Microsoft recommends to set up an MFA with a Conditional Access policy when you have…
Configure SPF record for Microsoft 365
Getting an email from an unauthorized sender with your domain’s address does not look good for your company. To protect your domain from spam and phishing attacks, you must set up SPF (Sender Policy Framework). In this article, you will learn how to configure SPF record for your Microsoft 365 domain.
Table of contents
What are SPF, DKIM, and DMARC?
DMARC, DKIM, and SPF are three email authentication methods. Together they help to prevent spammers, phishers, and other unauthorized parties from sending emails on behalf of a domain they do not own.
- Configure SPF record for Microsoft 365 (this article)
- Configure DKIM record for Microsoft 365
- Configure DMARC record for Microsoft 365
What is SPF record?
SPF is an essential part of your security strategy. By implementing SPF, you will reduce spam phishing attacks for your domain. It helps to protect your domain and improve to deliver legitimate emails.
An SPF record is a TXT record in the DNS (Domain Name System) zone of a domain. It contains a list of authorized mail servers or IP addresses that are allowed to send emails on behalf of that domain.
Important: It’s recommended to set up an SPF record, even if you don’t send emails from your domain name. In this case, the SPF record will look like v=spf1 -all. After that, no server has permission to send emails from that domain.
Get SPF record value Microsoft 365
The value of the SPF record syntax is identical to all the Microsoft 365 tenants.
The SPF value for the Exchange Online mail server should look like this:
v=spf1 include:spf.protection.outlook.com -all
Using SPF with “include” is an essential part of email authentication for Microsoft 365 to ensure that emails sent on behalf of your domain are legitimate and not forged. Instead of listing all the IP addresses or domains of Exchange Online servers in your SPF record, you can include the above SPF record.
We will show you how to see the value of the SPF record of your particular Microsoft 365 domain.
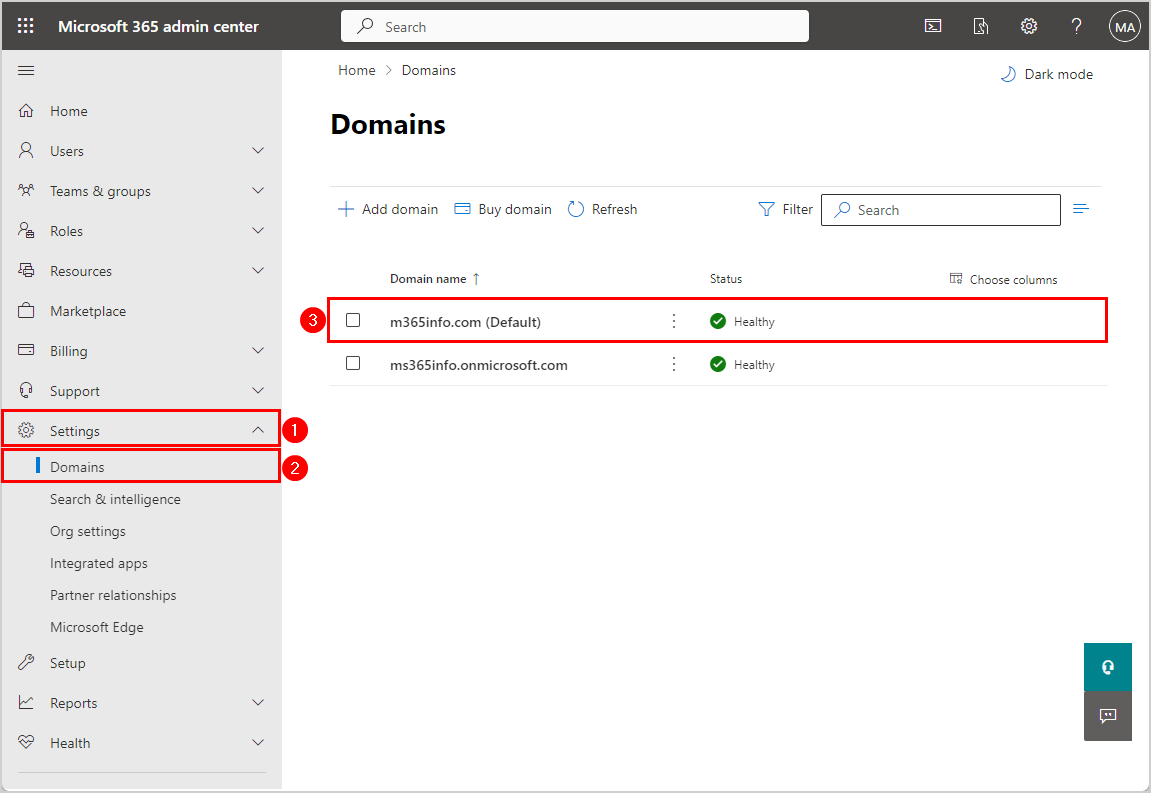
- Sign in to Microsoft 365 admin center
- Click on Settings > Domains
- Click on the domain you want to see the SPF record of.
In our example, it’s the domain m365info.com.
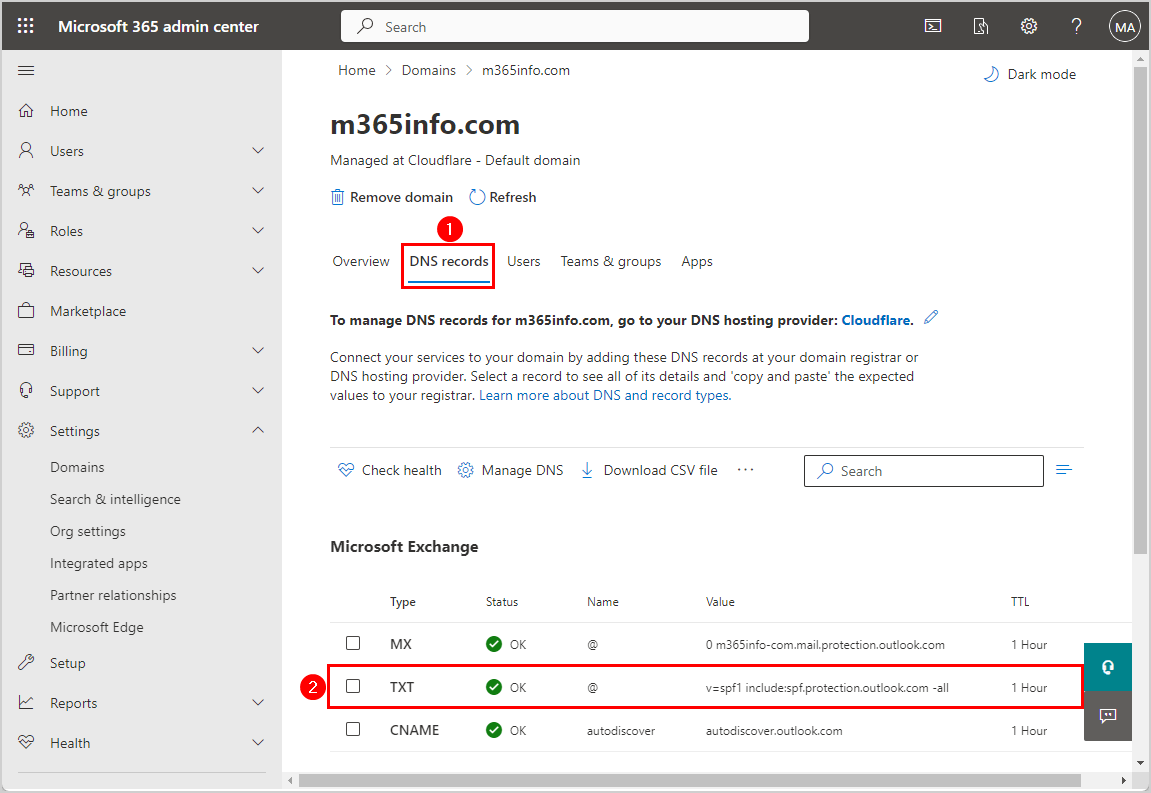
- Click on the tab DNS records
It shows all the information about the DNS records related to the Exchange Online services. Next to the type TXT record, you can find the SPF record value.
- Click on the TXT record
It shows you set up the record correctly for the domain.
- The TXT value is v=spf1 include:spf.protection.outlook.com -all
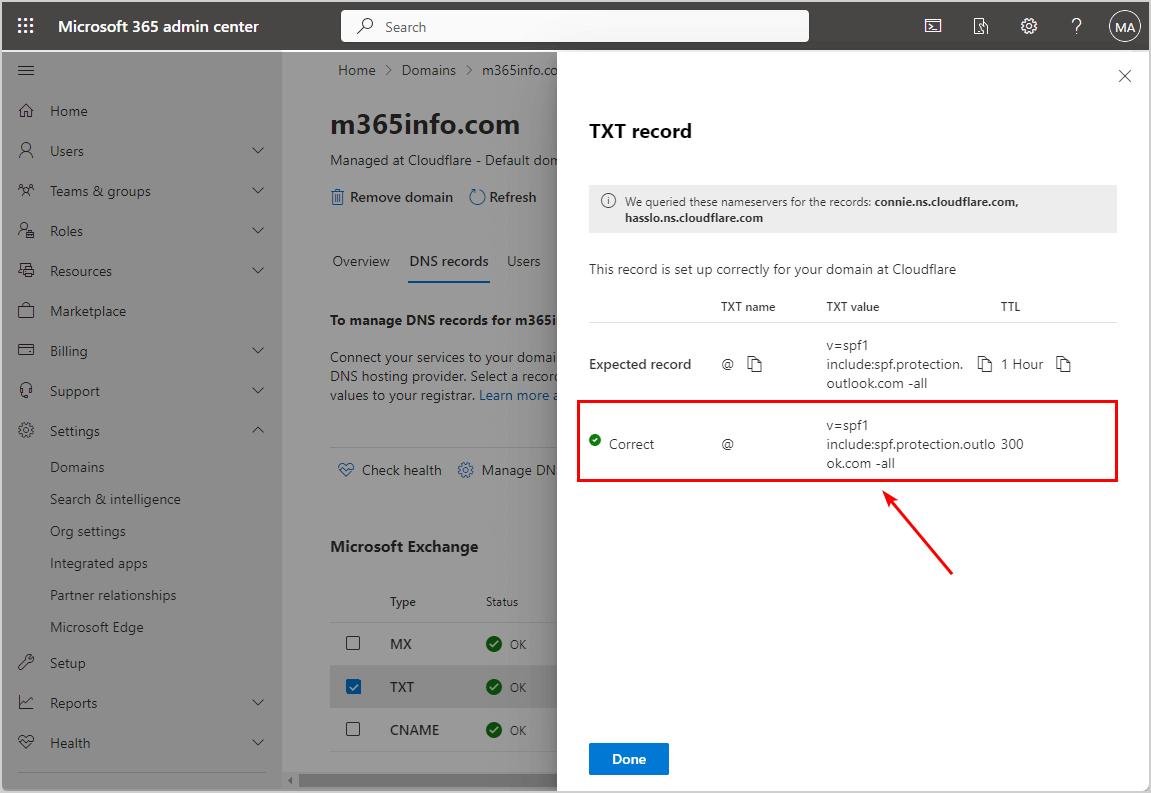
In this example, “spf.protection.outlook.com” is the domain containing the SPF information for all the Exchange Online servers. The -all at the end is the SPF qualifier, indicating that any server not matching the specified SPF policy should fail SPF authentication (e.g., emails from unauthorized servers should be treated as suspicious).
Create SPF record for multiple mail servers
Some have Exchange Online as mail infrastructure and another mail server that will send an email on behalf of the domain name. In that case, you need to show that your organization’s domain name is using two different entities:
- Exchange Online mail server
- Another mail server hosted in the organization
Let’s say that your mail infrastructure is hosted on Microsoft 365, and you have an On-Premises mail server with the public IP address 212.25.80.239. So you need to extend the original SPF record with another mail server, such as:
- mx (MX records)
- ip4 (IPv4 addresses)
- ip6 (IPv6 addresses)
You need to use the original syntax of the Microsoft 365 SPF record and add extra information for the On-Premises mail server with the public IP address 212.25.80.239.
Add the below information to the SPF record.
ip4:212.25.80.239The SPF record syntax will look like the below example.
v=spf1 ip4:212.25.80.239 include:spf.protection.outlook.com -allThe updated SPF record includes all the information about both servers for your domain.
Possible problems with SPF record
If the SPF record for your domain fails, it means that it’s not protected, and the email might be forged or unauthorized.
There are several outcomes concerning SPF record:
- No SPF record: The organization does not use SPF record.
- More than one SPF record: This is a common mistake where the DNS includes two or more SPF records. The outcome will give unknown results because the SPF record is set wrongly. Some mail servers will relate only to one SPF record, and other mail servers will refuse to accept mail.
- SPF record configured improperly: SPF record is based on very strict syntax rules that dictate how to construct the SPF record. Sometimes, the SPF record includes a syntax error, and the outcome is unknown results.
- SPF record that doesn’t include information about all the organization’s mail servers: This is when you have a hybrid environment based on two separate mail (Exchange Online and Exchange on-premises) infrastructures.
All these situations could lead to a problem where the external mail server will block mail sent by a user from your organization.
Note: You need to configure an SPF record for Microsoft 365, even if you don’t send emails from your domain name. Change the SPF record to v=spf1 -all, and no server will have permission to send emails.
Publish SPF record on public DNS
After we get or create the value for the SPF record in a Microsoft 365 environment, we must add the required SPF record to our public DNS server. The SPF record is implemented as a TXT record.
Note: If you use another DNS management infrastructure (like GoDaddy, etc.), the interface will differ, but the concept stays the same.
- Sign into your provider (Cloudflare) and go to the DNS records
- Open TXT
- Add the SPF record v=spf1 include:spf.protection.outlook.com -all under Content (required)
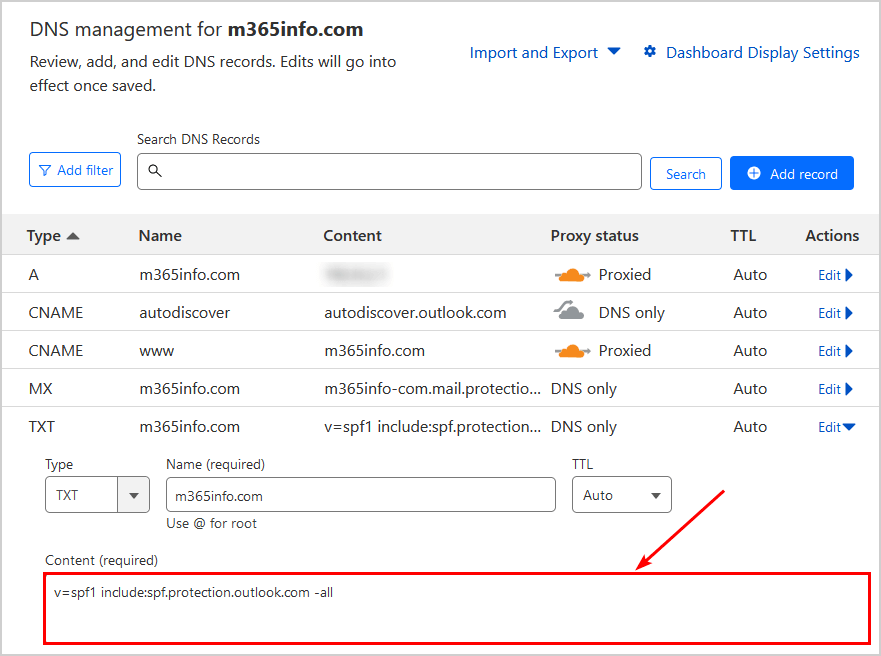
Now that you added the SPF record for Microsoft 365, we will check if SPF is correctly published in the next step.
Verify SPF record
Let’s check if you set up the SPF record correctly in the DNS and doesn’t include any errors. We will show you different methods to verify your SPF.
View SPF record in Windows
How to use the command prompt to check SPF record:
- Click on Start on Windows
- Open the app Run
- Type cmd
- Use the below syntax
nslookup -q=txt domain name- Fill in the domain name and press Enter
nslookup -q=txt m365info.comYou will see the following results. In our case, the domain m365info.com includes one TXT record. The value of the SPF record is v=spf1 include:spf.protection.outlook.com –all.
C:\>nslookup -q=txt m365info.com
Server: comp
Address: 212.25.80.239
Non-authoritative answer:
m365info.com text =
"MS=ms62326082"
m365info.com text =
"v=spf1 include:spf.protection.outlook.com -all"Check SPF record with Kitterman
Validate with the Kitterman SPF Record testing tool:
- Enter the domain name m365info.com
- Click Get SPF Record (if any)
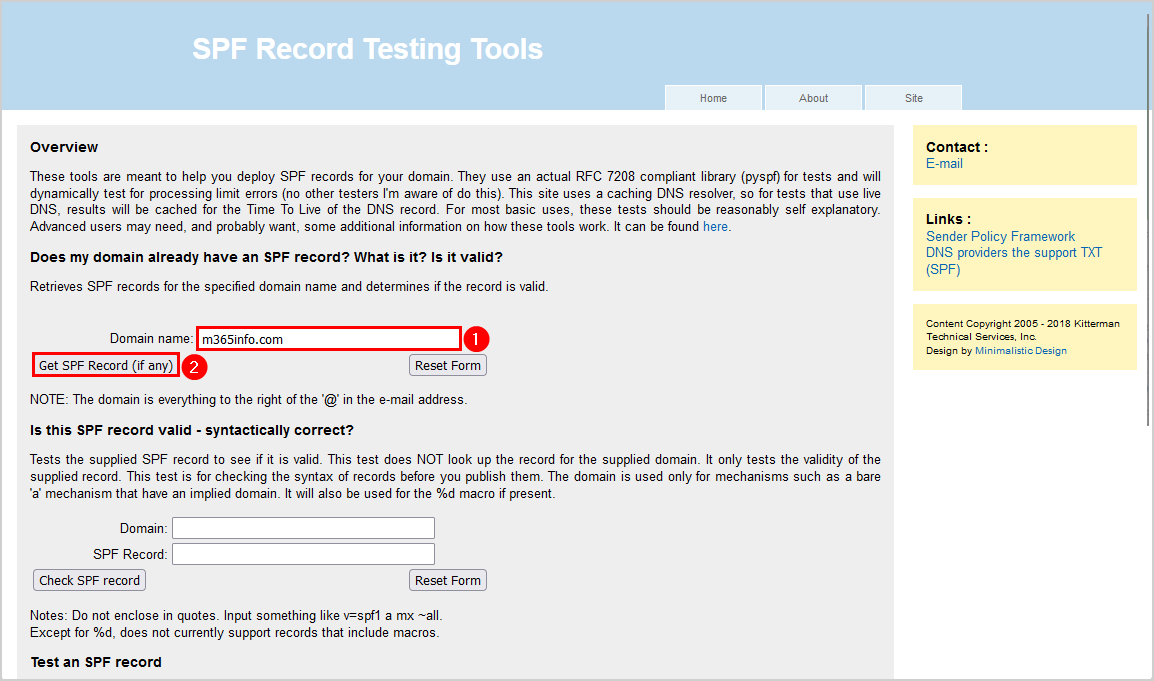
The SPF results outcome will look like the below example.
- It found the SPF syntax correctly, and the SPF record passed the validation test
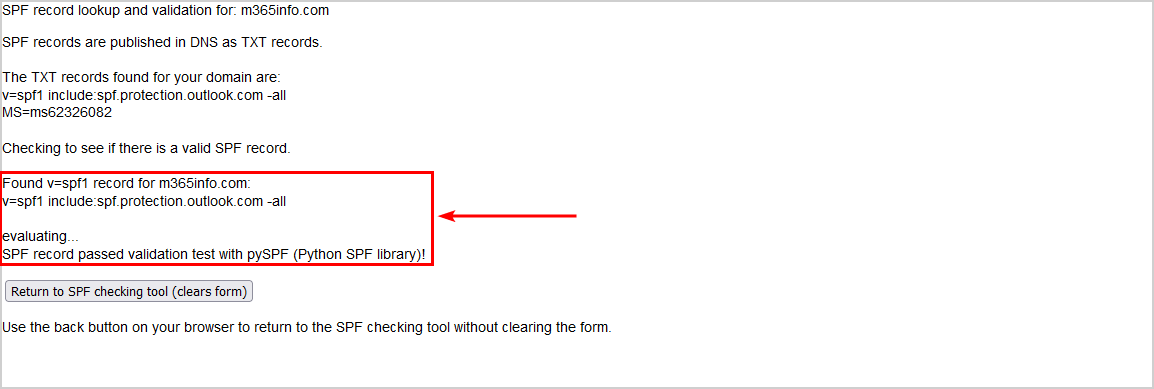
Note: Kitterman allows you to test the SPF record with the Check SPF record option to see if it’s valid before you publish it.
Check SPF record with MxToolBox
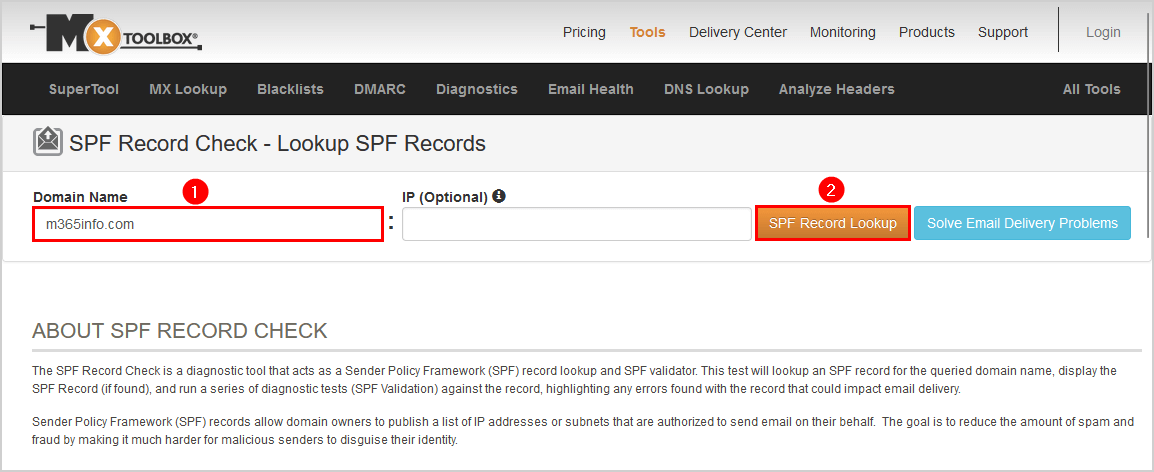
Verify the SPF using the MxToolbox SPF Record Check:
- Type the domain name m365info.com
- Click SPF Record Lookup
The result shows that the SPF verification test is completed successfully. The status information about the m365info.com SPF record is green.
As you can see below, the Test SPF Multiple Records results show Less than two records found. This is correct because we don’t use more than one SPF record.
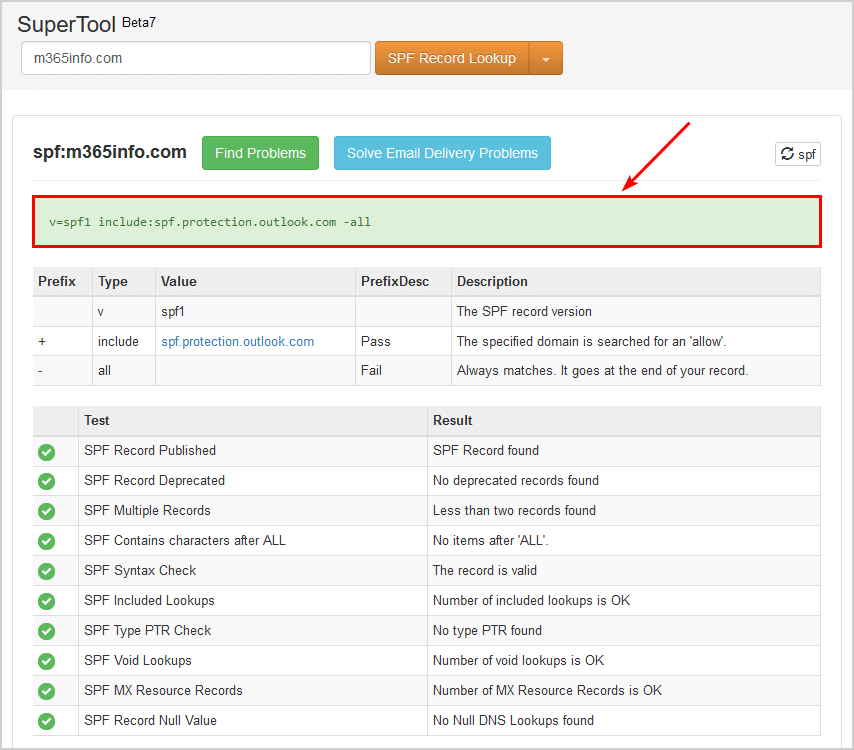
Note: MxToolBox has the SPF Wizard tool to generate an SPF record for your domain before you publish it.
Check SPF record with Dmarcian
Check your SPF record with Dmarcian SPF Surveyor:
- Enter your domain
- Click Survey Domain
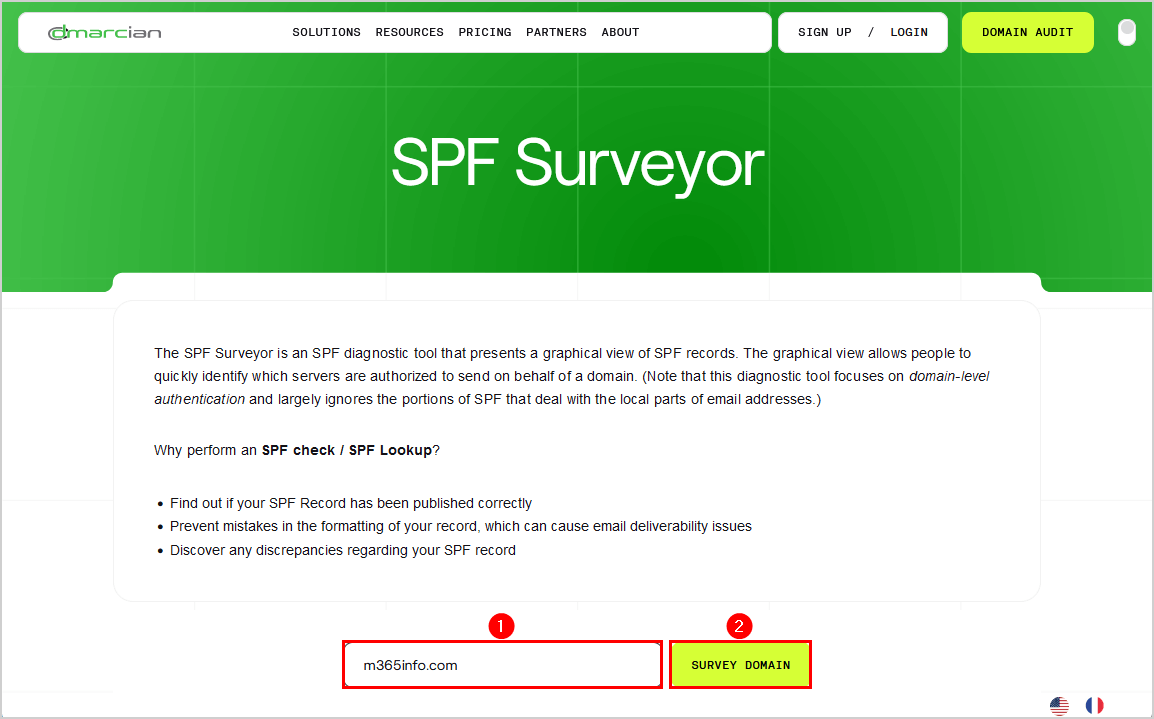
Scroll down to see the results and information about the SPF record.
- The verification test successfully extracts the content within the include:spf.protection.outlook.com record
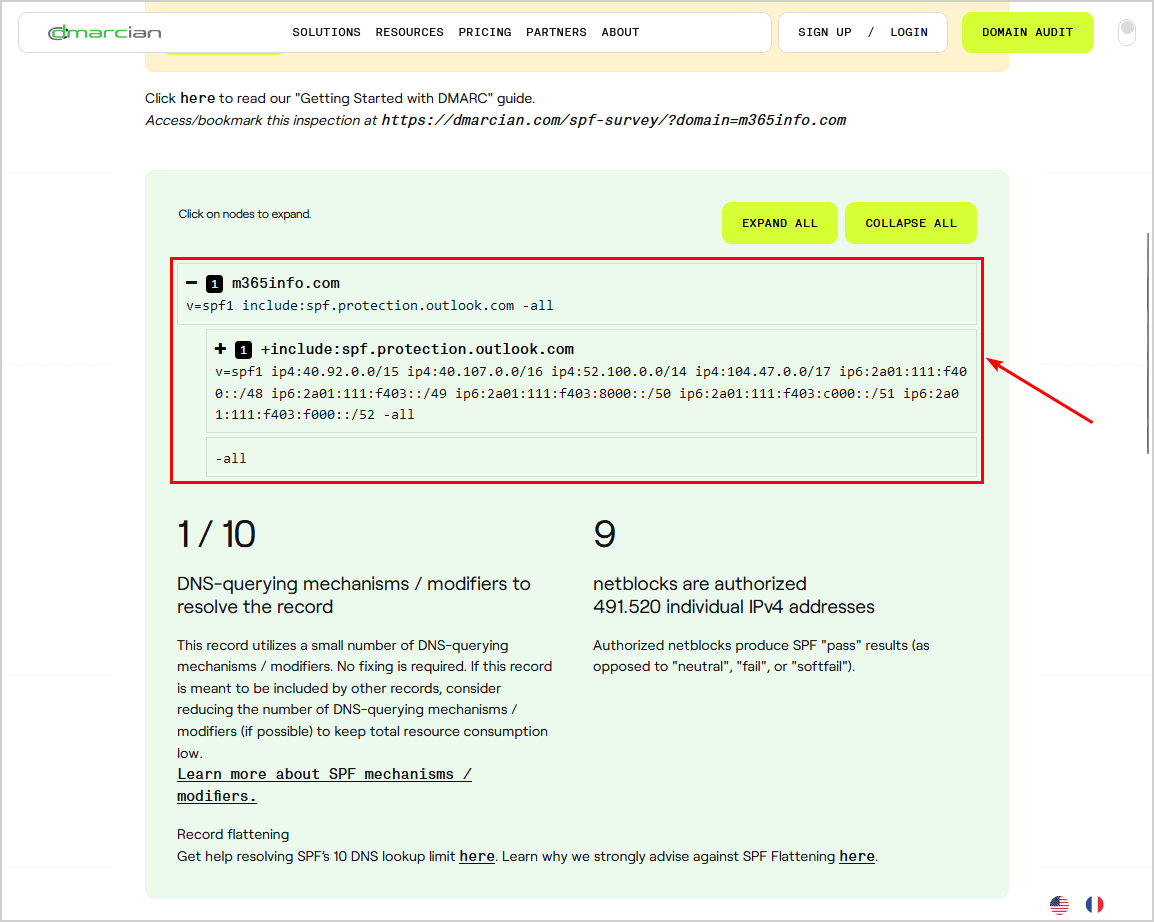
Note: Dmarcian shows additional information about the include mechanism, which is very helpful.
Note: It is not enough to check your SPF record with one of the above methods, as they will not test the SPF authentication in the sent email. Therefore you need to verify the SPF authentication with Gmail and CheckTLS.
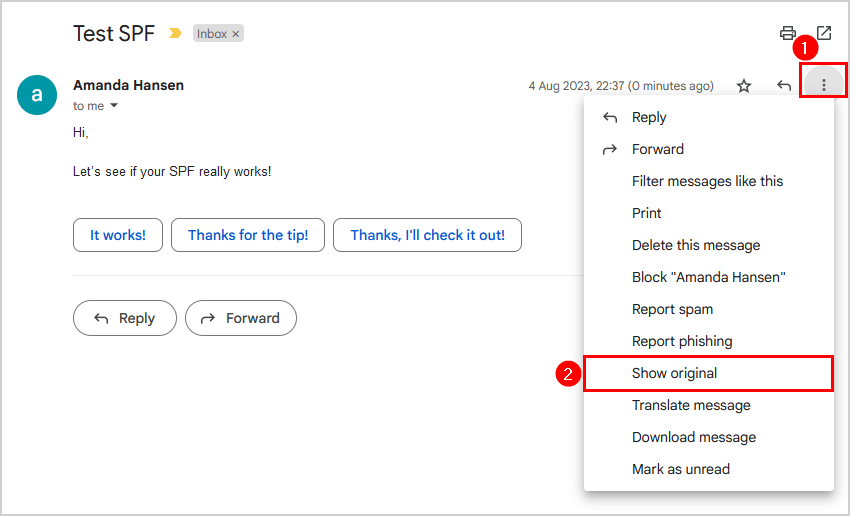
Verify SPF with Gmail
We want to verify the email messages sent by our organization to the recipients include SPF authentication.
To test SPF, we will send an email from an organization sender to an external recipient with a Gmail address.
In our example:
- Organization sender: amanda.hansen@m365info.com
- External recipient: bob.green@gmail.com
Go to the recipient inbox to view the email header:
- Open the email
- Click the three dots
- Click Show original
The information about the SPF signature shows:
- PASS with IP
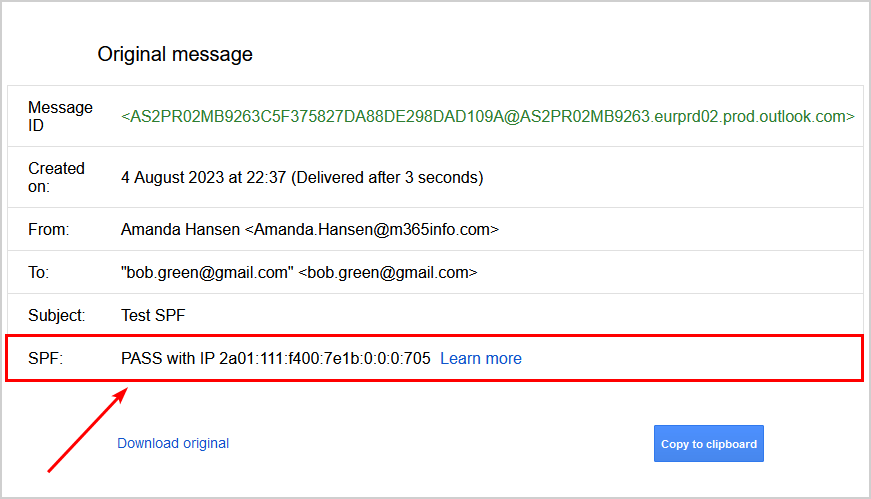
Note: The Gmail original message doesn’t show if SPF failed the test but removes the entire SPF row. So when you can’t find SPF in the original message, it means you did not set it up, or it’s incorrectly configured.
Verify SPF with CheckTLS
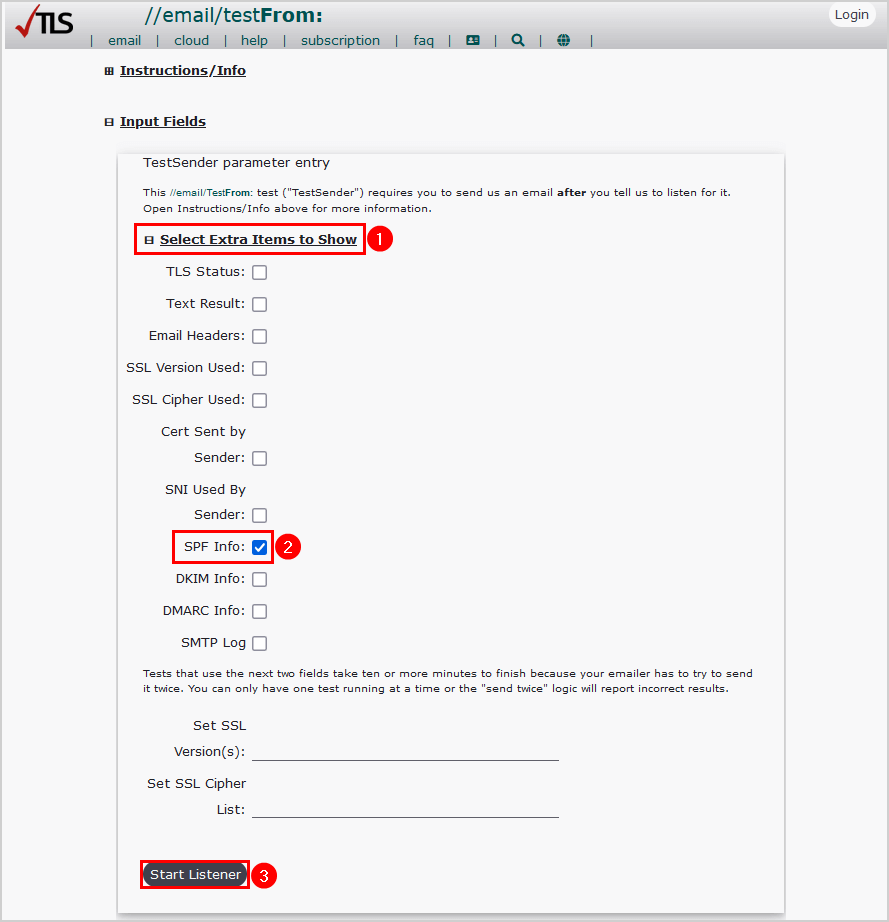
Test your SPF authentication in the message header with the CheckTLS tool:
- Go to CheckTLS
- Click on Select Extra Items to Show
- Select SPF Info
- Click Start Listener
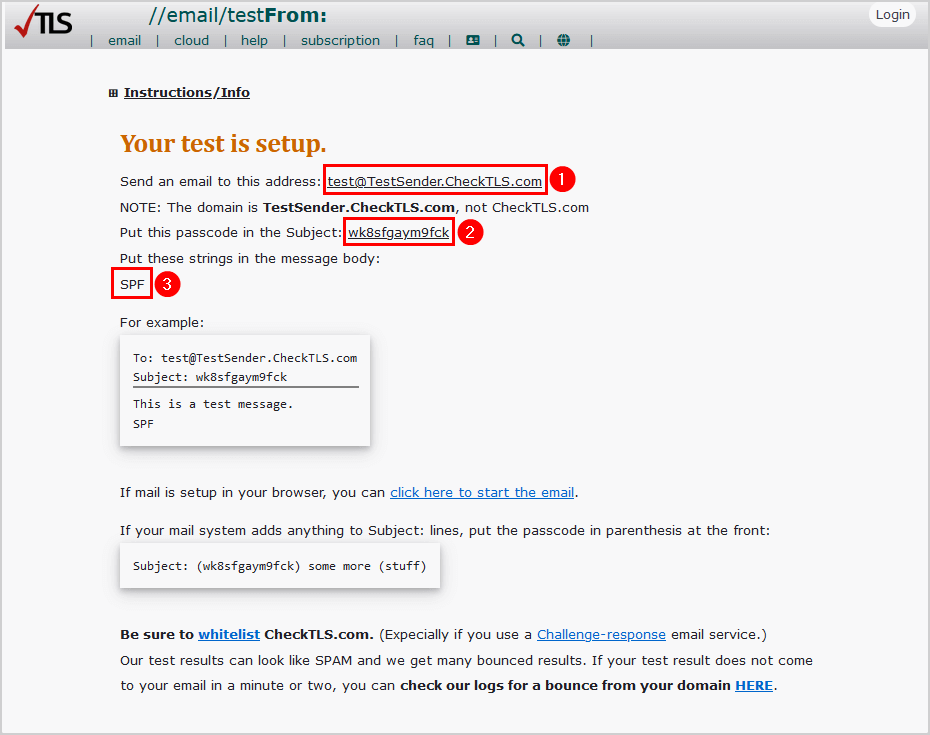
In our example, we will send an email from Amanda.Hansen@m365info.com.
How to send a test email:
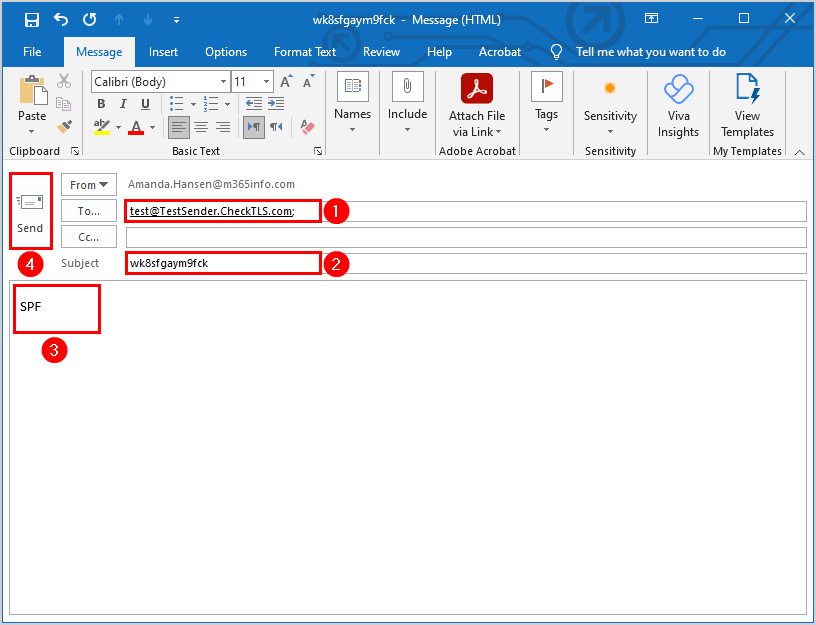
- Copy and paste the address to test@TestSender.CheckTLS.com
- Copy and paste the passcode in the subject of the email
- Type SPF in the message
- Create a new email with the required information
- Send the test email
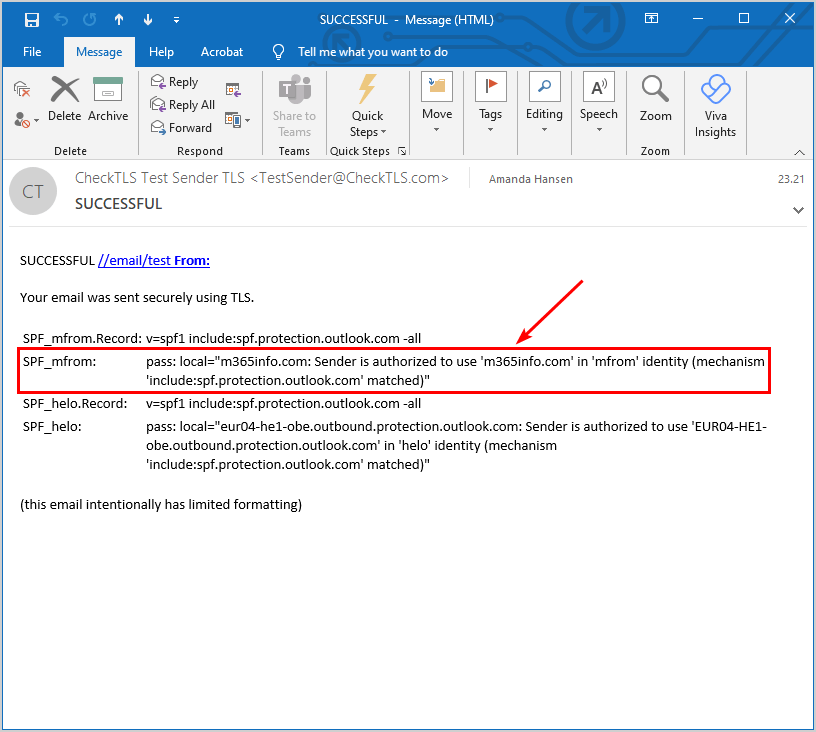
After you send the email, you need to check your inbox because you will get an email from CheckTLS.
- Open the email from CheckTLS to see the SPF report
- The results show SPF_mfrom: pass, which means that the email was sent successfully
Frequently Asked Questions (FAQ)
What is SPF?
SPF stands for Sender Policy Framework. The SPF record is a type of DNS (Domain Name System) record that specifies which mail servers are authorized to send emails on behalf of a specific domain. It is an email authentication method to detect and prevent email spoofing.
Why do I need to set up the SPF record?
SPF is a protocol that helps to reduce spam via email for your domain name. If you don’t set up the SPF record, you ask for trouble. Your legitimate emails could be delayed, rejected, or go to the recipient’s junk folder. Therefore you should always configure the SPF record, even if you don’t send emails from your domain. It increases the email message reliability and authenticity of incoming email messages for your organization’s domain.
What is the default SPF record for Exchange Online/Microsoft 365?
The value of the SPF record is not unique and is identical to all Microsoft 365 domains (v=spf1 include:spf.protection.outlook.com).
What information is included in the SPF record?
The SPF record contains information about the authorized mail servers or IP addresses that can send emails on behalf of a specific domain.
Conclusion
You learned how to configure the SPF record for your Microsoft 365 domain. Get your SPF record for the Exchange Online server in the Microsoft 365 admin center. Then check the SPF record in the command prompt, Kitterman, MxToolBox, or Dmarcian, to verify it’s published correctly. Remember to test the SPF authentication by sending an email and testing the message headers with Gmail and CheckTLS.
Did you enjoy this article? You may also like How to simulate spam mail. Don’t forget to follow us and share this article.

This Post Has 0 Comments