, you can get a list of all the groups…
Migrate legacy MFA and SSPR to Authentication methods policy
The legacy multifactor authentication (MFA) and self-service password reset (SSPR) policies will soon deprecate. This means you must migrate these legacy policies to the new converged Authentication methods policy for Azure Active Directory. In this article, you will learn how to migrate from legacy MFA and SSPR policies to converged Authentication methods policy.
Table of contents
Legacy MFA and SSPR policies deprecated
Microsoft has announced the deprecation of managing authentication methods in the legacy multifactor authentication (MFA) and self-service password reset (SSPR) policies. To avoid any service impact, it’s recommended to migrate these old MFA and SSPR policies by September 2025 to the new converged (unified) Authentication methods policy.
Note: Please migrate your authentication methods off the legacy MFA and SSPR policies by September 2025 to avoid any service impact
After you complete the migration, you can manage all authentication methods together in the Authentication methods policy. It allows you to create tenant-wide authentication policies from a single configuration page in the Microsoft Entra admin center.
We will show you how to migrate MFA and SSPR policy settings to the Authentication methods policy for Azure AD (Microsoft Entra ID).
Authentication methods policies
Before we start the migration process, we need to know which authentication methods our organization enabled in the Microsoft Entra ID.
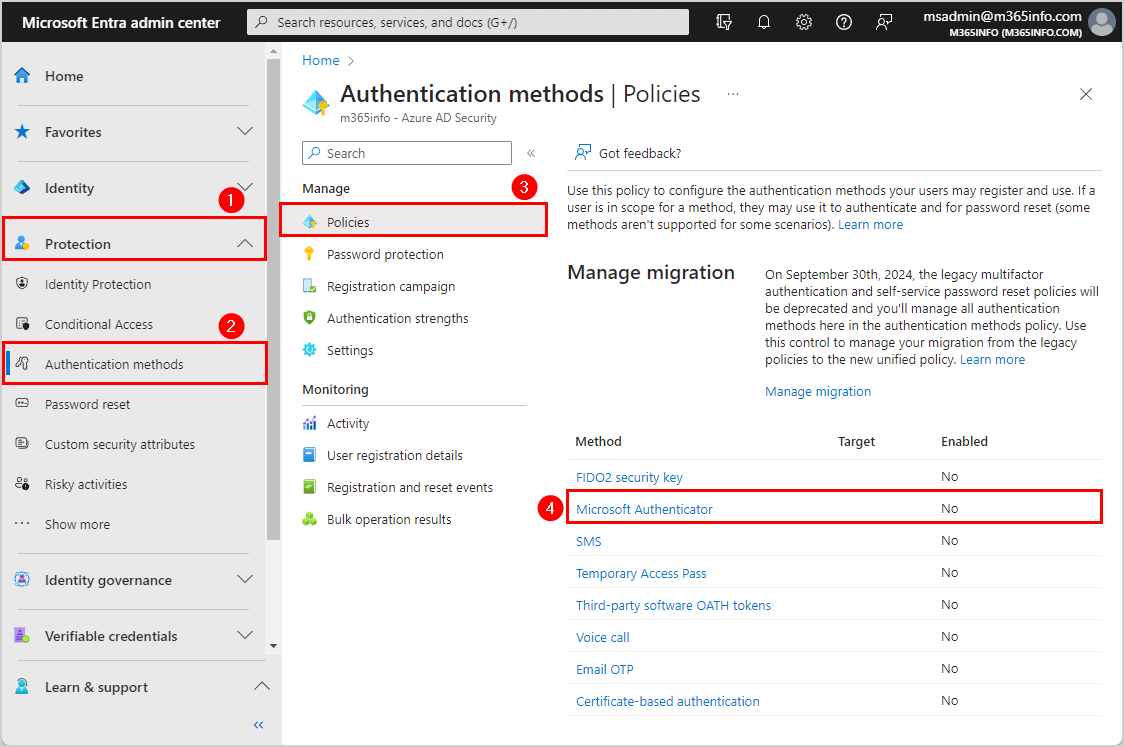
Follow these steps to see the authentication methods policies:
- Sign into Microsoft Entra admin center
- Click Protection > Authentication methods
- Go to Policies
You will see a list of all the authentication methods. If this is a new tenant, then it will have all the methods disabled by default.
Note: You can’t disable all authentication methods in the user credential policy. Enable at least one auth method to prevent lockout. Otherwise, the migration can’t be completed.
You need to enable at least one authentication method for all users. In our example, we will only enable the Microsoft Authenticator.
- Click on Microsoft Authenticator
- Click Enable
- Select All users
- Click Save
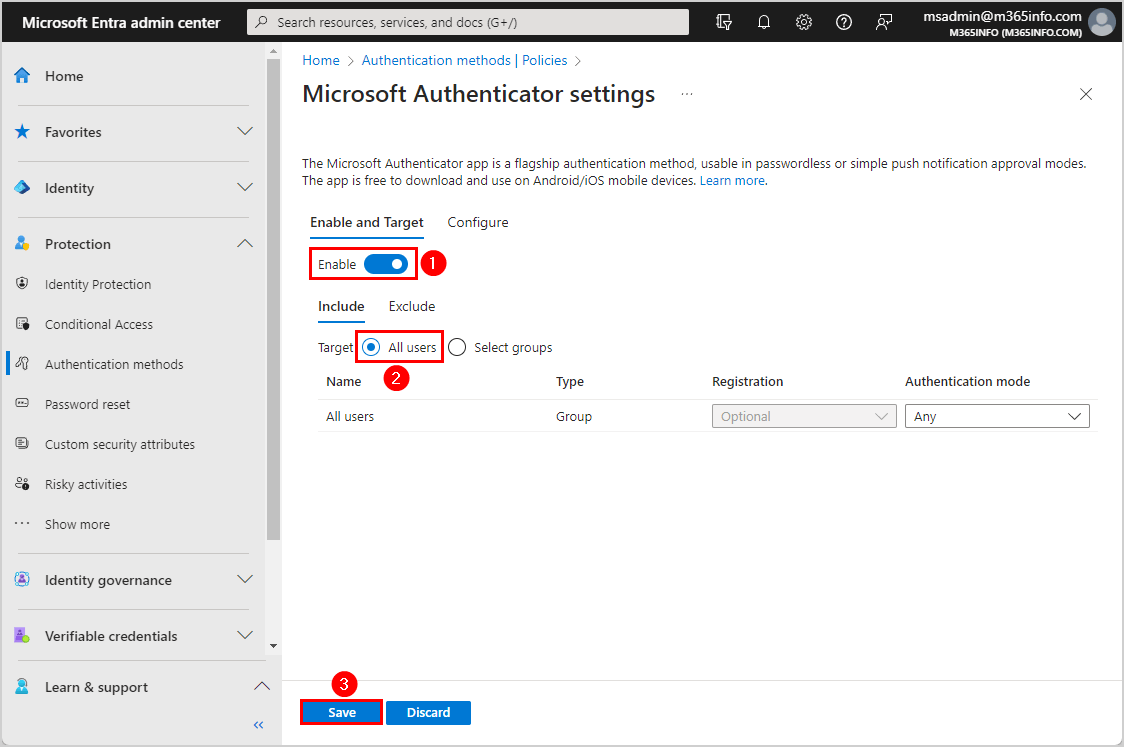
- The method Microsoft Authenticator enabled for all users
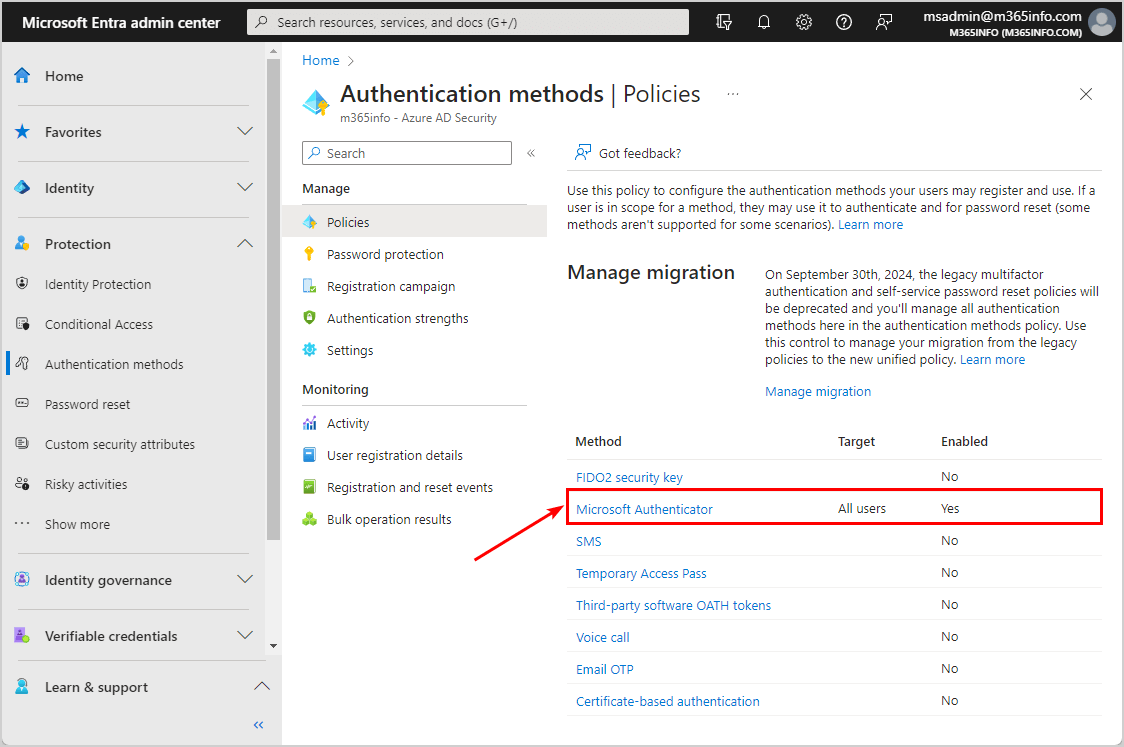
Start legacy MFA and SSPR policies migration
You can manage the migration in Azure AD or Entra portal. In our example, we will show you how to start the migration process in the Microsoft Entra admin center.
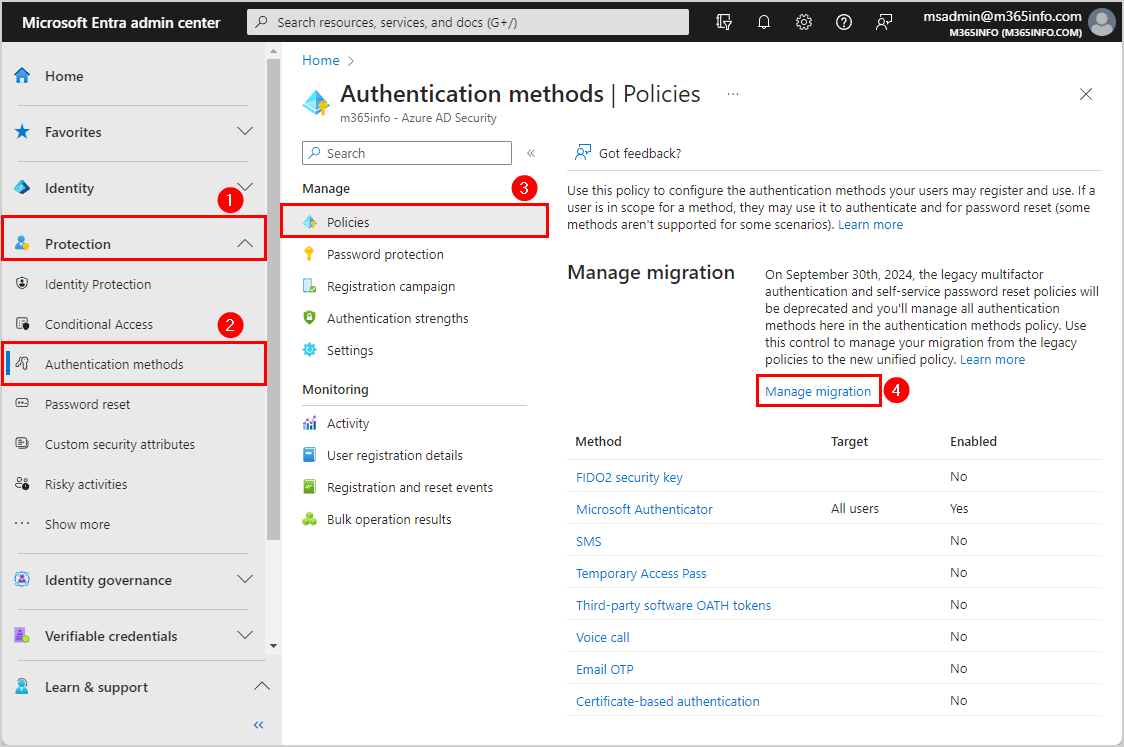
How to start legacy MFA and SSPR policies migration process:
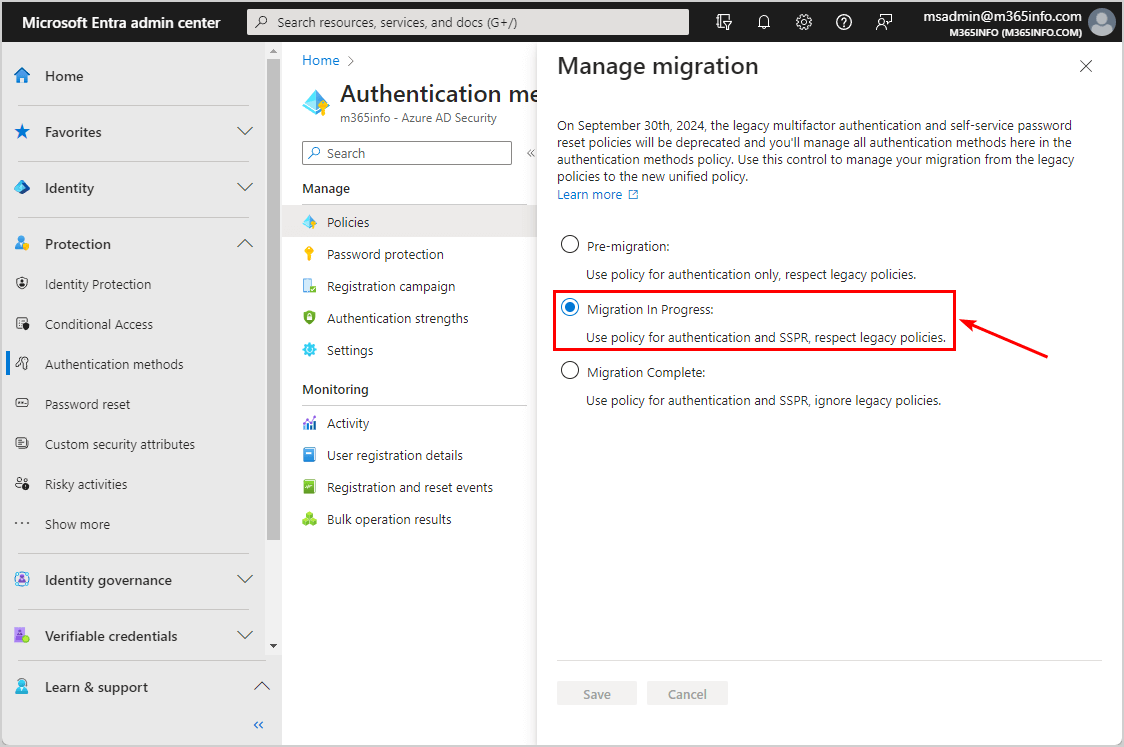
- Sign into Microsoft Entra admin center
- Click Protection > Authentication methods
- Click Manage migration
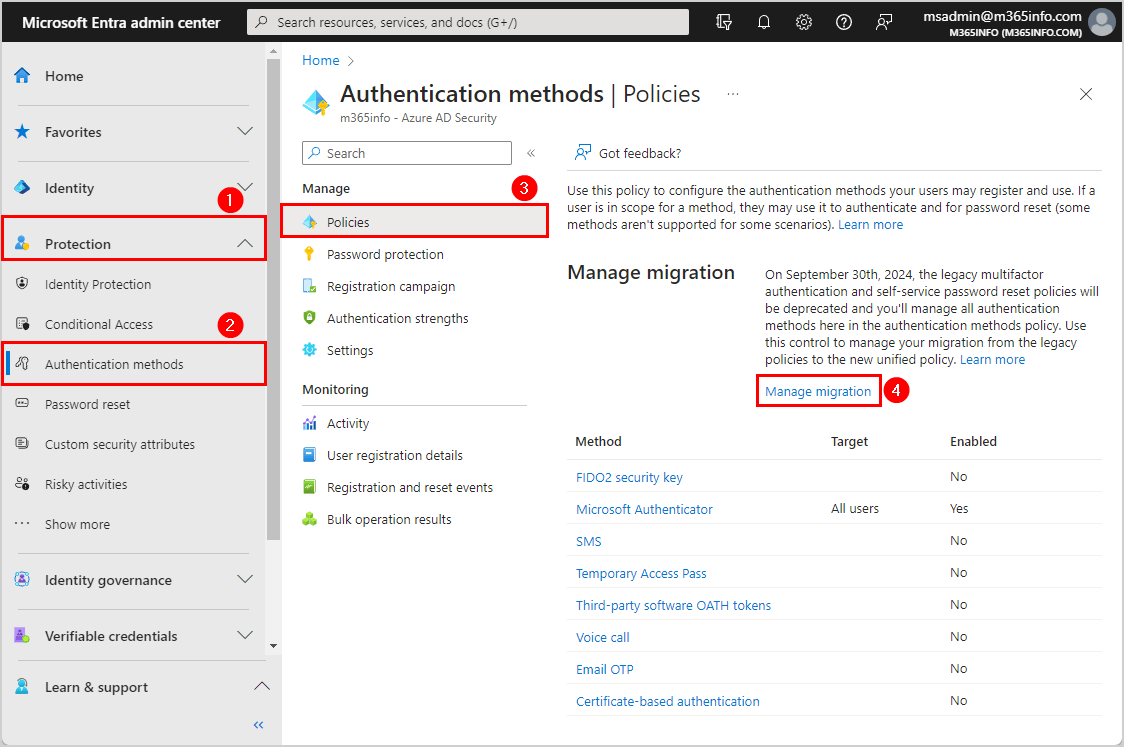
- Select Migration in Progress
- Click Save
If the Migration in Progress already is selected, you don’t need to do anything here.
1. Check legacy per user multi-factor authentication
We need to check the legacy mfa in the old portal, which you can access in two ways:
- Microsoft 365 admin center
- Azure Active Directory
We will show you both options in the next step.
Option 1: Legacy MFA in Microsoft 365 admin center
First, we will see the see the legacy MFA in the Microsoft 365 admin center:
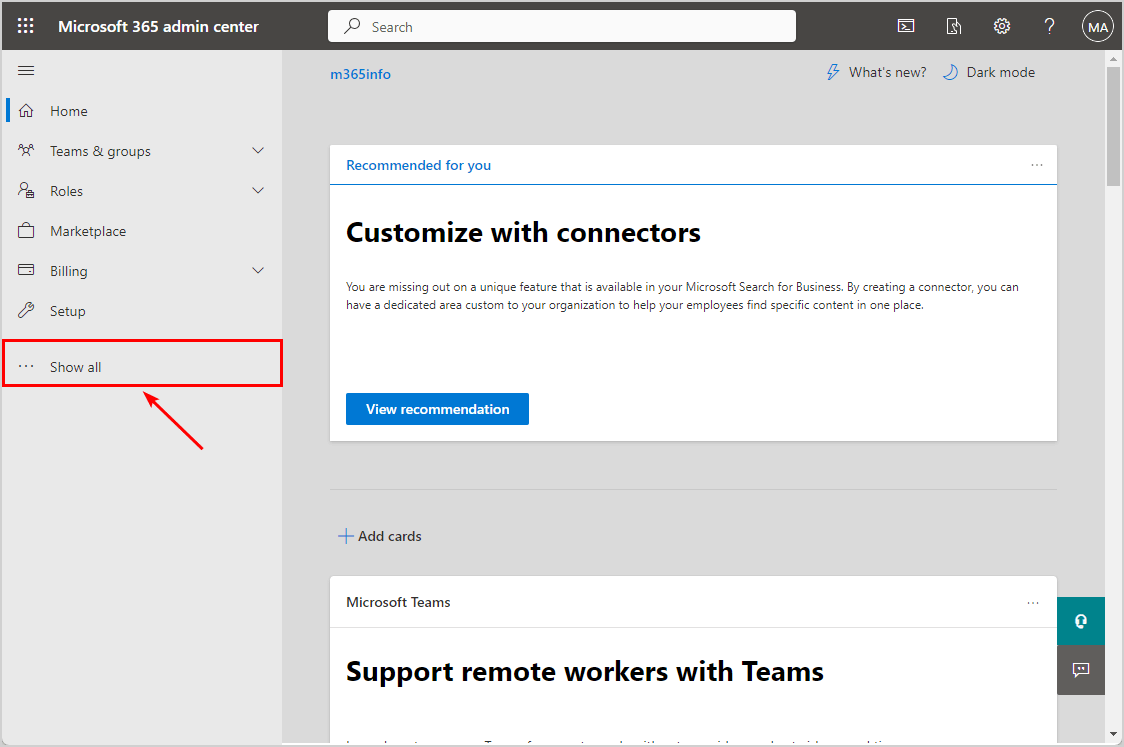
- Sign into Microsoft 365 admin center
- Expand Show all
- Click Users > Active users
- Click Multi-factor Authentication
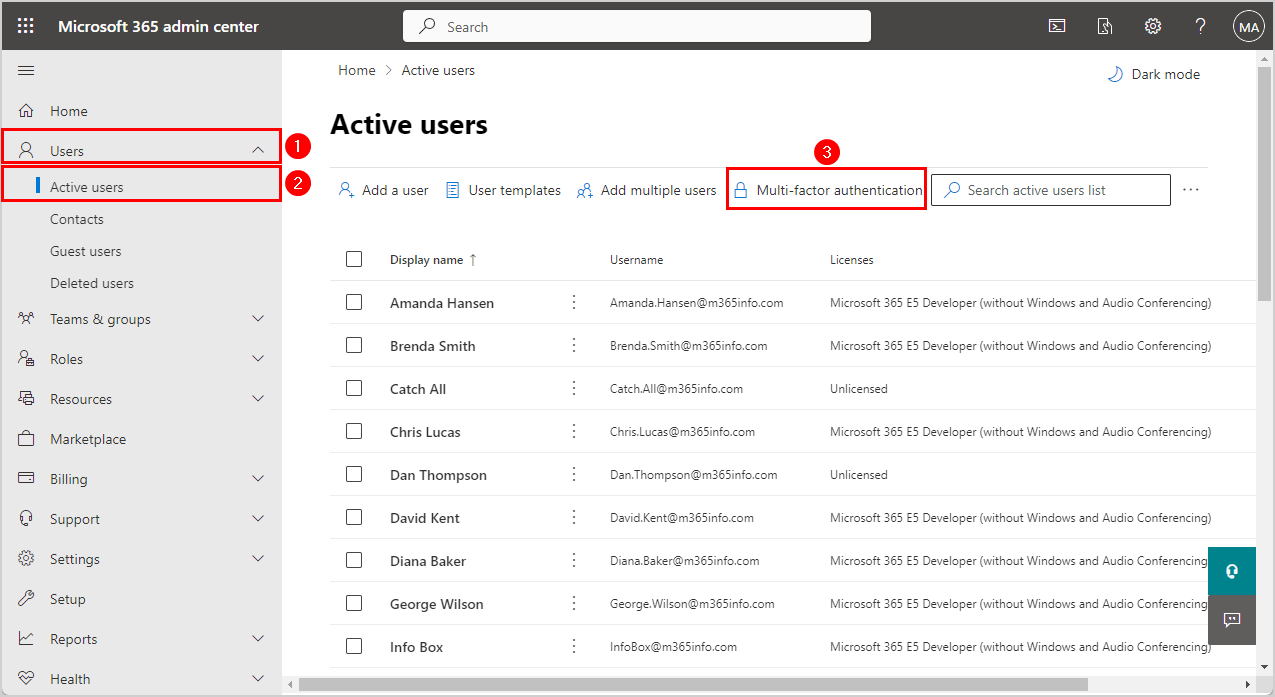
The Configure multifactor authentication (MFA) opens in a new tab.
- Click Legacy per-user MFA
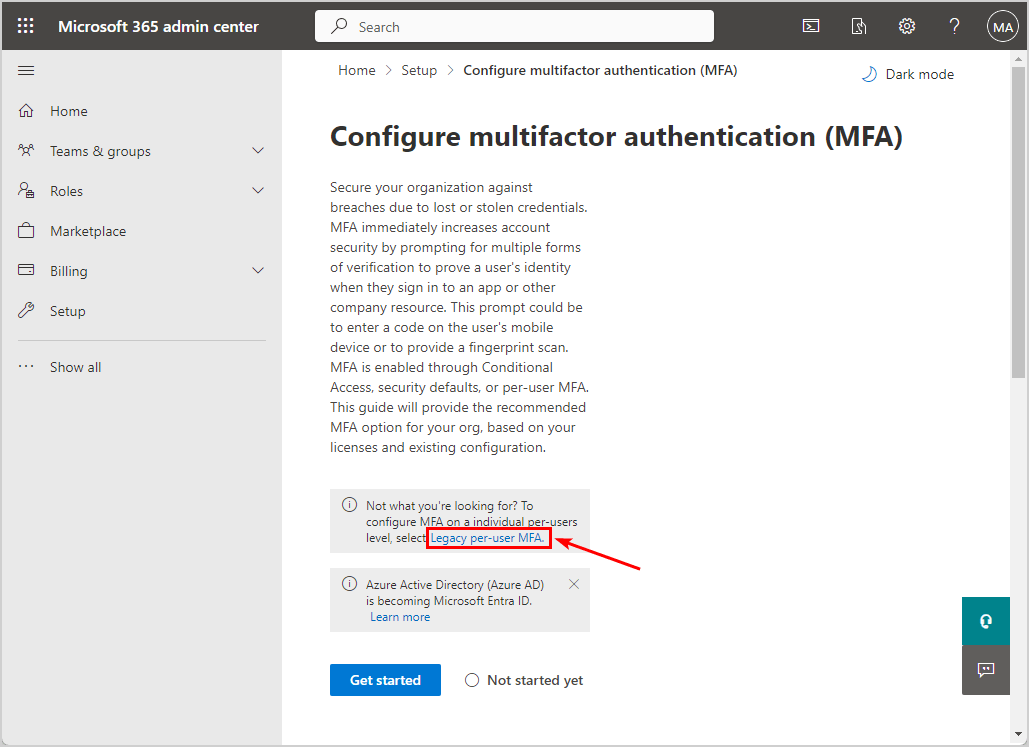
The old multi-factor authentication portal opens in a new tab.
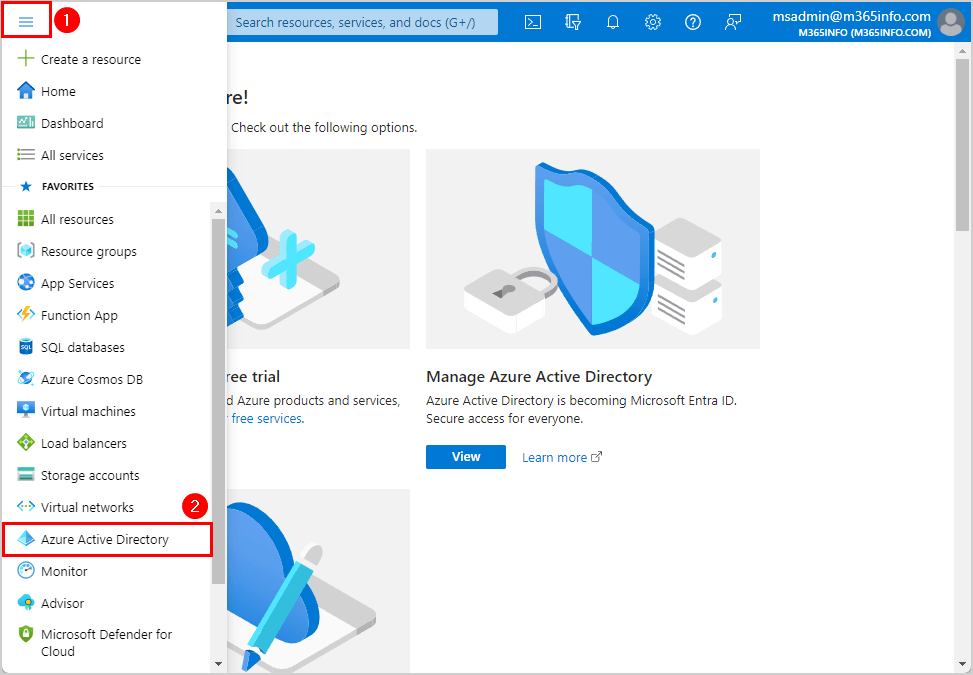
Option 2: Legacy MFA in Azure AD portal
We can also view the old MFA portal in Azure Active Directory.
- Sign into Microsoft Azure
- Open the menu
- Click Azure Active Directory
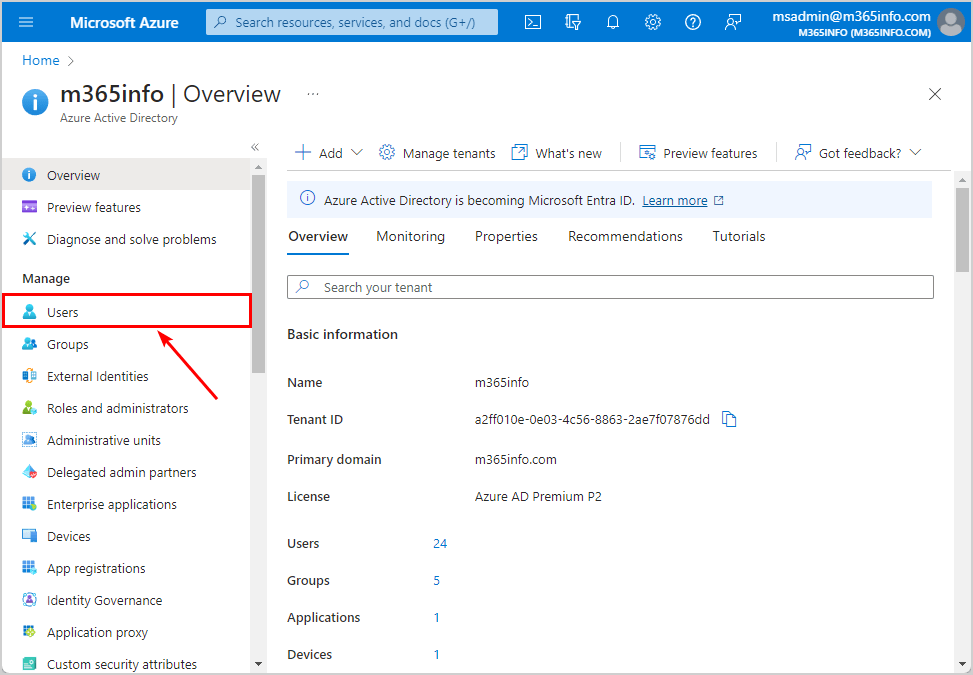
- Click Users
- Click Per-user MFA
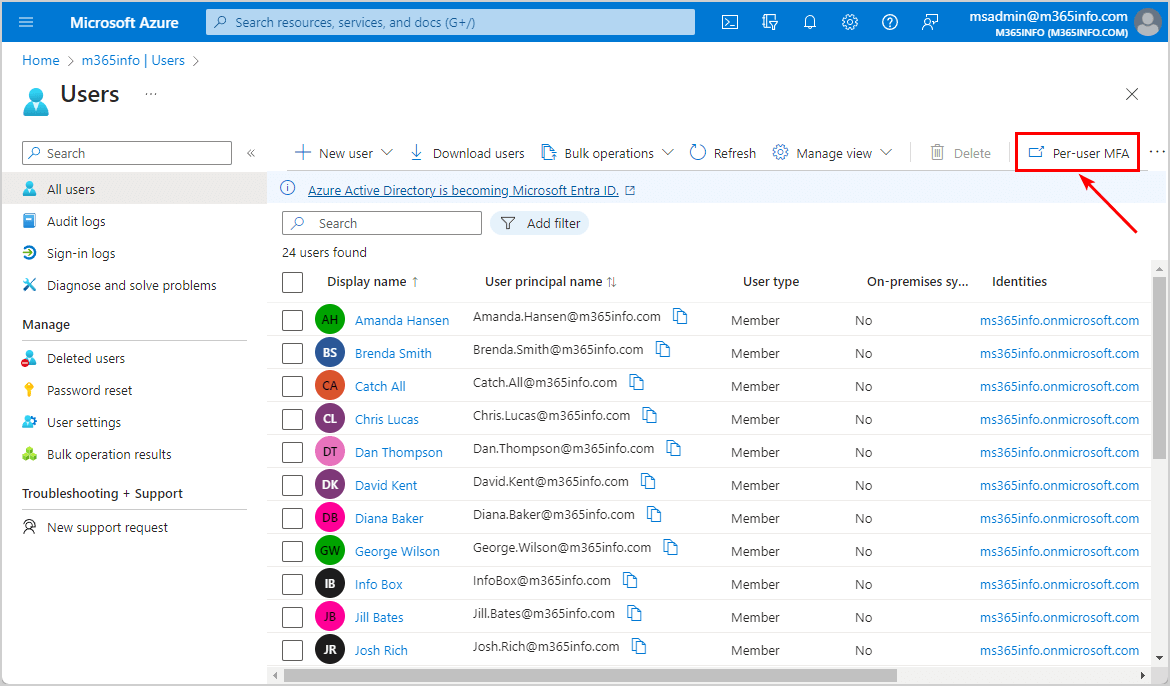
It will open the old multi-factor authentication portal. Here, you will see a list of all the users with the multi-factor authentication status.
- Check your user MFA status
Note: If all the users’ status is disabled, it means you are using conditional access mfa in your organization. You can only see a different status (enforced, enabled) per user if you are using per-user mfa.
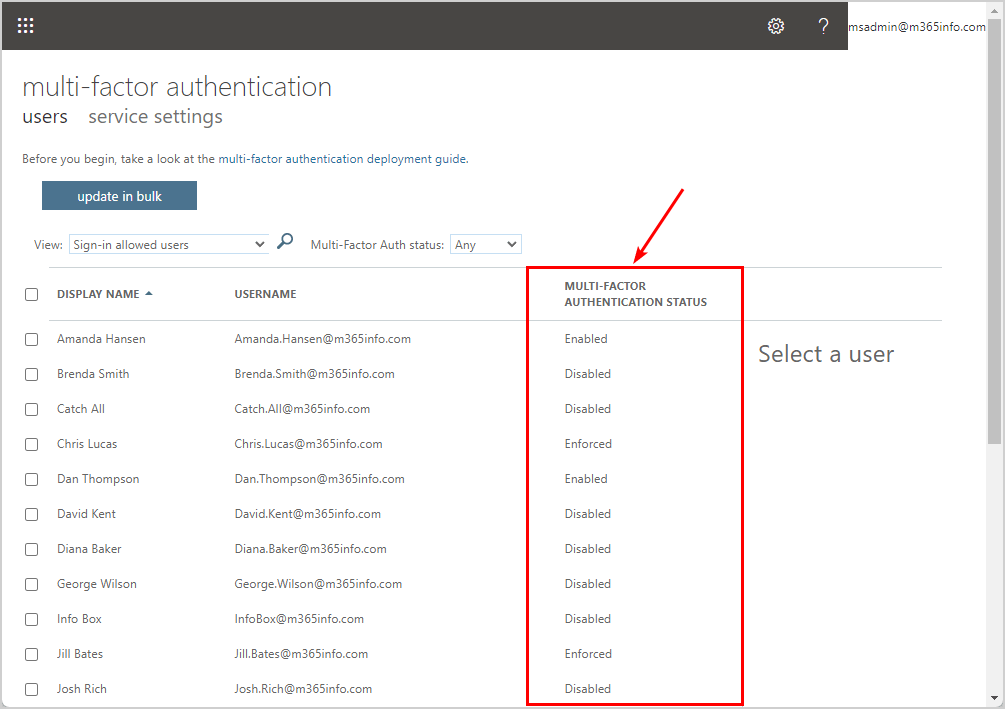
You don’t need to do anything here but continue to the next step.
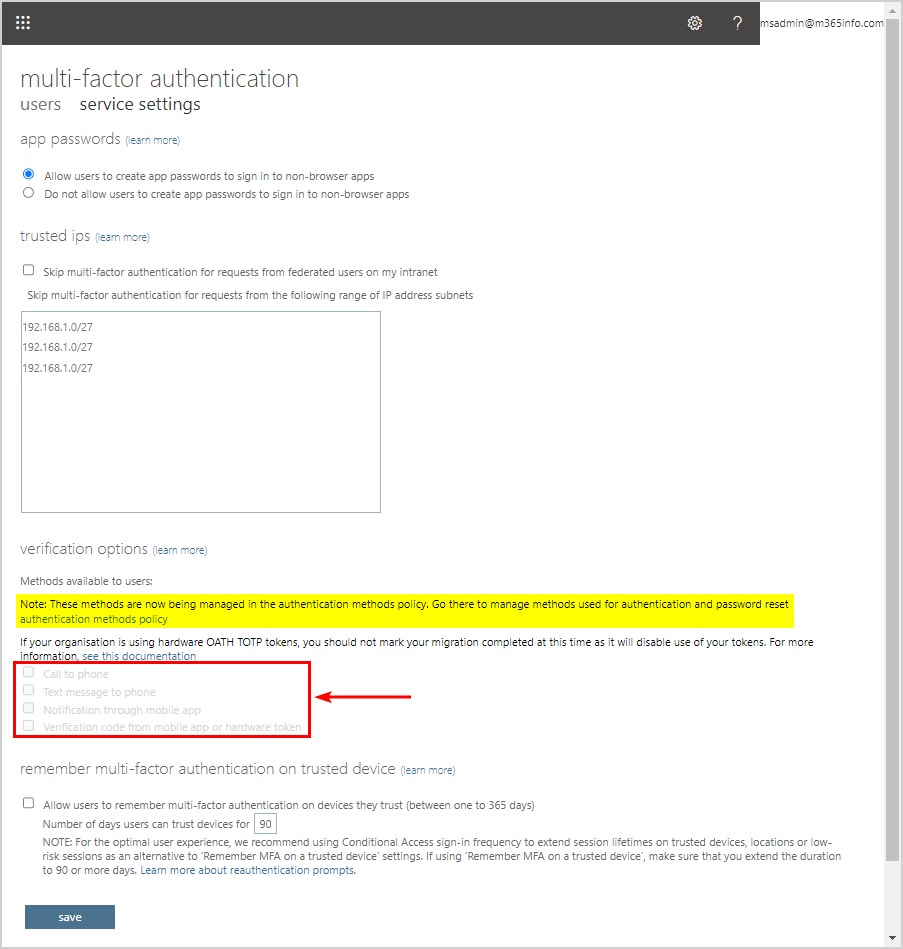
2. Remove legacy MFA service settings
The next step is to remove the MFA service settings in the old portal.
The old multi-factor authentication portal opens:
- Click service settings
- You will find the verification options selected
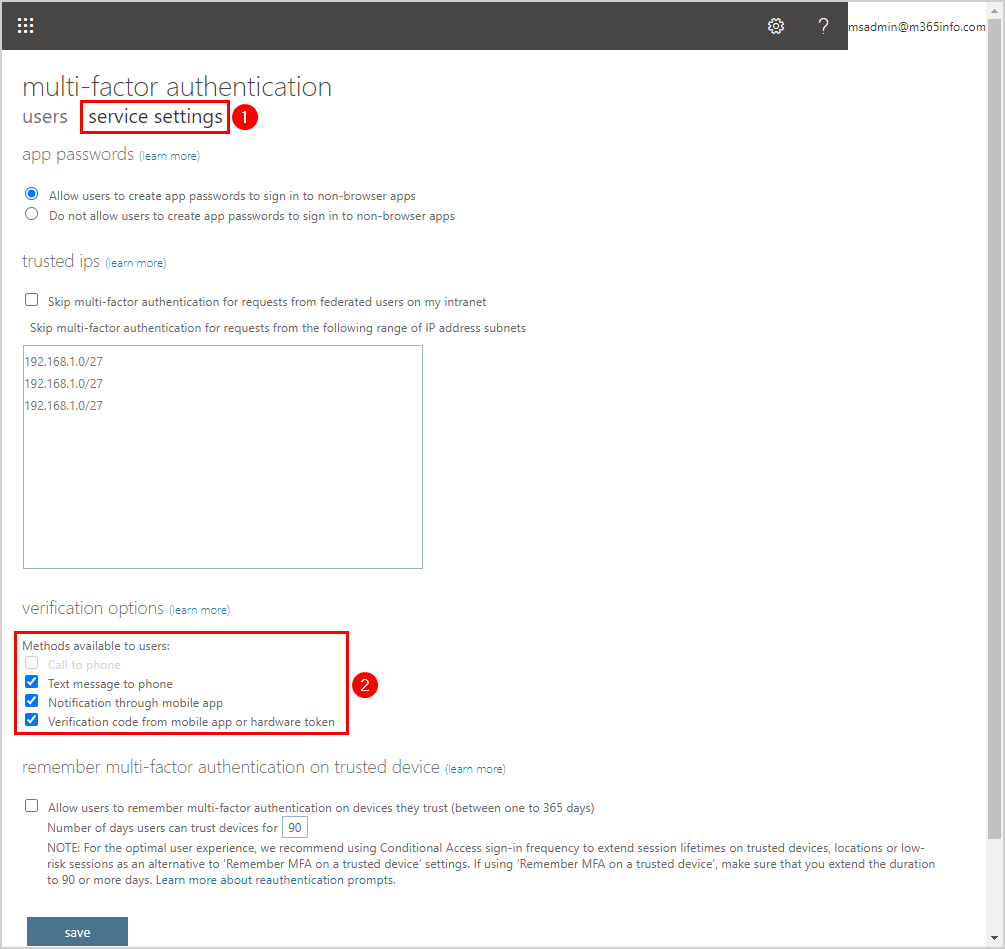
We want to clear all the check boxes under verification options.
- Clear check box Text message to phone
- Clear check box Notification through mobile app
- Clear check box Verification code from mobile app or hardware token
- Click Save
Note: Ensure that you have enough authentication methods enabled in the new authentication methods policy before saving.
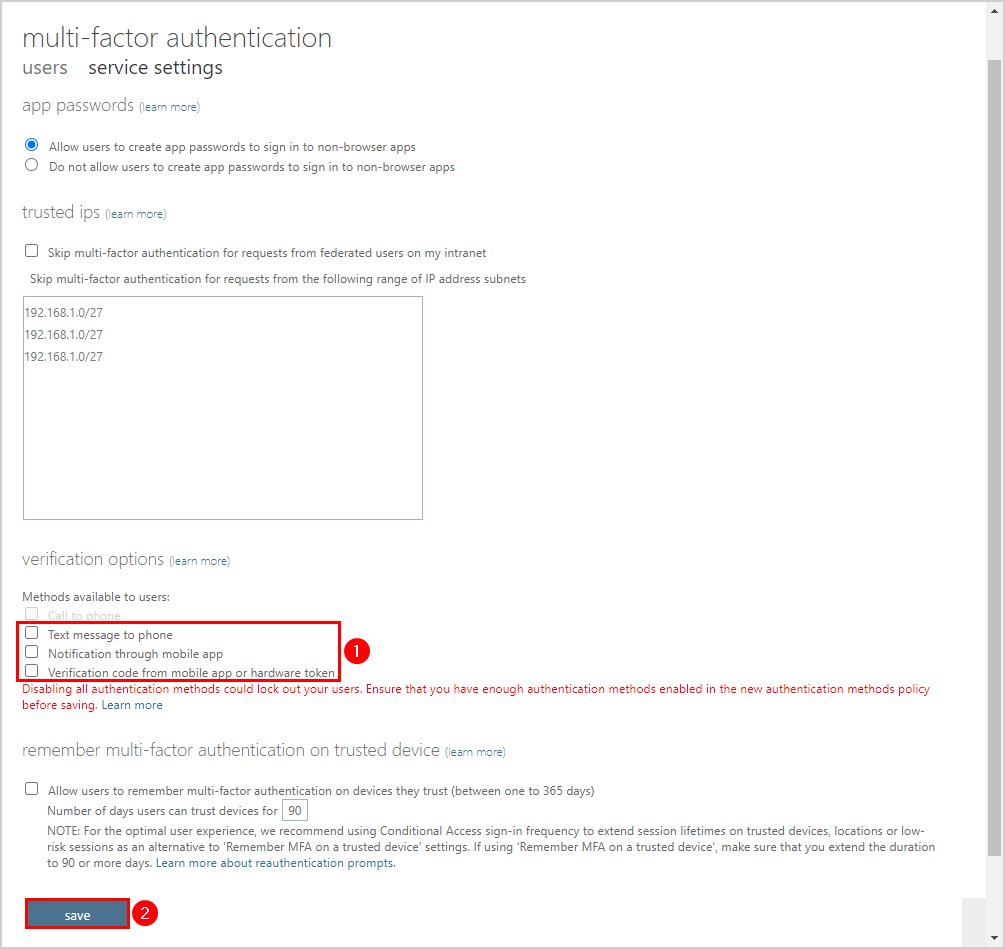
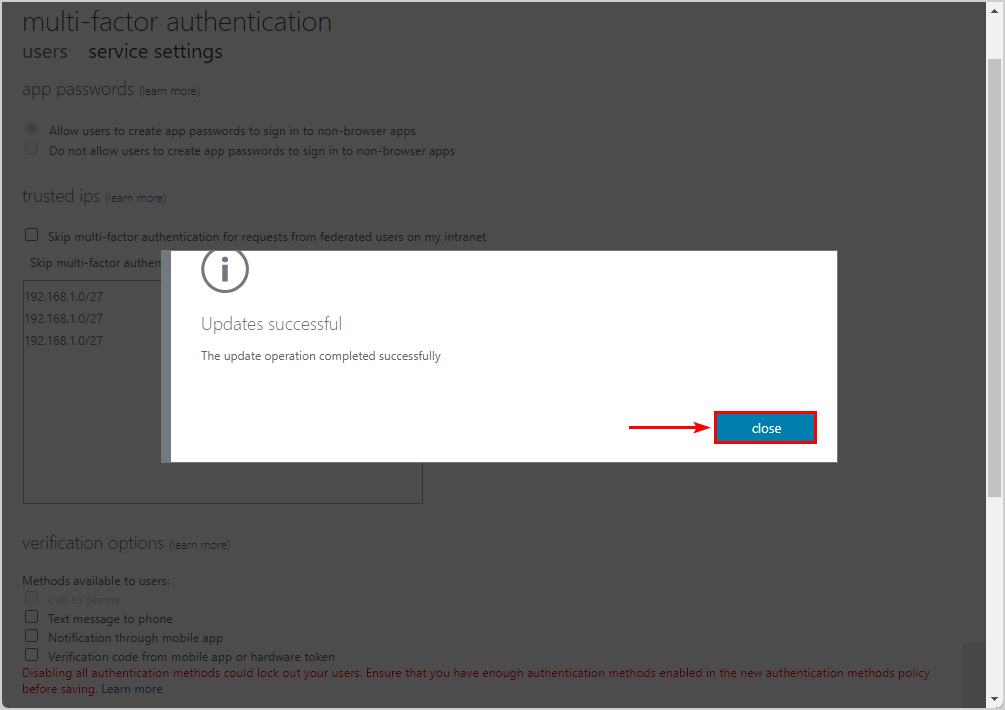
The update operation completed successfully!
- Click close
3. Remove legacy SSPR settings
You also need to remove the legacy password reset policy saved in Microsoft Entra ID.
- Sign into Microsoft Entra admin center
- Click Protection > Password reset
- Click Authentication methods
- See the password reset methods that are selected
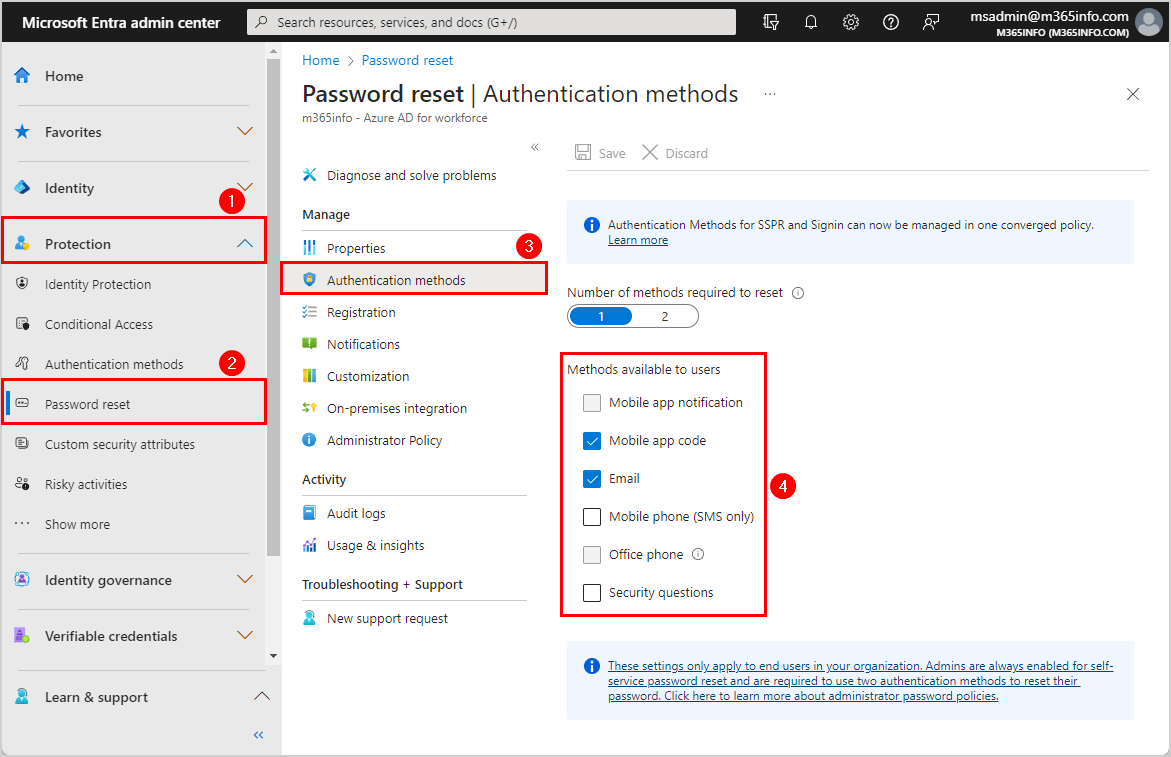
- Clear all methods
- Click Save
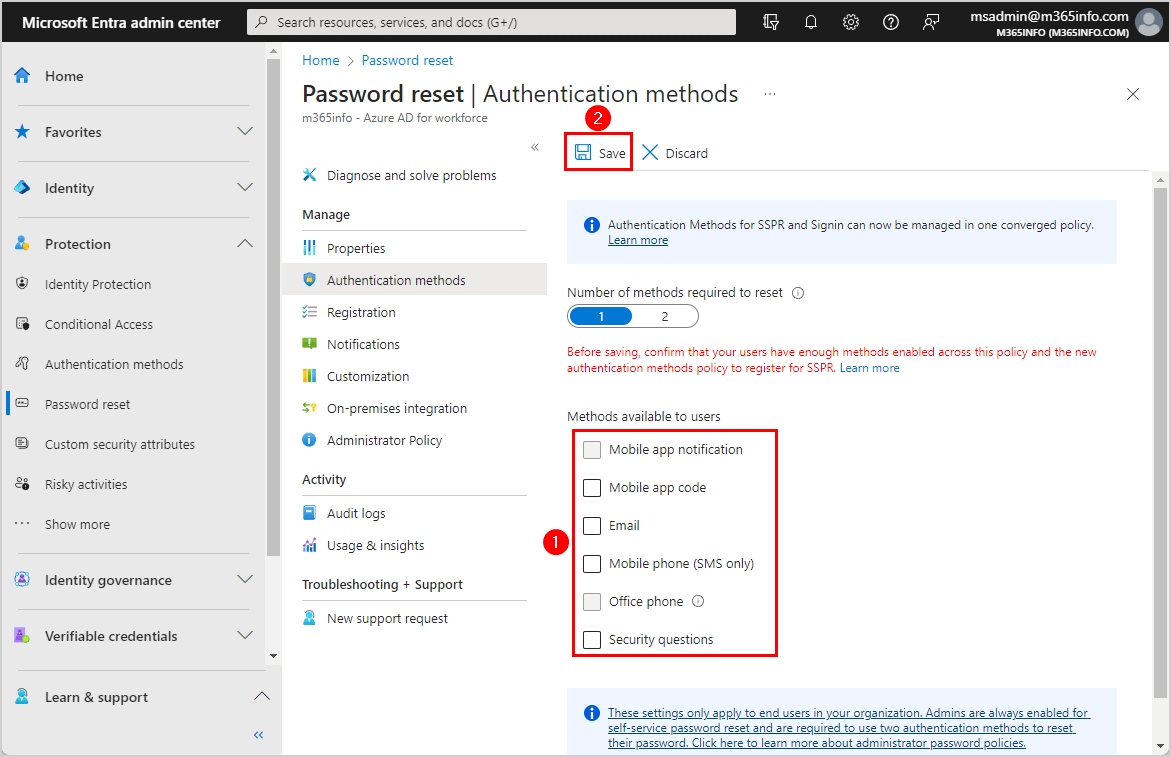
It successfully saved the changes to the password reset policy.
Complete migration to converged Authentication methods
Note: You can’t click on migration complete until disabling all methods in the legacy MFA and SSPR policies.
The final step is to complete the migration in Microsoft Entra ID.
- Go to Microsoft Entra admin center
- Click Protection > Authentication methods
- Click Manage migration
- Select Migration Complete
- Click Save
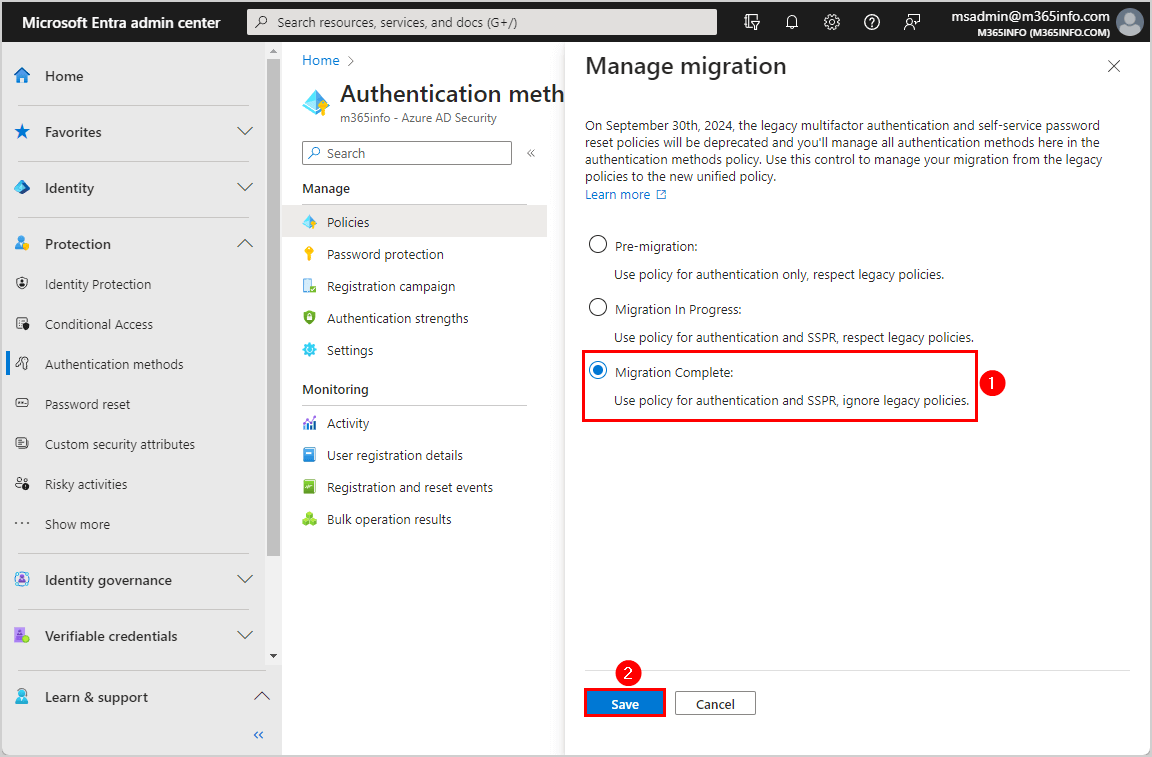
You successfully completed the migration.
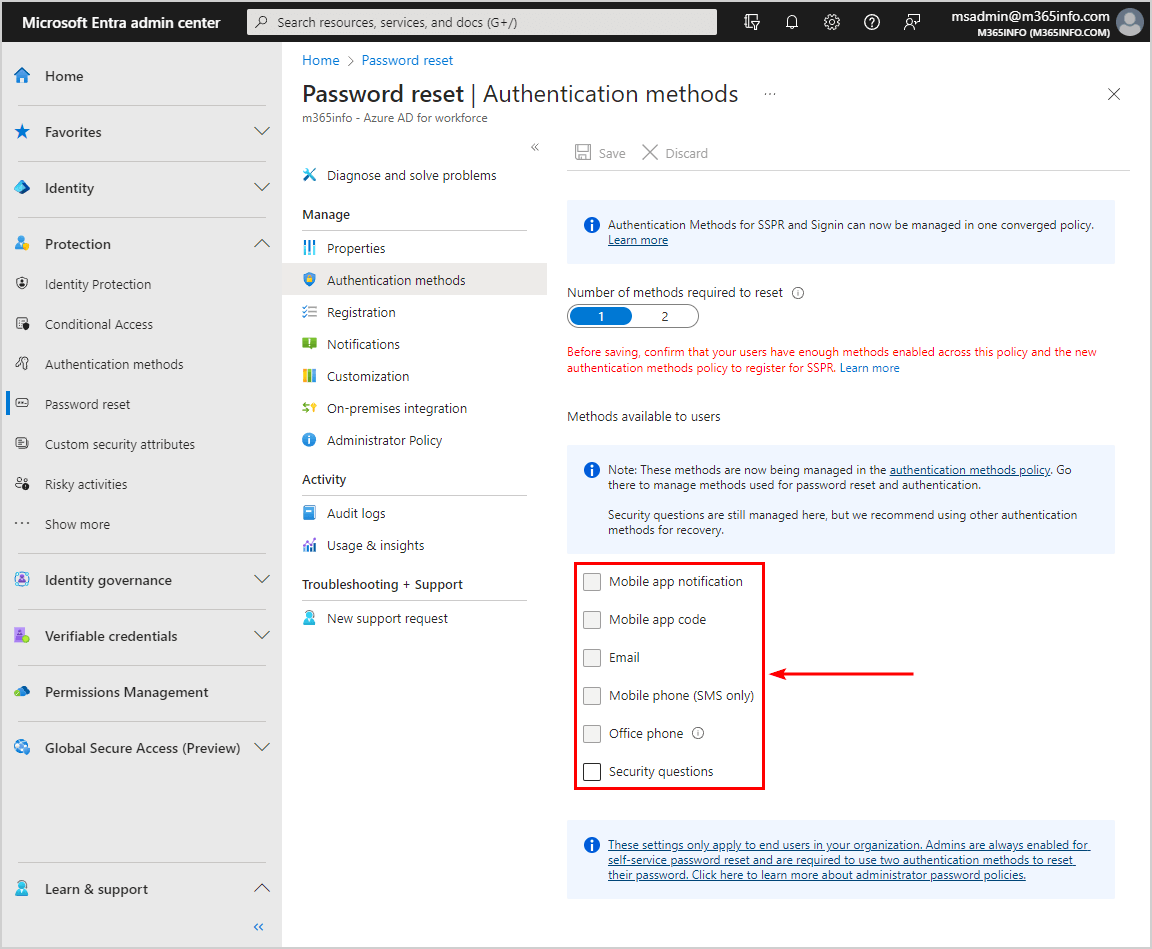
Verify converged Authentication methods migration completion
You can verify that the old legacy MFA and SSPR policies are disabled correctly.
Verify all methods in legacy SSPR policy disabled:
- Go to Microsoft Entra admin center
- Click on Protection > Password reset
- Click Authentication methods
You will see that all the methods used for password reset are greyed out, except for security questions.
Verify all methods in legacy MFA policy disabled:
- Go to the old multi-factor authentication portal
- Click service settings
Under verification options, it says that all these methods are now being managed in the authentication methods policy. You can see that all the methods available to the users are greyed out.
You are all set!
Read more: How to improve Microsoft Entra MFA security »
Conclusion
You learned how to migrate from legacy MFA and SSPR policies to Authentication methods policy. Before you start the migration, you need to enable at least one authentication method for all the users in the new Authentication methods. When you start the migration process, you must disable the old methods in the legacy MFA and SSPR policies. Lastly, you can complete the migration in the Microsoft Entra admin center.
Did you enjoy this article? You may also like Reset MFA for Microsoft 365 user. Don’t forget to follow us and share this article.

It says to disable all methods in legacy MFA policy (and of course to add all them in a new portal before migrate), after migration I haven’t any problems with users, and all will be back correctly?
After migration I have to do nothing and all will goes well?
That’s correct.
If we migrate all users, Does all the users have to re-enrol for Microsoft Authenticator even if they are already using it OR it is just going to enforce those users who was using any other MFA application?
Hi O365info Team,
Currently, in my organization tenant, we do not have MFA enabled for all accounts. Only specific accounts have MFA enabled & in use. SSPR is disabled.
If i start the migration of legacy MFA to Authentication methods policy, does it affect those who do not have it currently? Also, does this migration enforce users to use MFA which currently do not have it enabled?
Thanks & Regards.
Nothing will happen to the existing per-user MFA and SSPR settings.
This will only migrate from legacy MFA and SSPR policies to converged Authentication methods policy.
We can migrate the policies and continue to use per-user MFA afterwards, correct?
Yes, you can keep using per-user MFA afterward.