In the current article, we will review the required configuration settings for implementing Force TLS…
Configure Force TLS in Exchange Online environment | Settings of inbound connector | Part 7#12
In the current article, we will review the required configuration settings for implementing Force TLS in Exchange Online based environment. In our specific scenario, we need to configure the Force TLS option for the “incoming mail flow”.
The meaning is – mail that sent from external mail server to the Exchange Online server that represent a particular domain name.
The Force TLS configuration setting will be applied to the inbound connector.
Table of contents
Scenario requirements | Exchange Online | incoming mail
The complete scenario description appears in the previous article
In this article, we will implement the following part from the complete scenario:
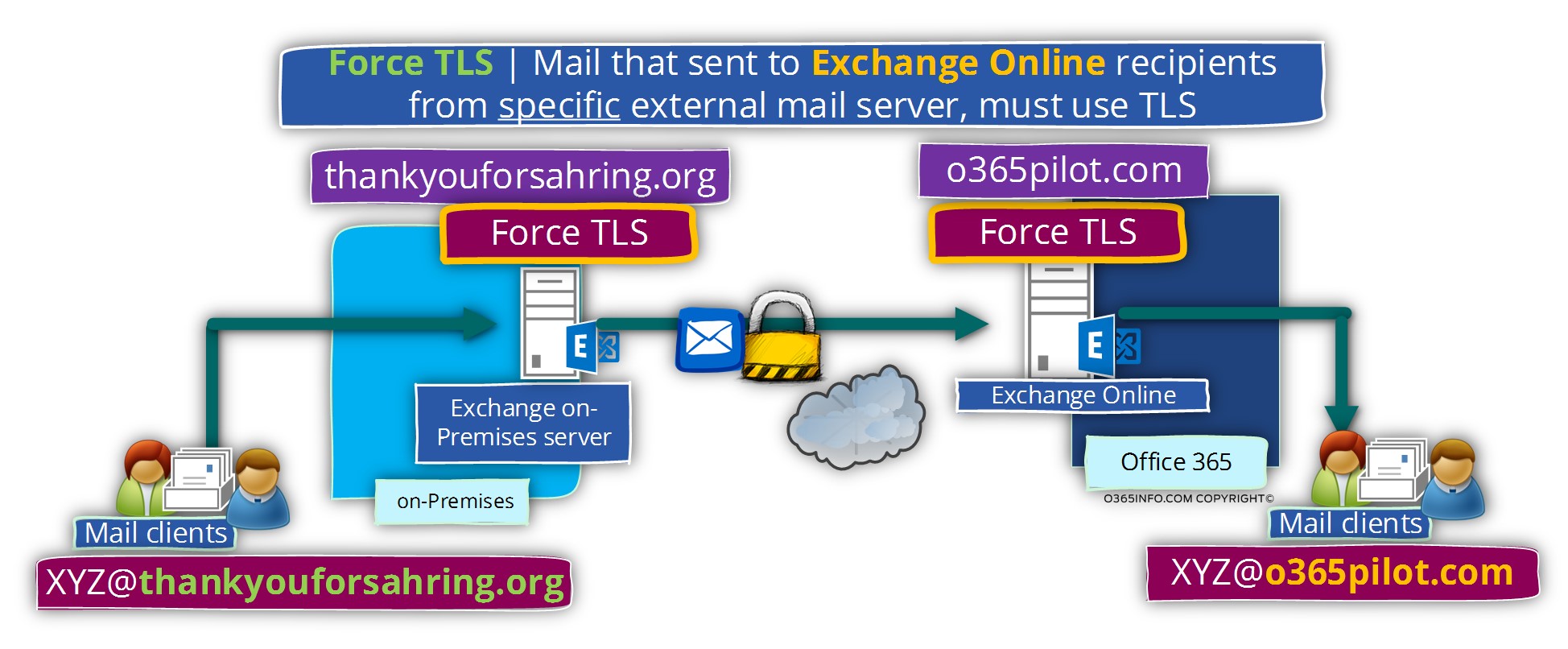
E-mail messages that sent from a specific external mail server (Exchange on-Premises in our scenario, which represent a specific domain name) to – an Exchange Online recipients which hosted at Exchange Online, will be sent by using a secure communication channel meaning TLS.
In additional requirement is that the Exchange Online server, will have the ability to identify the particular external mail server that in our scenario represent an organization that uses the domain name – o365pilot.com
Each time that the Exchange Online that represent the domain name o365pilot.com is addressed by the mail server of the organization A, that represents the domain name – thankyouforsharing.org, the Exchange Online will “agree” to accept the mail only when the following requirements will be fulfilled:
- The mail communication will need to be implemented by using encrypted communication line (TLS).
- The “external server” (Exchange on-Premises) must support TLS.
- The “external server” (Exchange on-Premises) must identify himself using a trusted public certificate.
- The public certificate of the “external server” (Exchange Online) must include a specific domain name that will approve the identity of the mail server – o365pilot.com
General information
It’s important to understand that when using Exchange Online inbound mail connector, we can define the parameter of a specific external server but, not the parameters of the destination domain that is hosted at Exchange Online.
For example, in our scenario the Exchange Online host the domain name – thankyouforsharing.org
In case that the Exchange Online host additional domain for the specific Office 365 tenant, the inbound connector “rules” will be applied for each of the other domains that are configured for the particular Office 365 tenant.
In the following diagram, we can see an illustration of the mail flow scenario. Each mail that is sent by the external mail server that represents the domain thankyouforsharing.org, must be sent over a secure communication channel using TLS.
Creating the required configuration for Force TLS | Exchange Online | Outbound connector
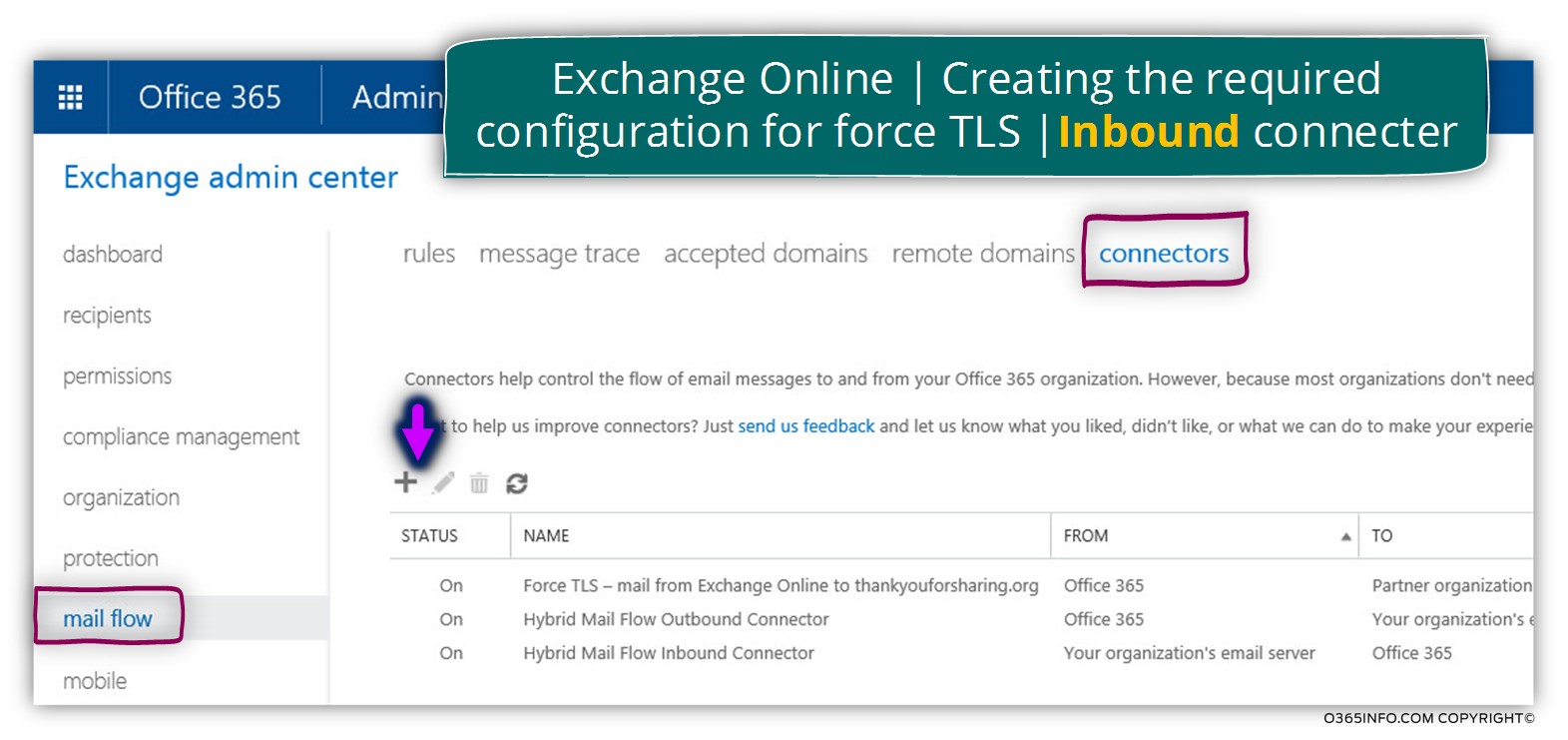
To be able to fulfill the requirement in which, each E-mail message sent by an external mail server that represents the domain name – thankyouforsharing.org to Exchange Online recipients (o365pilot.com) will be encrypted, we will create a new inbound mail connector
- Login to Exchange Online admin center
- On the left bar menu, choose the mail flow menu
- On the top bar menu, choose the connectors menu
- Click on the plus sign to create a new mail connector
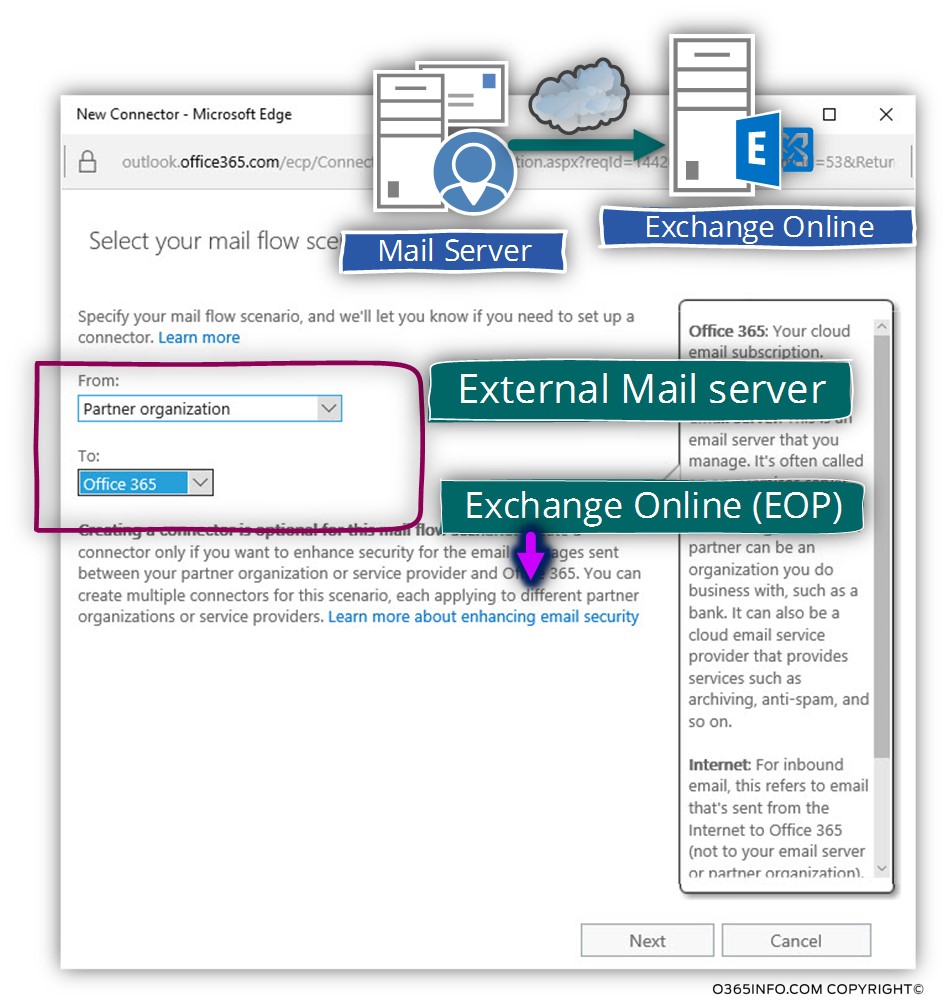
We need to configure the mail flow, of the mail that sent from the external mail server to the Exchange Online server.
In the From: option box choose – Partner organization
In the To: option box choose – Office 365
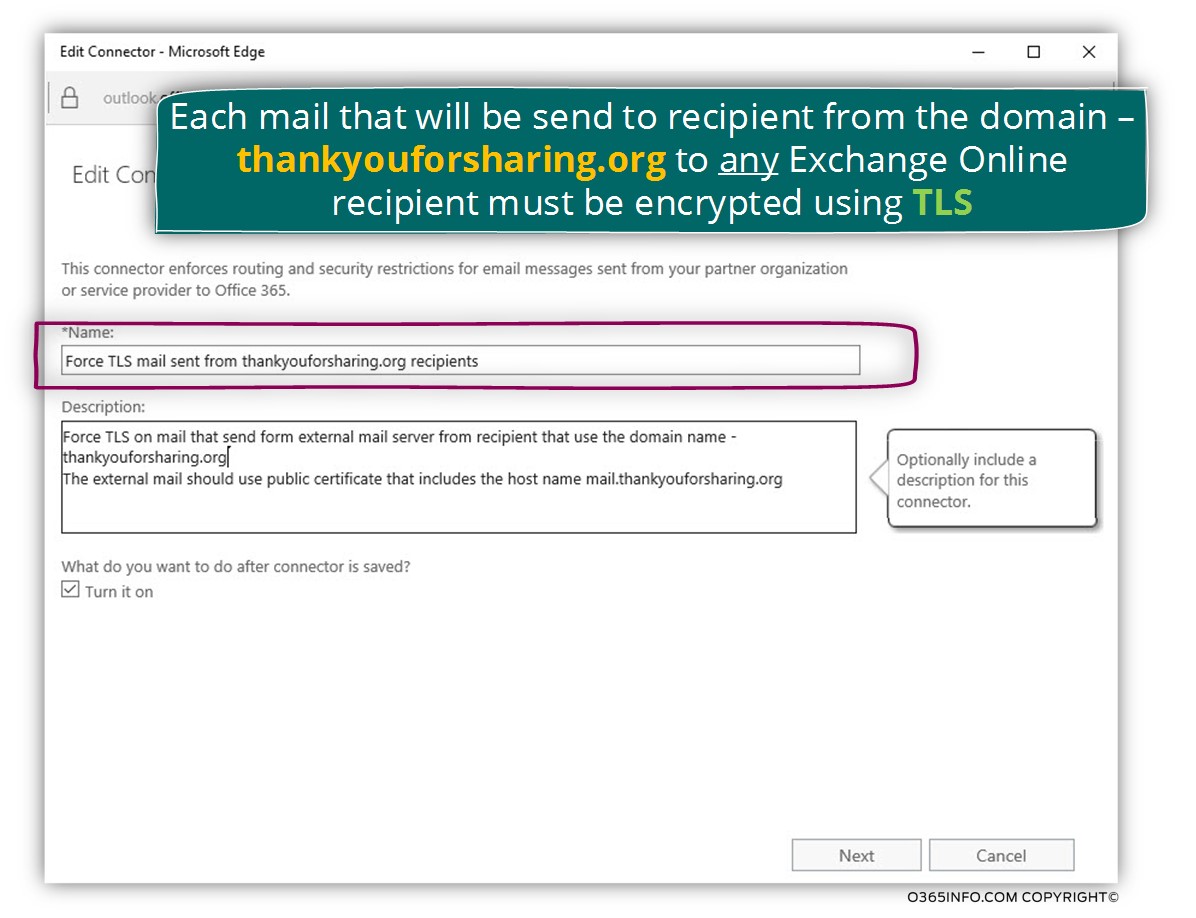
In the *name text box, write the name that is suitable to your needs.
My recommendation is to use a descriptive name + description so in the future, in the case of a troubleshooting process, it would be easy to understand the purpose of a specific mail connector.
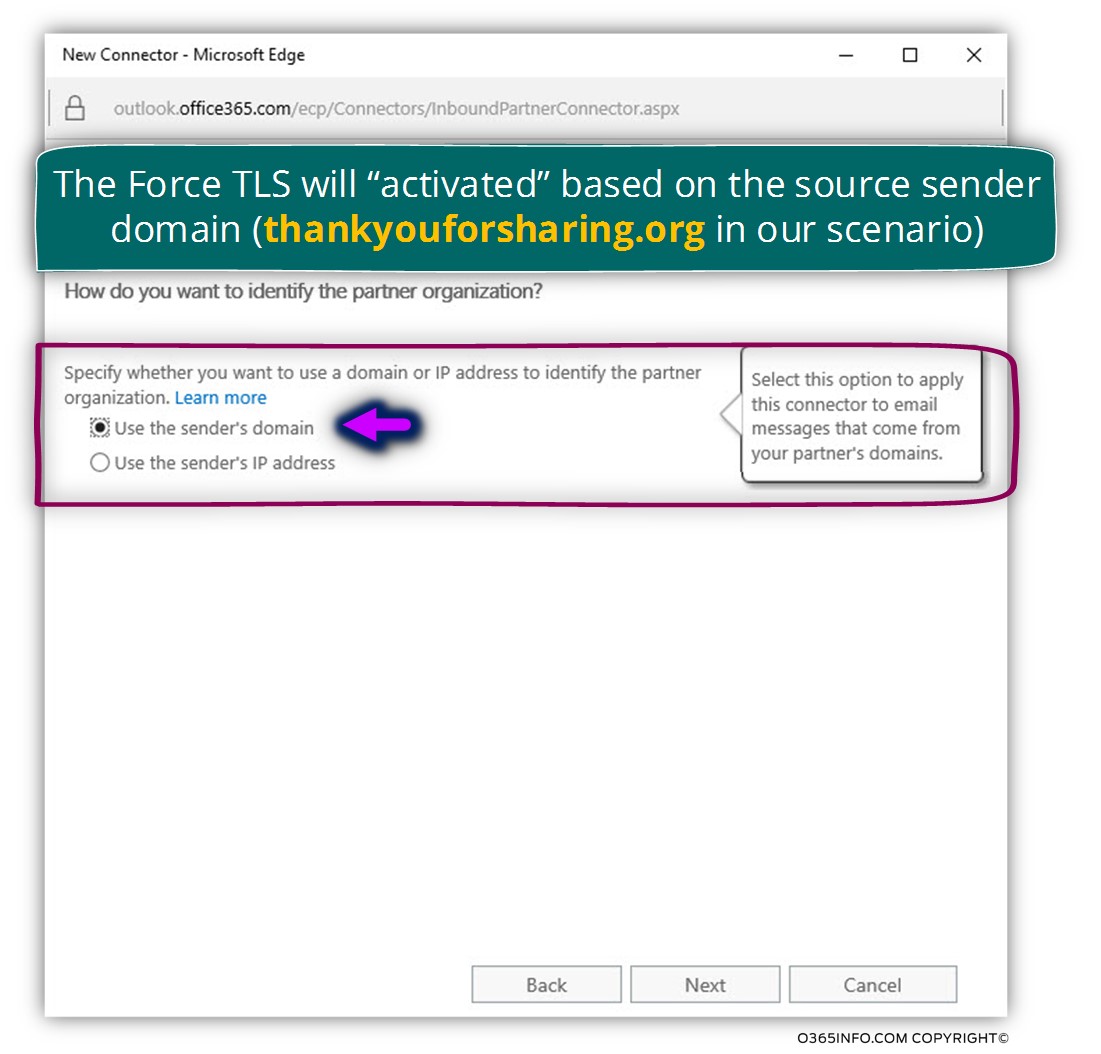
In this screen, we define the parameter which will activate the Exchange Online incoming connector
We can choose from one of the following options:
- Use the sender’s domain – when we select this option, Exchange Online will use the specific incoming mail connector in case that the E-mail message that sent from an external recipient include a specific or a predefined domain name
- Use the sender’s IP address – when we select this option, Exchange Online will use the specific incoming mail connector in case that the E-mail message is sent from the external mail server that is represented by a specific IP address.
In our specific scenario, we will “activate” the incoming mail connector (by choosing the option to use the sender’s domain) when the E-mail message to the external recipient will include the domain name – thankyouforsharing.org
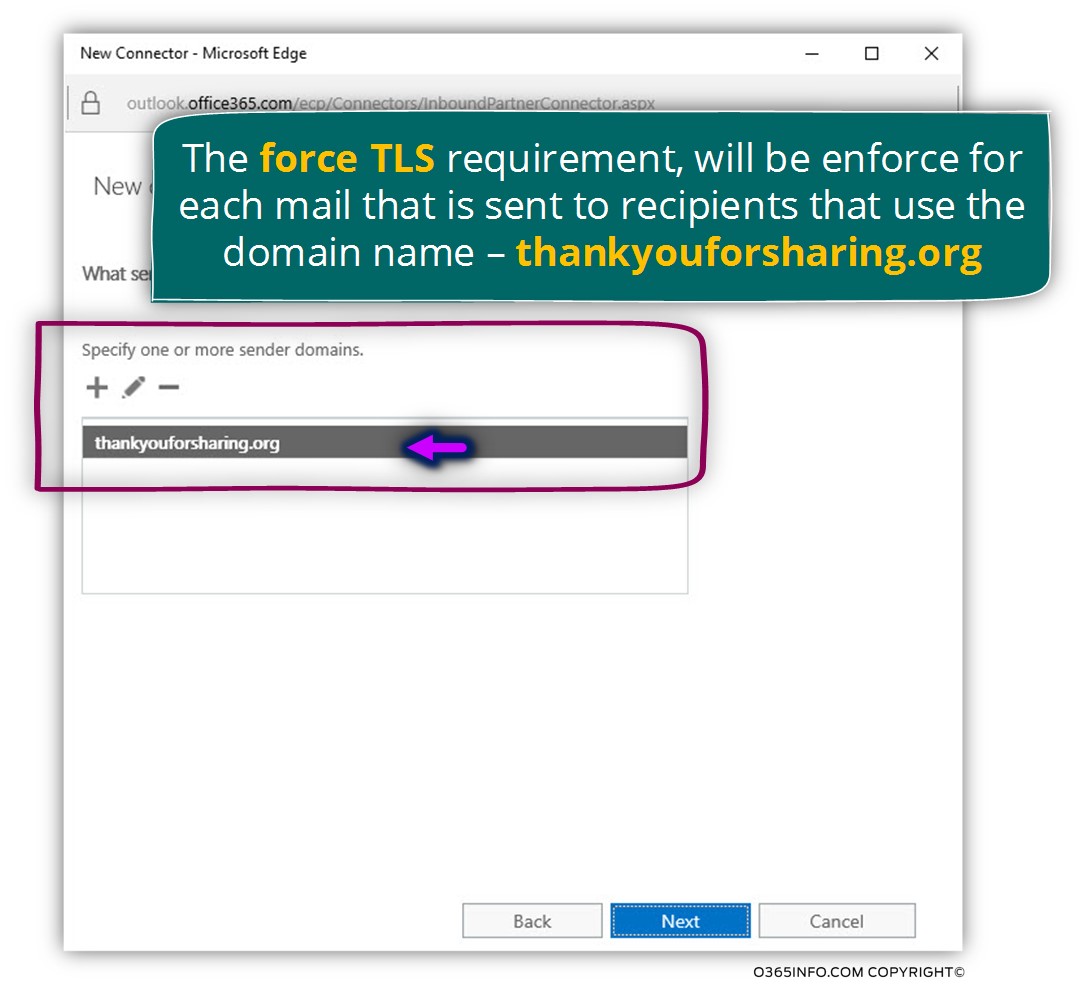
On the next screen, we will add the domain name thankyouforsharing.org
On the next screen, we decide how Exchange Online should identify the “destination mail server.”
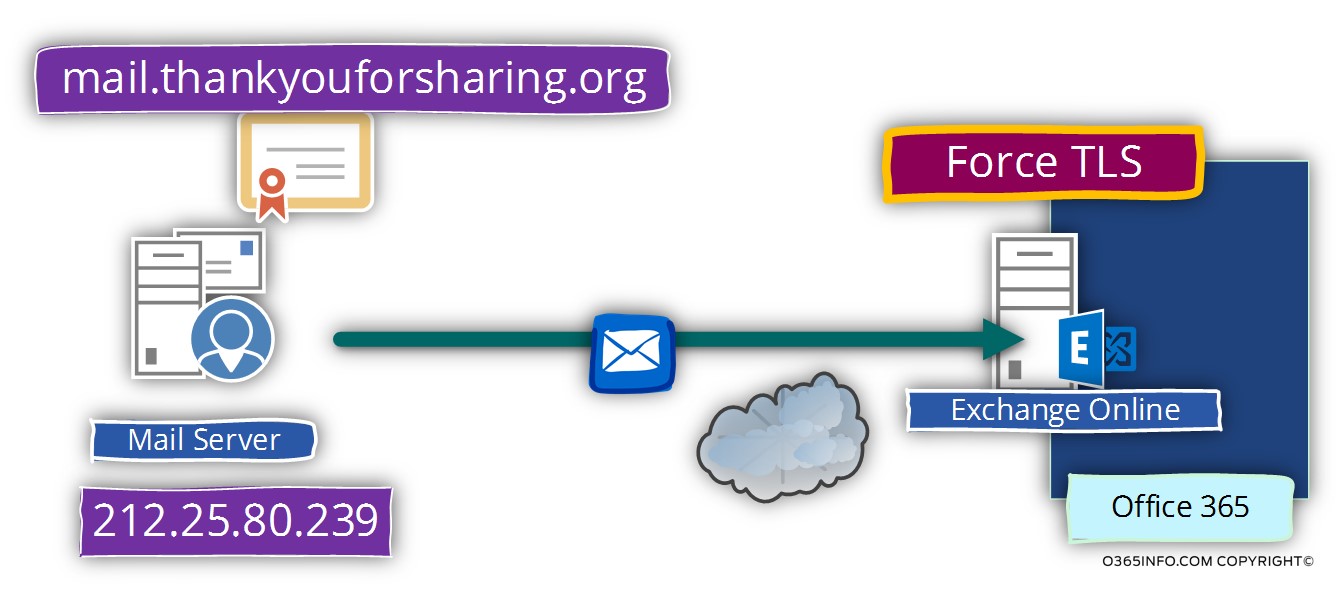
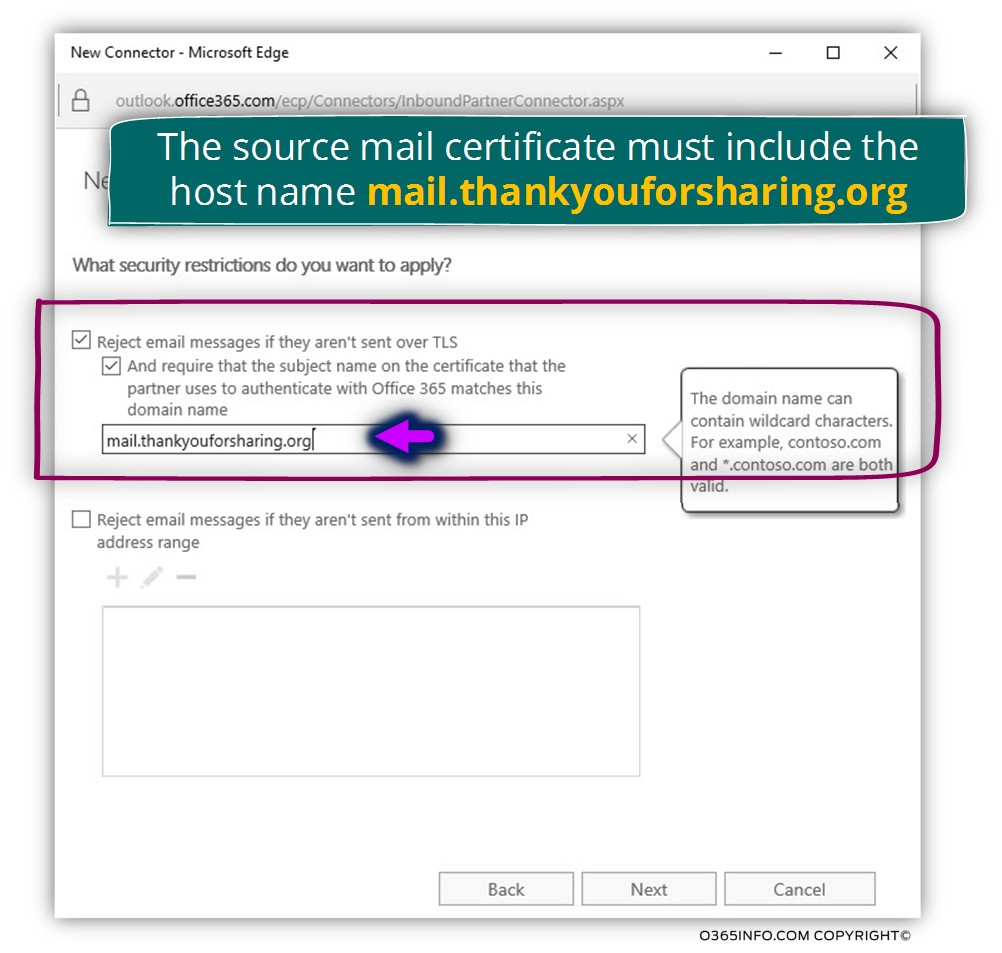
In our scenario, we want that the external mail server will identify himself by presenting a public server certificate + that the server certificate include a specific host name – mail.thankyouforsharing.org
We will select the option of – Reject email messages if they aren’t sent over TLS and in addition we will select the option box – And require that the subject name on the certificate that the partner uses to authenticate with Office 365 matches this domain name
In this section, we will need to define the specific host name (or domain name) that needs to be included in the certificate.
In our scenario we will ask for the external server to include the host name –
mail.thankyouforsharing.org
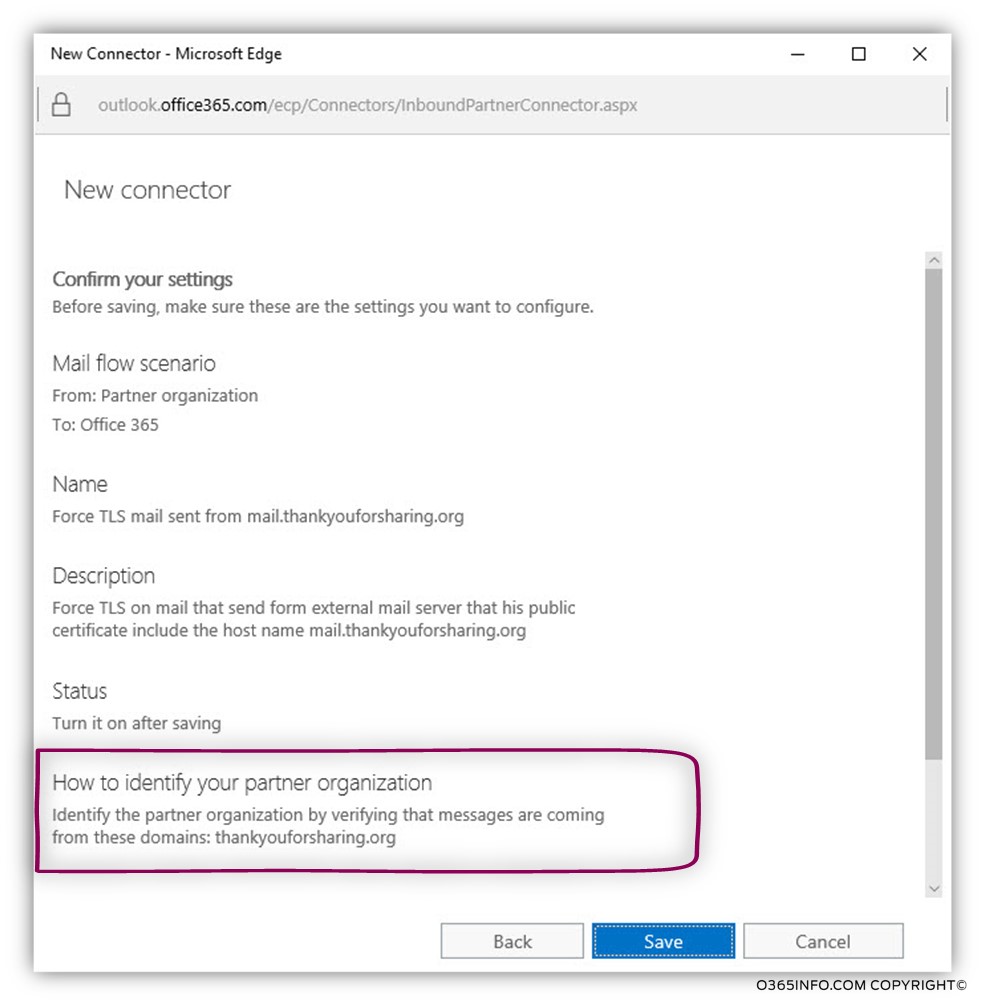
On the next screen, we can see a summary of the configuration settings.
Notice the section of – How to identify your partner organization, which inform us what will be the “trigger”, which will activate the incoming connector.
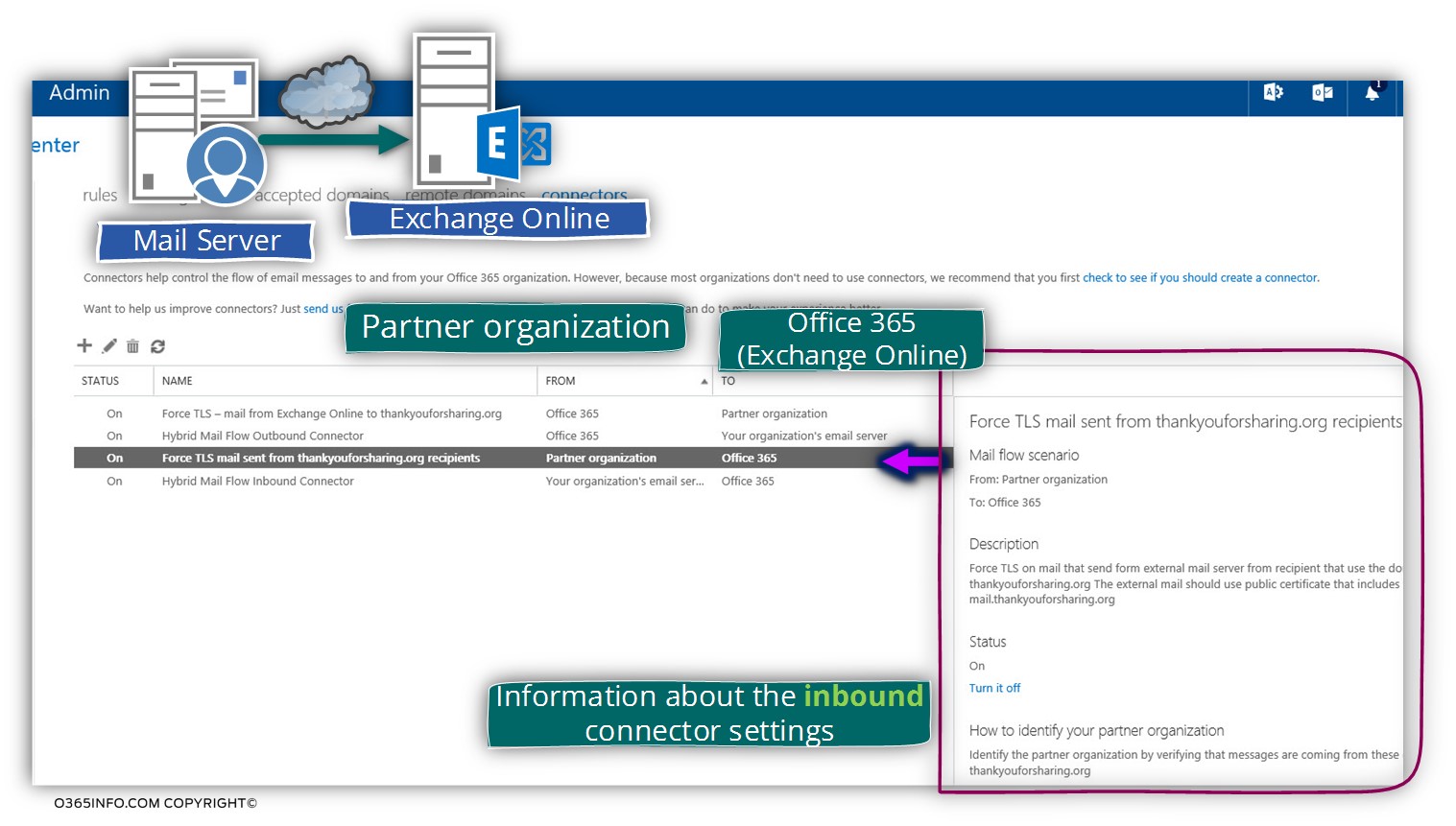
In the following screenshot, we can see the result.
A new incoming connector was created.
We can understand that this is an “incoming connector” because, under the “FROM” section, we can see that the source is – partner organization and the “TO” is Office 365.
Recap and the next article
In the current article, we have reviewed the required configuration setting that we need to implement for configuring the option of Force TLS in the Exchange Online Inbound connector.
The Force TLS setting that will be “activated” for an incoming communication channel – when an external mail server that represents the domain name – thankyouforsharing.org address Exchange Online.
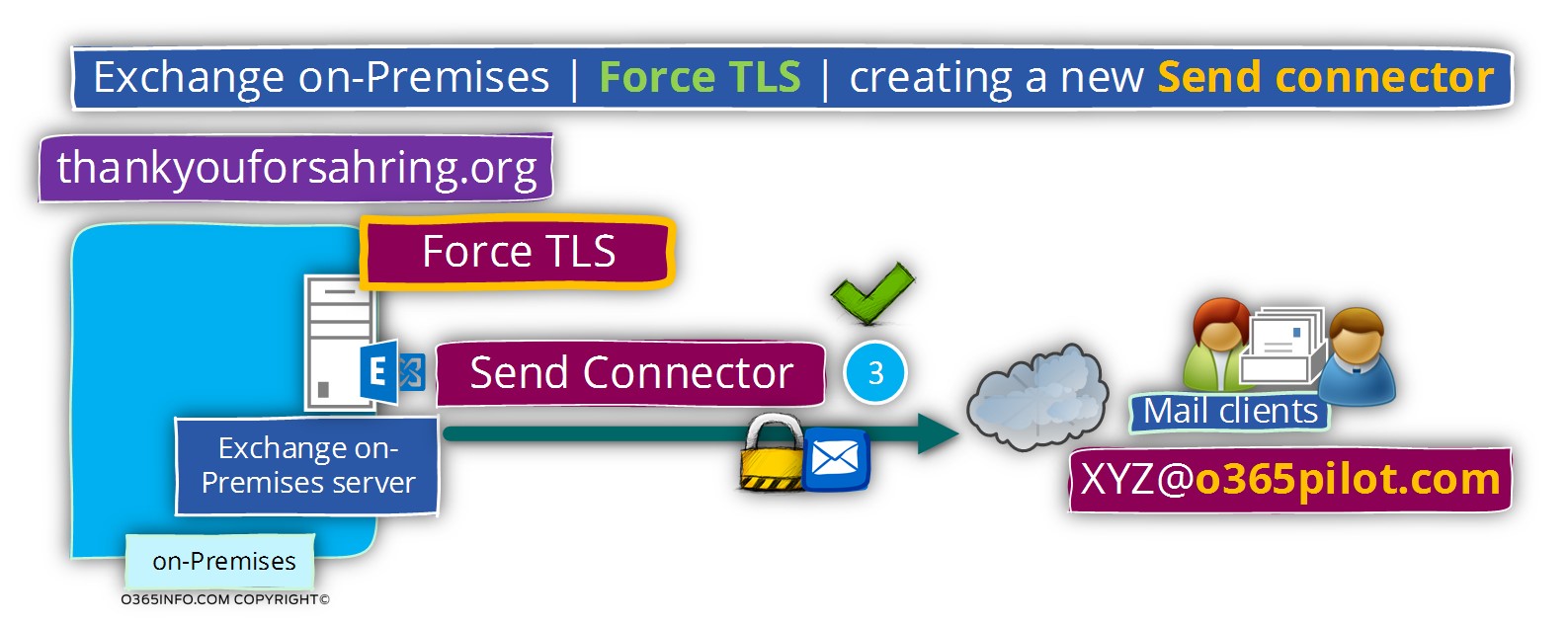
In the next article (Configure Force TLS on Exchange on-Premises environment | Settings of Send connector | Part 8#12), we will review the required configuration setting for Force TLS in Exchange on-Premises based environment.
The setting that needs to implemented on the “outgoing Exchange on-Premises mail connector”.

This Post Has 0 Comments