The subject of E-mail Message attachment manifests itself in two main scenarios: Malware scenario –…
Manage E-mail attachment policy in Office 365 – Part 3#4
In the current article, we will review how to enforce an E-mail attachment policy by using Exchange Online transport rule.
The example that we will review in the current article is – an E-mail attachment policy, that stop E-mail messages that include an attachment with a specific file extension.
Table of contents
Manage E-mail attachment policy in Office 365 | The article series
The article series include the following articles:
- Manage E-mail attachment policy in Office 365 – Part 1#4
- Manage E-mail attachment policy in Office 365 – Part 2#4
- Manage E-mail attachment policy in Office 365 – Part 3#4
- Manage E-mail attachment policy in Office 365 – Part 4#4
Block E-mail that has an attachment with a specific file extension
The following option as the name implies, enable us to choose the specific file Extension that will be blocked.
In this scenario we are “taking” the responsibility from the mail client such as OWA and Outlook and use the Exchange Online server for enforcing the E-mail attachment file extension policy.
The main disadvantages of this method are:
- We will need to prepare a list of file extensions that we want to block and update this list from time to time in the Exchange Online transport rule in case that we want to add a “new file extension”
- The Exchange Online transport rule will relate only to the file name extension and not the true file type (MIME type).
For example – in the case that we define an E-mail message attachment rule that will block mail attachment that uses the file name extension *BAT, each E-mail message that will include this attachment will be blocked.
However, in case that a hostile element changes the filename extension from BAT to PDF, for example, the Exchange Online transport rule will not block the E-mail message.
Attached some quotation from Microsoft public articles:
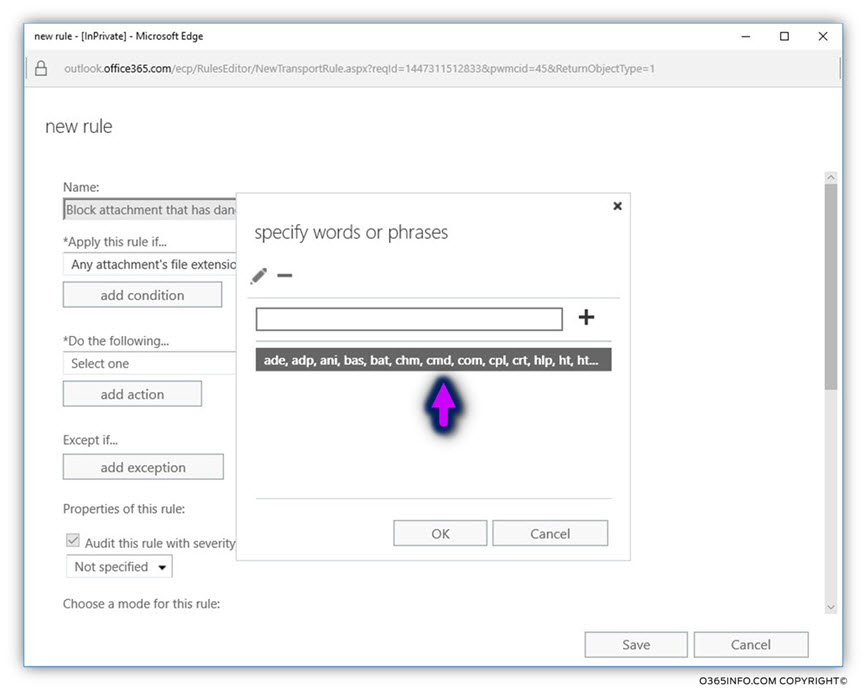
For increased protection, we also recommend using Transport rules to block some or all of the following extensions: ade, adp, ani, bas, bat, chm, cmd, com, cpl, crt, hlp, ht, hta, inf, ins, isp, job, js, jse, lnk, mda, mdb, mde, mdz, msc, msi, msp, mst, pcd, reg, scr, sct, shs, url, vb, vbe, vbs, wsc, wsf, wsh. This can be done by using the Any attachment file extension includes these words condition.
To be able to create the required rule, use the following steps:
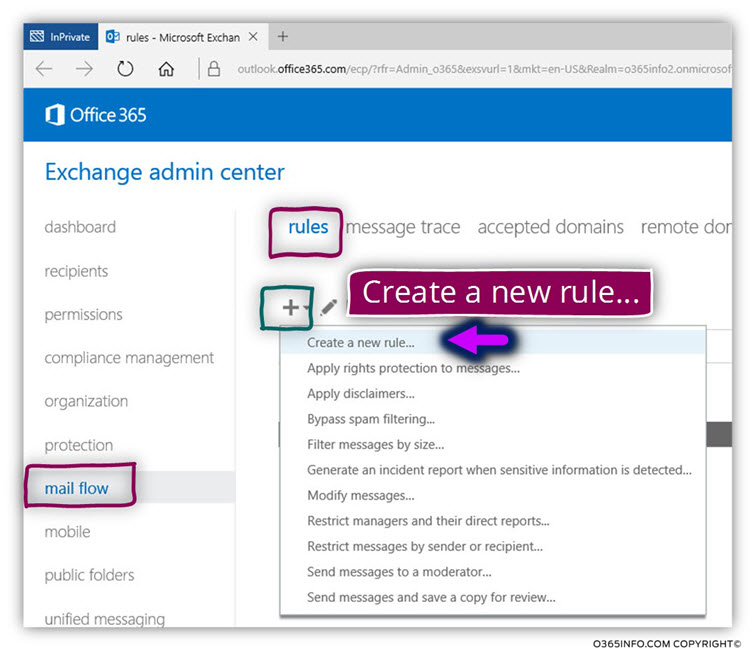
Log in to Exchange admin center
- On the left bar menu, choose – mail flow
- On the top bar menu, choose – rules
- Click on the plus sign
- Choose – Create a new rule…
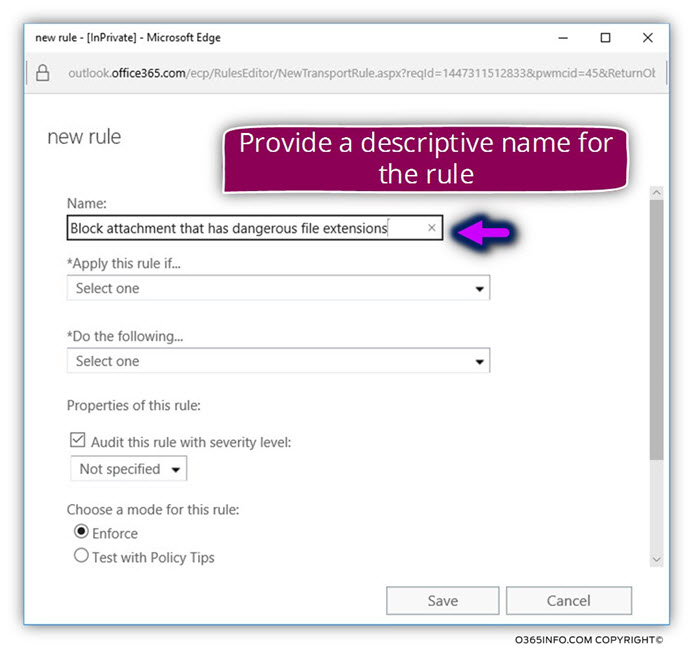
In the name: text box, add a descriptive name for the rule that will be created.
In our specific scenario, we will use the name – Block attachment that has dangerous file extinctions
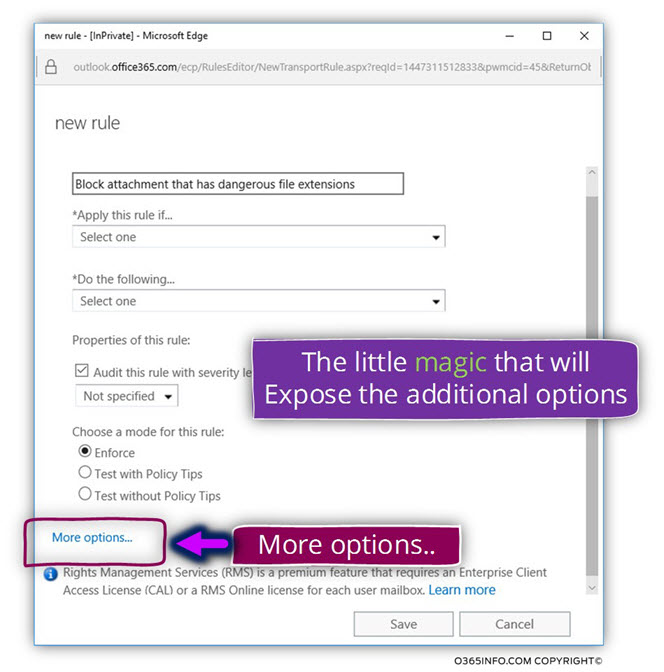
On the bottom part of the window, click on the option – More options…
(using the More Option… menu is needed for displaying all of the available mail attachment rule options).
Under the *Apply this rule if…. choose the menu – Any attachment… in the sub menu that appear, choose the menu – file extension includes these words.
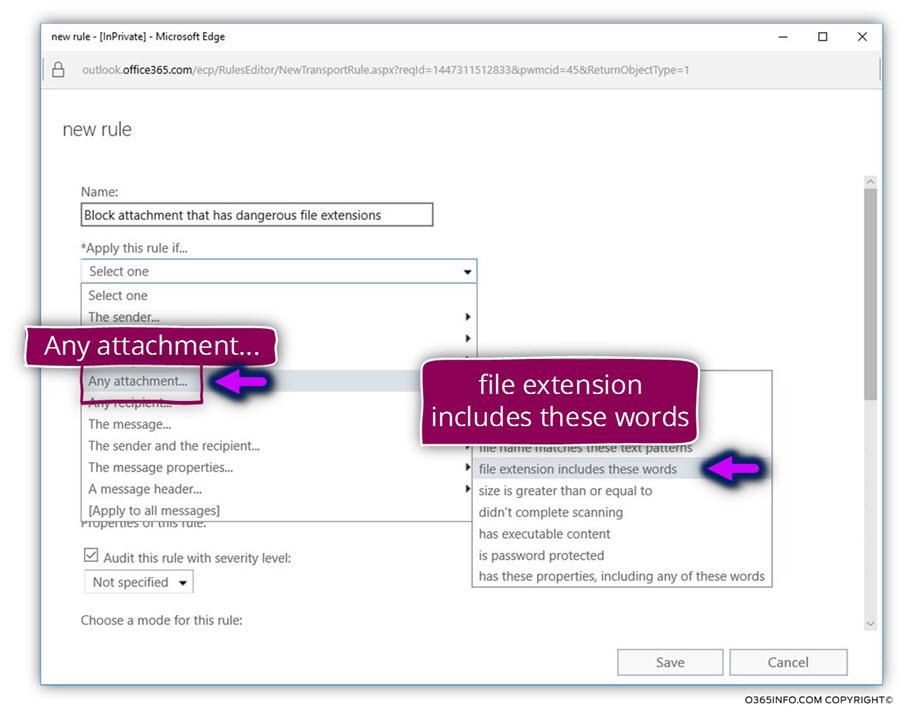
In the text box – specify words or phrases and the name of the file extension that you want to block such as – ade, adp, ani, bas, bat, chm, cmd, com, cpl, crt, hlp, ht, hta, inf, ins, isp, job, js, jse, lnk, mda, mdb, mde, mdz, msc, msi, msp, mst, pcd, reg, scr, sct, shs, url, vb, vbe, vbs, wsc, wsf, wsh
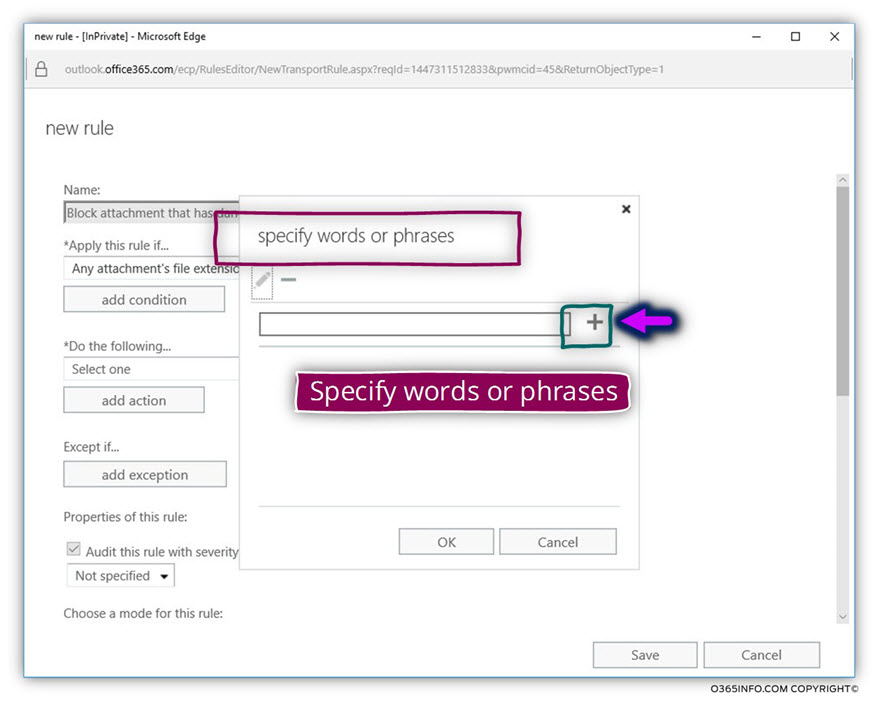
Click on the plus icon to add the required file extensions
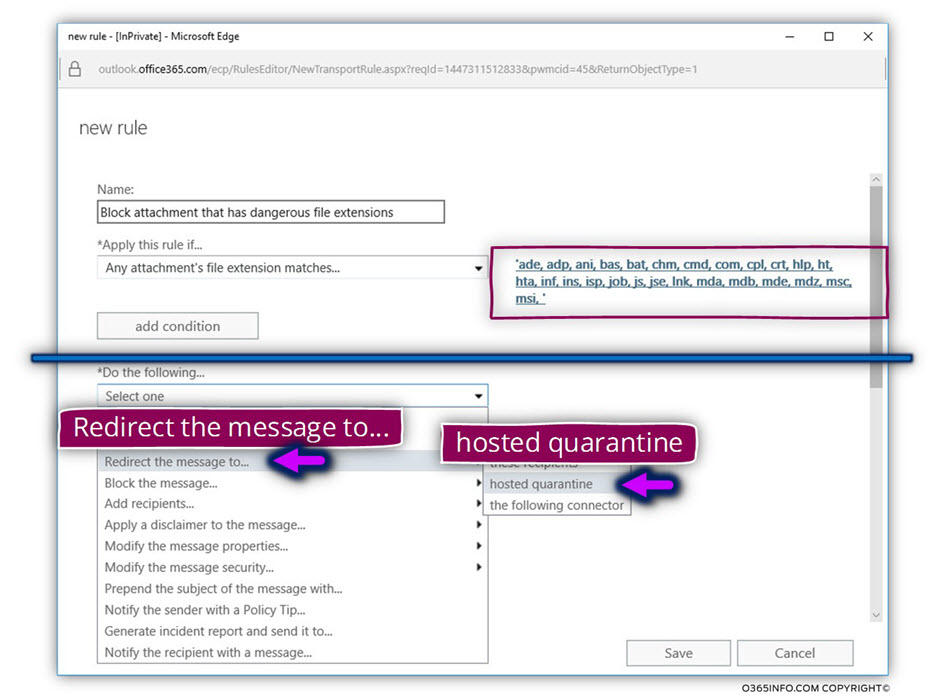
The “action” part of the rule
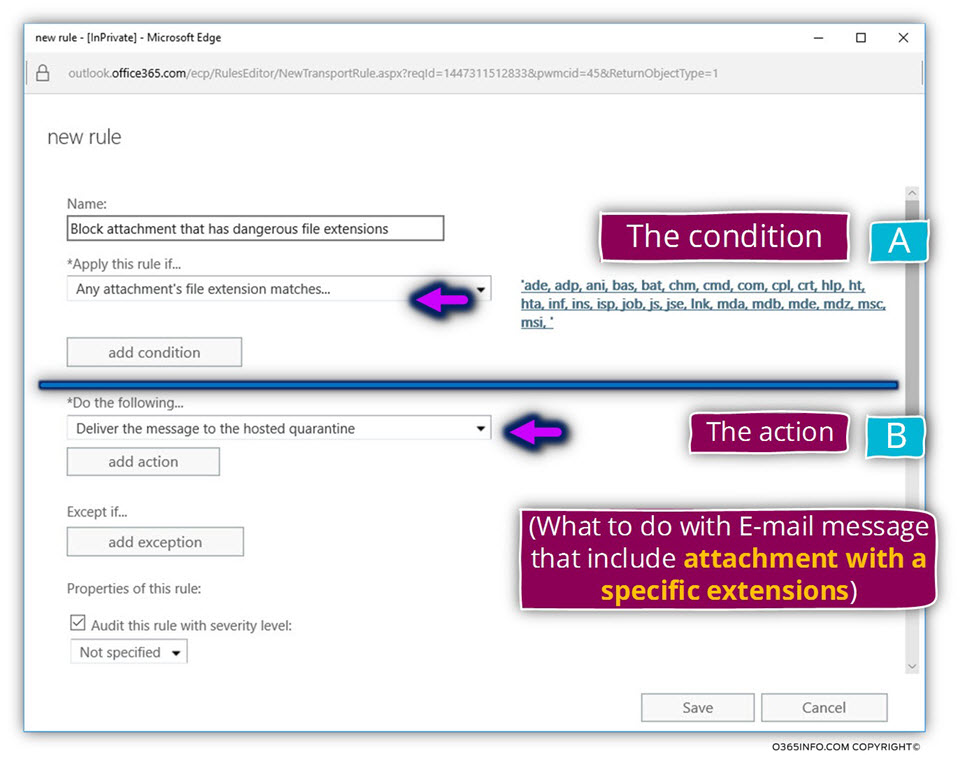
In this part, we decide what is the specific action that will be implemented or enforced, in case that Exchange Online “capture” a specific E-mail message with an attachment that is not a complaint with our E-mail message attachment policy.
In our specific scenario, we decide to send the E-mail message to quarantine (described as Hosted quarantine).
In the section – Do the following… choose the menu Redirect the message to…. And, in the sub menu that appear, choose the menu hosted quarantine
In the following screenshot, we can see results
Next article
In the next article, we will review how to create an Exchange Online transport rule, that will enforce an E-mail attachment policy on E-mail messages by “stopping” E-mail message that that includes a password protected attachment.
Hi, Tks for the article ! It’s very helpfull. One doubt, i have to add the extension one by one or can i put all the extension list separated by coma ? Like your example… tks !