One of the most common questions among Office 365 customers is: how to implement a…
SMTP Relay in Office 365 environment | Part 3#4
After the migration to Office 365 (Exchange Online), users complain that they stop to get a mail message from a Fax device located within the organization Office.
You start to investigate this issue and re-check the Fax device settings. Everything looks O.K and still, email messages that send by the Fax device don’t reach their destination. Mmmm …., what happened?
The little thing that we forgot is that, until now, mail-enabled Devices\Application was configured to connect the on-premises Exchange server.
Before we can restore the ability of this Mail enabled Devices\Application to send mail to organization recipients (that located in the cloud), we will need to face some “obstacles.” Fear not, there is a solution!
Table of contents
- Send mail to Exchange Online – Article Series
- Mail client addressing mail services | Optional scenarios
- Part 1 – Implementing SMTP mail relay using IIS server
- Part 2 – Configuring IIS server as mail relay for Office 365 environment
- Part 3 – Enable the IIS SMTP relay to send mail on behalf other Email address
Send mail to Exchange Online – Article Series
- Send mail to Exchange Online | Part 1#4
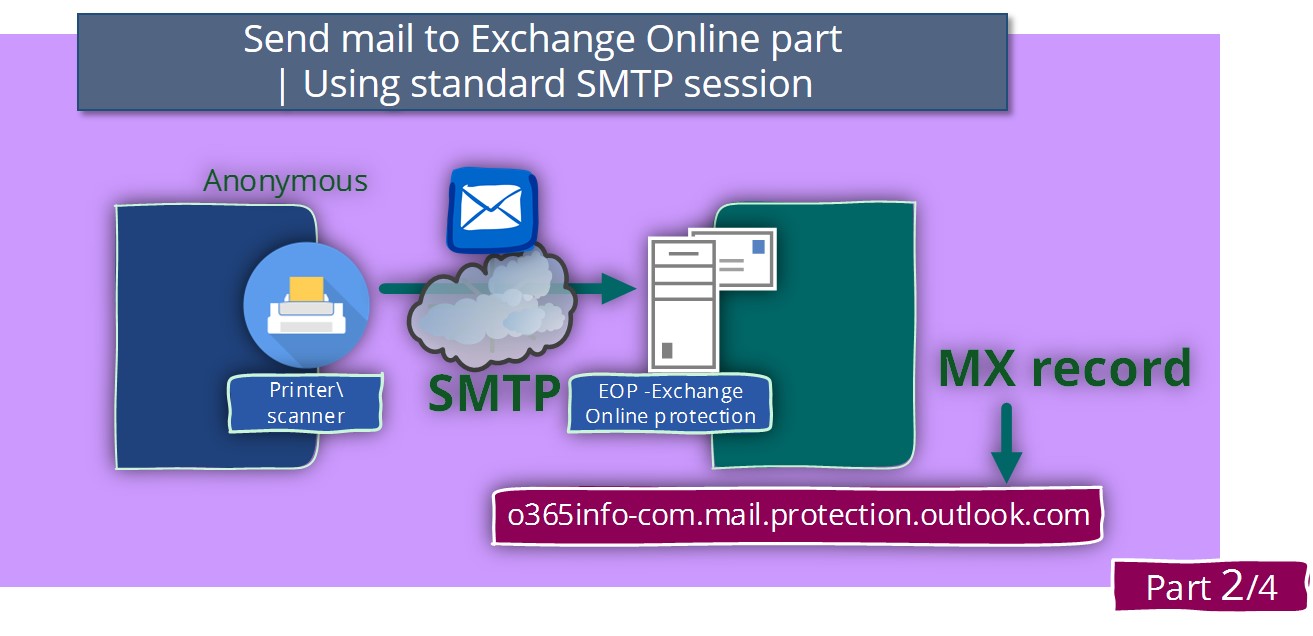
- Send mail to Exchange Online using standard SMTP session | Part 2#4
- SMTP Relay in Office 365 environment | Part 3#4
- SMTP Relay in Office 365 environment | Troubleshooting scenarios |Part 4#4
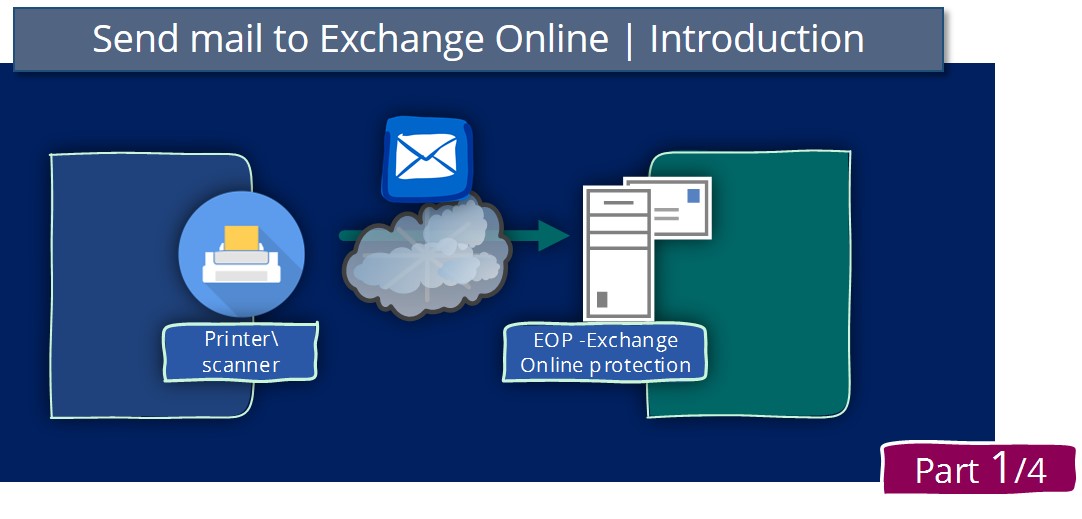
The current article is the third article in the article series that deals with the requirement of sending mail via the Office 365 mail services.
In the previous article, we have described a scenario in which we address the Office 365 mail services by using the MX record that represents “our mail server” in Office 365.
The disadvantage of this method is that this configuration configured as non-secure and has built-in limitations such as the inability to send mail to the external recipient or implement the option if “send on behalf”.
The “solution” for this disadvantage and the preferred method for connecting the Office 365 mail infrastructure is using a secure communication channel based on the TLS protocol and the need for the mail client to provide user credentials.
The primary challenge that we face is that in a scenario that the “mail client” is a hardware device such as a scanner or printer or a specific software, many times this “mail client” doesn’t support the mandatory need for creating a secure communication channel using the TLS protocol.
In this case, the solution is implemented by using a broker or an Intermediary, which described as a mail relay.
In the current article, we will review how to use the built-in SMTP server which exists in Windows Server OS – The IIS SMTP server.
Mail client addressing mail services | Optional scenarios
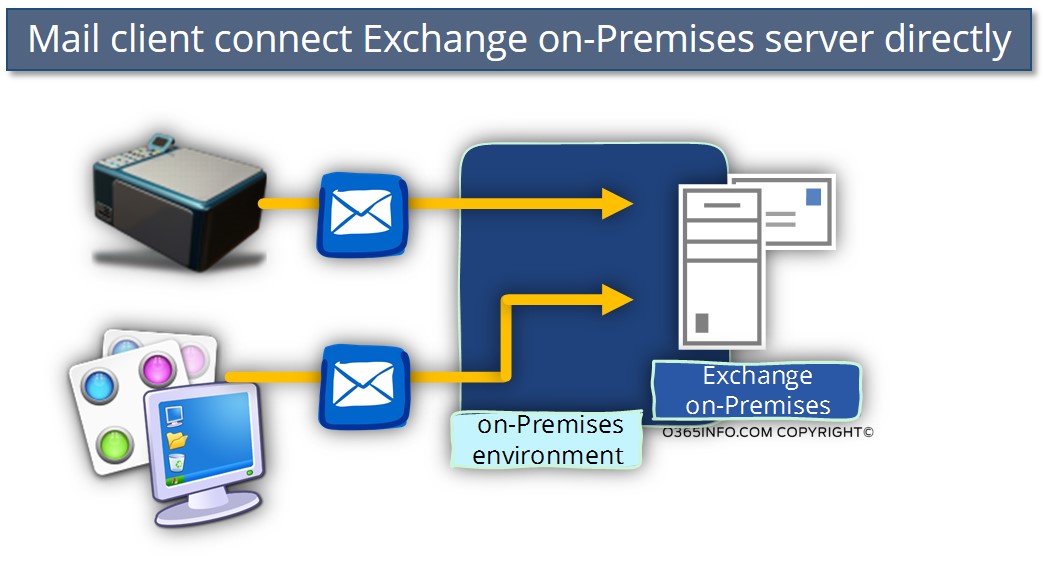
Scenario 1 – LAN Mail clients (devices\application) addressing an internal mail server
In a scenario in which LAN Mail clients (devices\application) address an internal mail server, the basic assumption is that the LAN environment considered as a “safe” (isolated from the external network).
For this reason, the typical characters of the communication between the Mail enabled Devices\Applications, and the on-premises mail server is:
- Communication channel – mail-enabled Devices\Applications communicate with the On-Premises mail server using the SMTP protocol (non-encrypted connection).
- Authentication – most of the time, the Mail enabled Devices\Applications doesn’t use authentication mechanism (Anonymous authentication).
- IP Address restriction – in some scenarios, if the administrator wants to implement a basic security mechanism, the on-premise mail server is configured to accept anonymous SMTP connection only from a particular predefined IP address.
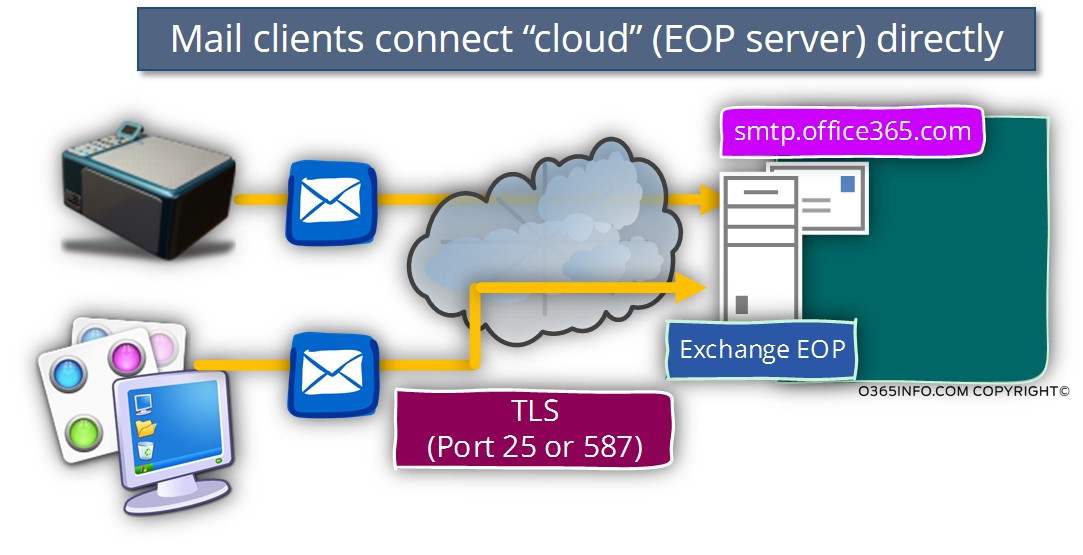
Scenario 2 – LAN Mail clients addressing Office 365 mail services using secure communication channel (TLS)
In a scenario of mail flow in a public network such as the cloud (Office 365 mail services), the characters of the communication channel are based upon different assumptions – the communication channel – the communication channel between the Mail enabled Devices\Applications and the Office 365 mail services are created via a public network infrastructure (non-trusted environment).
For this reason, the best practice from the security point of view is the need to establish a security mechanism that will enable sending mail via the Office 365 mail infrastructure in a secure way.
The “translation” for the “secure way” is implementing encrypted communication channel + the need for the Office 365 mail infrastructure to identify the “element” (Mail enabled Devices\Applications) that connect him and ask for mail services.
The charter of this scenario is Mail enabled Devices\Applications that have the ability to address the Office 365 mail infrastructure “directly” by addressing the Office 365 entities that represent the Exchange Online mail services that are available for mail clients.
To be able to address the Office 365 mail server – smtp.office365.com using a secure communication channel, the Mail enabled Devices \ Applications need to have the ability to communicate using TLS protocol + provide a user credential of Office 365 users who have an Exchange Online mailbox.
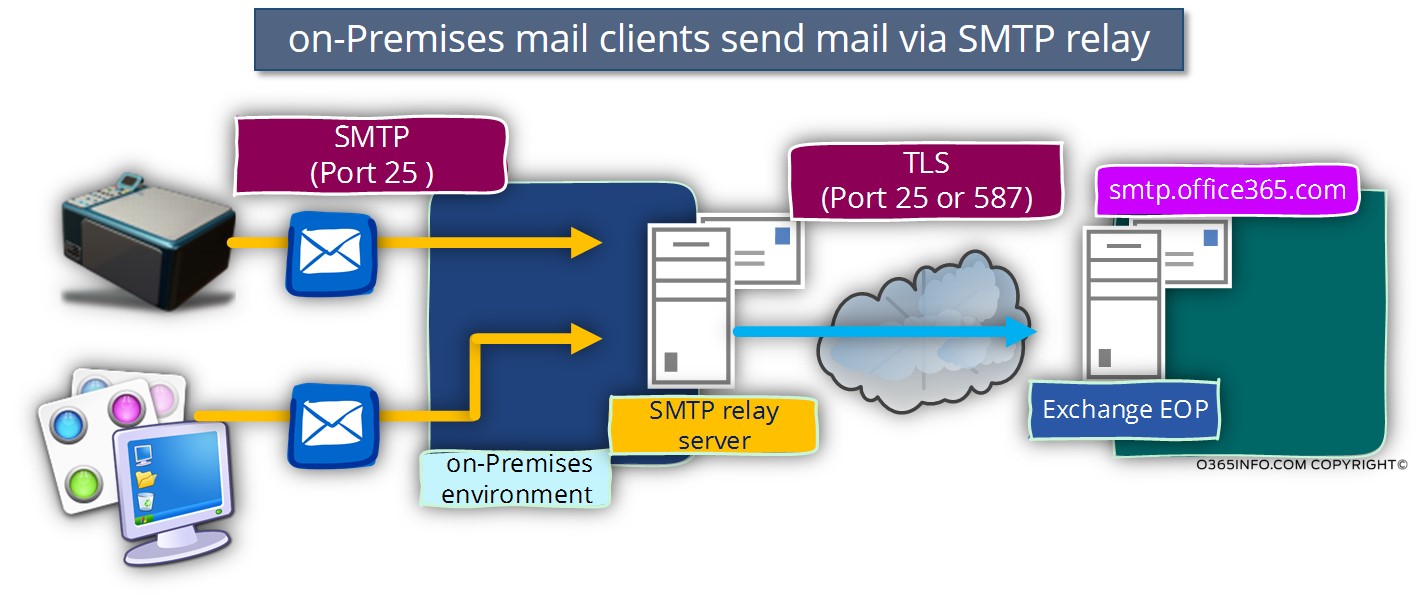
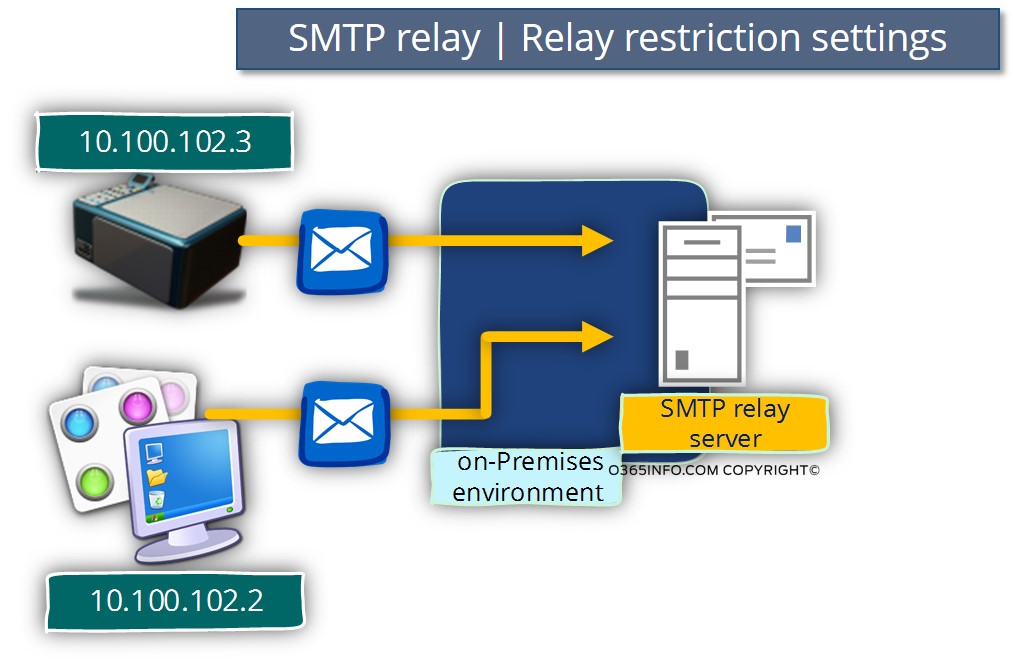
Scenario 3- LAN Mail clients (devices\application) addressing Office 365 mail services via mail relay
The third scenario, is a situation in which we want to enable Mail enabled Devices \ Applications address the Office 365 mail infrastructure using a secure communication channel.
Because the Mail enabled Devices\Applications doesn’t support the mandatory requirement for using TLS protocol + authentication, we need to use an Intermediary element that will serve as a “logic connector” between the organization Mail enabled Devices\Applications and the Office 365 mail infrastructure (EOP server).
The “logic connector” will be implemented by using an SMTP relay server.
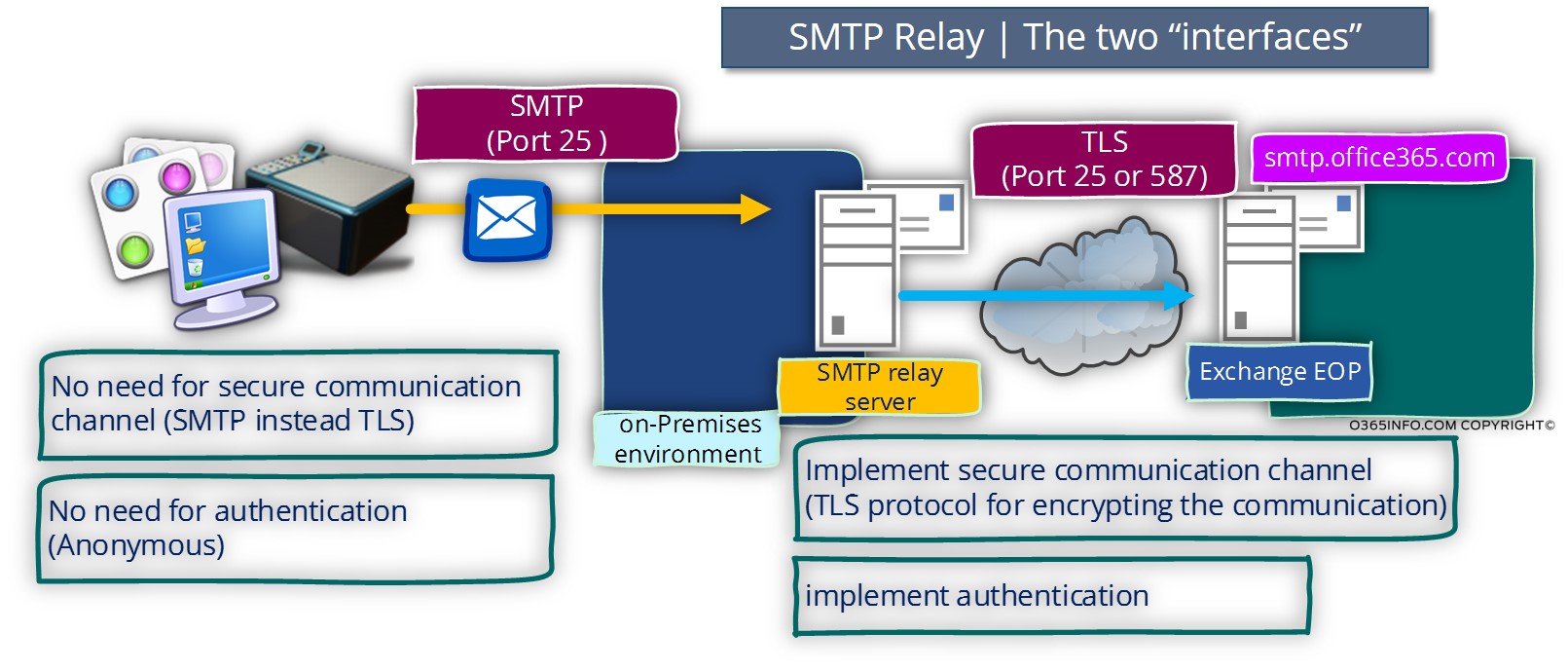
The SMTP relay server will use two separate interfaces:
- Interface 1 – the internal interface that will communicate with the organization Mail enabled Devices\Applications.
- Interface 2 – the public interface that will contact the Office 365 mail infrastructure (the EOP server) using a secure communication channel.
The public interface of the SMTP relay server will have to answer the following mandatory requirements:
- Secure communication channel – encrypted communication channel that is created by using the TLS Protocol (Port 587 or Port 25).
- Authentication – the “SMTP relay server” that wants to relay mail to the Office 365 mail infrastructure will need to provide credentials (username + password) using the basic authentication protocol.
- Mail server IP address\Host name – the “SMTP relay server” that wants to relay mail to the 365 mail infrastructure, will need to know what is the Pubic host name of the 365 mail server (smtp.office365.com).
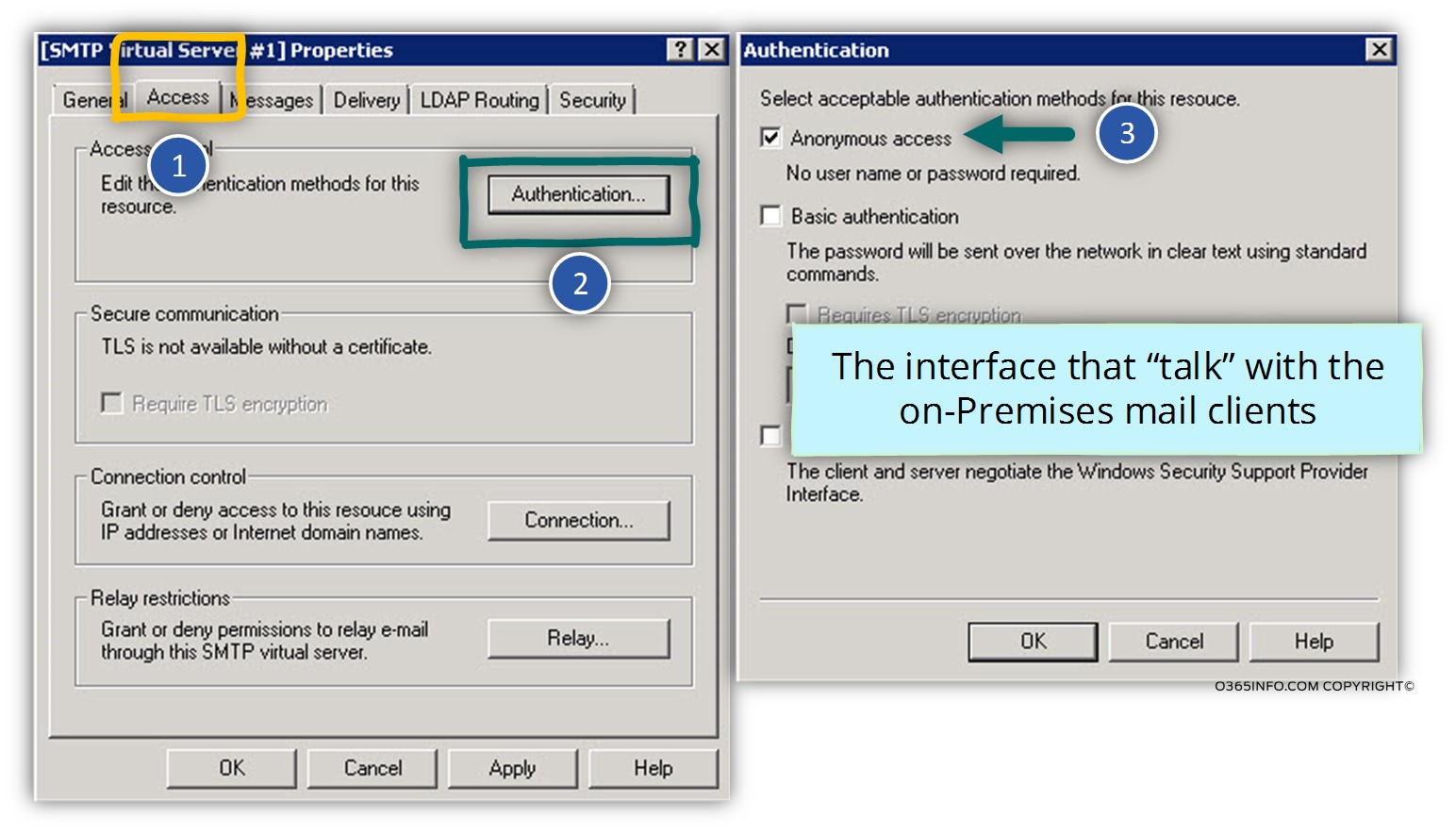
The IIS SMTP server can answer the need for the mandatory requirements of Exchange Online for TLS & Authentication. In the scenario, the IIS SMTP server will be configured with two “interfaces”:
- The interface that accepts requests from LAN Mail enabled Devices\Applications – this “interface,” will allow\accept the mail relay requests from LAN Mail enabled Devices\Applications, without the need for authentication (anonymous) and the communication channel that we use for communicating with the LAN Mail enabled Devices\Applications is based upon the SMTP protocol (no need for encryption).
- The interface that communicates with the Exchange Online – The other “leg” or interface will be used by the IIS SMTP server for the communication with the Exchange Online using: TLS and implement the requirements for authentication.
Part 1 – Implementing SMTP mail relay using IIS server
In the following section, we will review all the settings and pre-requirements that we need to implement for using IIS SMTP as a mail relay server.
SMTP Mail Relay pre-requirements
1. IIS SMTP User credentials
The credentials that the IIS SMTP use for communicating with the Exchange Online could be any Office 365 user credentials that have a valid license (license for Exchange Online Mailbox).
There is no need for purchasing a “detected” license for this purpose. The only “issue” that we should consider regarding the recipient name (the Office 365 users that we use for authenticating to the Exchange Online server) is that by default, each of the messages that will relay to the Exchange Online server will include this recipient name in the from field.
For example – in case that we configure the IIS SMTP server to use the credentials of an Office 365 users named John, each of the E-mail address that sent from a LAN Mail enabled Devices\Applications to other Office 365 recipients, will be accepted at the destination recipient as an E-mail address that sent by “John.”
Later on, we will review the scenario in which the LAN Mail enabled Devices \ Applications use different mail address and how to enable the IIS SMTP to send email “on behalf” this Hosts.
2. Firewall settings
To enable the IIS SMTP server to create a communication channel to the Exchange Online, we need to create in the organization Firewall, an outbound rule which allows the IIS SMTP to use TLS (Port 587 or Port 25).
3. Office 365 mail server entity | Hostname
To be able to refer the Exchange Online server, Office 365 use a general Hostname: smtp.office365.com
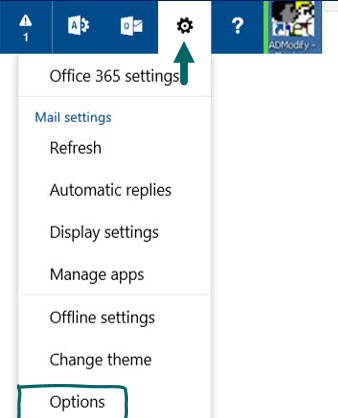
In case that you want to find the information about the Exchange Online server name, use the following instructions
- Login to Office 365 portal
- Access OWA (Mail) client
- In the top menu click on the Settings icon
- Choose the Options menu
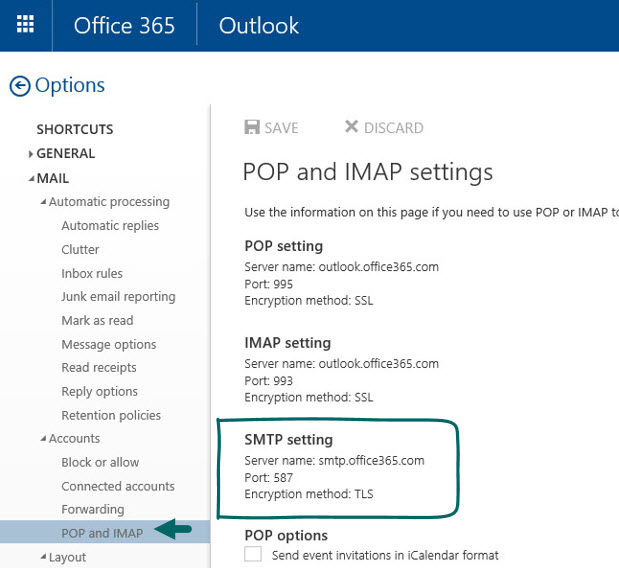
- On the left side menu bar choose the POP and IMAP menu
- In the bottom of the page, click on the Settings for POP or IMAP
- In the windows that appear, look for the section: SMTP settings
here, you can find the Exchange Online server name (smtp.office365.com) and additionally, we can see that there is a mandatory requirement for using TLS protocol (port 587 or port 25).
Installing and configuring the IIS SMTP server
In the following section, we will demonstrate how to install IIS SMTP server on a Windows 2008 server.
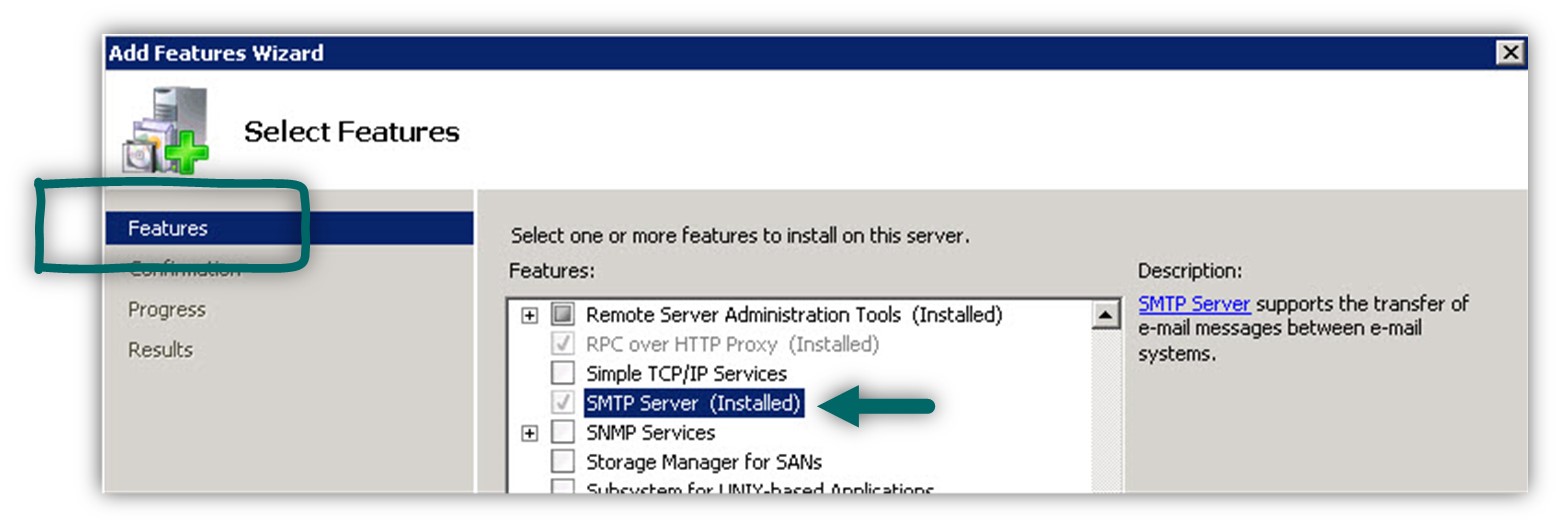
Step 1: install IIS Server
- Open Server Manager Console and under Features select Add Features
- Select the option of SMTP Server
(The reset of the installation process is just next, next, etc.)
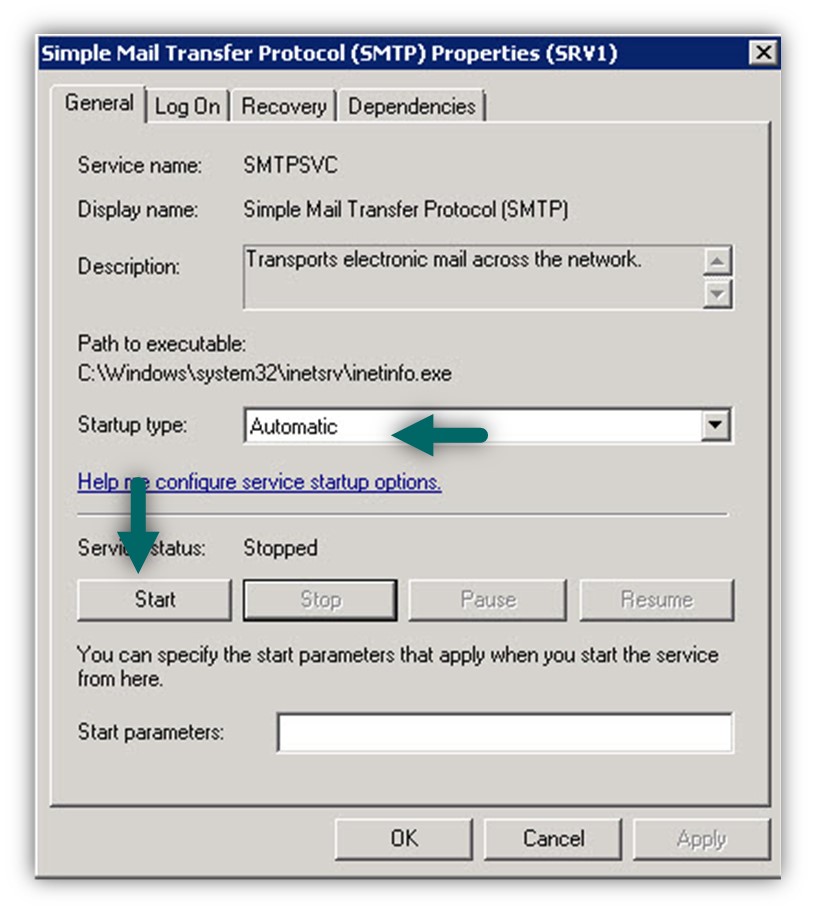
Step 2: IIS SMTP Service
By default, the IIS SMTP service is not started, and the startup type is: manual
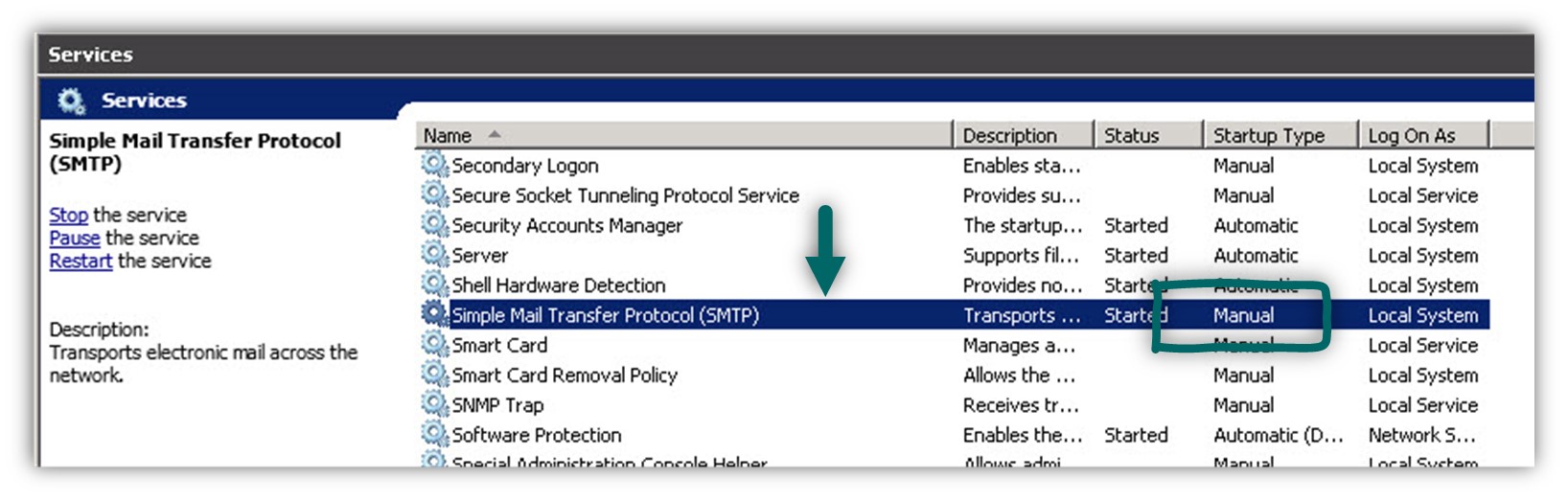
- We will need to change the default setting to – Automatic.
Double click on the SMTP Service: Simple Mail Transfer Protocol (SMTP) and, change the Startup type to Automatic - Start the IIS SMTP service (SMTPSVC)
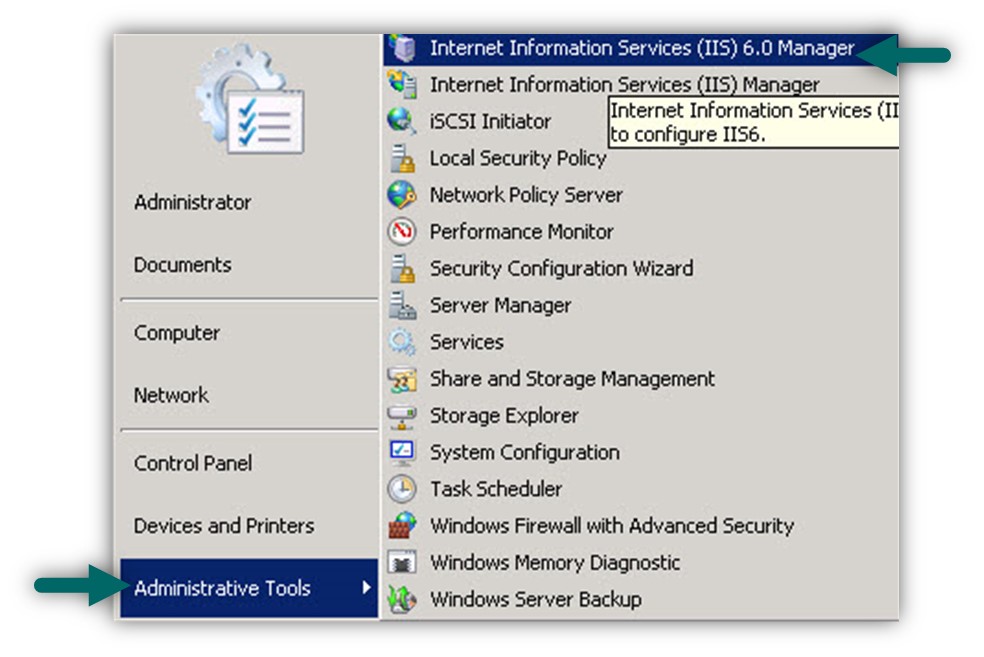
Step 3: IIS SMTP Server MMC
The management console for the IIS SMTP is Internet Information Services 6.0.
(There is no option of managing the IIS SMTP using the “standard” IIS 7 Management console). We can find the IIS 6.0 Manager under Administrative Tools -> Internet Information Services 6.0
Part 2 – Configuring IIS server as mail relay for Office 365 environment
In the following section, we will review all of the required settings for configuring the IIS SMTP server as a “SMTP Relay.”
1. IIS SMTP relay “LAN interface.”
The first part relates to the: settings for the interface or the “IIS Leg” that serves the LAN Hosts (Mail enabled Devices\Applications).
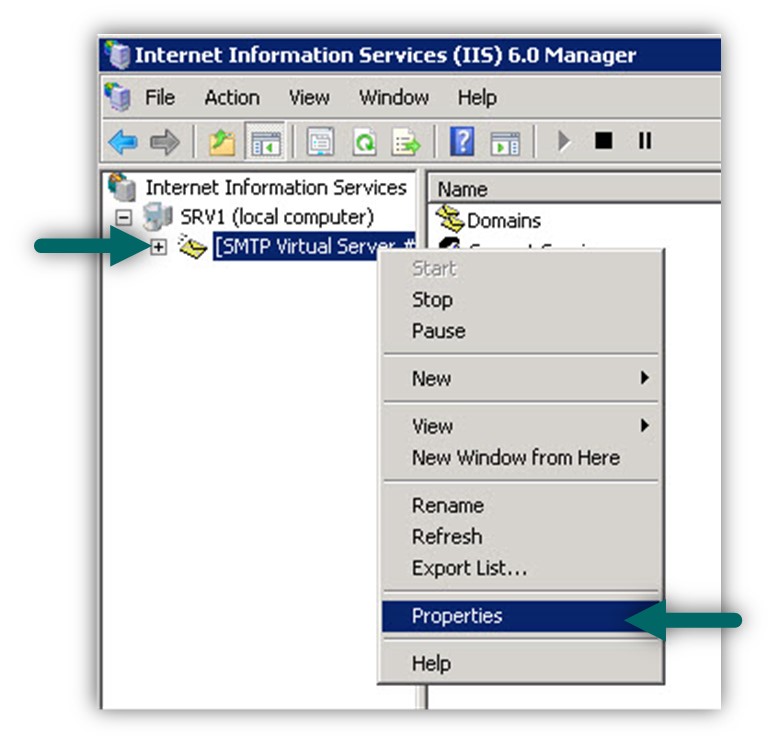
Open the IIS SMTP management console, right click on the
[SMTP Virtual Server #1] and choose: Properties
1. Access tab | Authentication
Select the Access tab -> Authentication
In the Authentication windows choose the option: Anonymous access (Mail enabled Devices\Applications doesn’t need to use authentication).
2. Access tab | Relay
The “relay” settings use for configuring the IP address of the: Mail enabled Devices\Applications that will communicate (relay mail) to the IIS SMTP server.
In our example, we have two hosts who need to send mail to the IIS SMTP server:
Help Desk application that installed on a workstation with the IP address 10.100.102.2 and, FAX device that uses the IP address: 10.100.102.3
To enable this Hosts to send (Relay) mail to the IIS SMTP server, we will need to add this IP address to the “allowed list.”
Select the Access tab -> click on the Relay… button.
In the Relay restriction window, add the IP address of the Mail enabled Devices\Applications that will communicate (relay mail) to the IIS SMTP server.
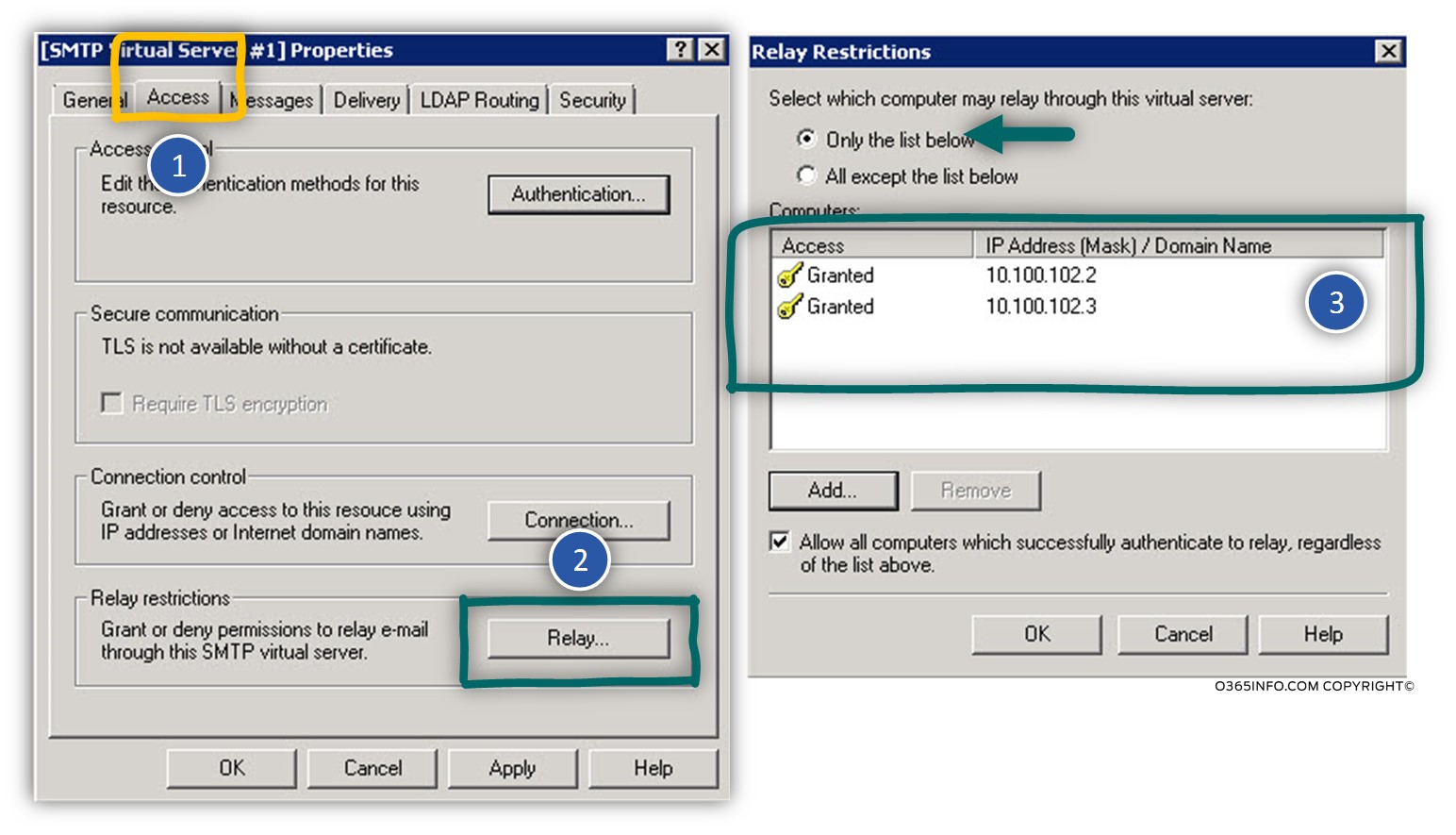
Note: Make sure that you enter only the IP addresses of the Mail enabled Devices\Applications that you trust. This setting lets’ mail that’s coming from these sources is relayed to any destination. In effect, this makes the on-premises server which is running IIS an open relay.
You can read additional information about the relay settings in the next article – SMTP Relay in Office 365 environment | Troubleshooting scenarios |Part 4#4
2. IIS SMTP mail relay “cloud” interface
In this section, we will create the required settings that enable the IIS SMTP server to relay mail messages to the Exchange Online server.
Delivery Tab
The Delivery tab, use for configuring the IIS SMTP “interface” that communicate with the Exchange Online server.
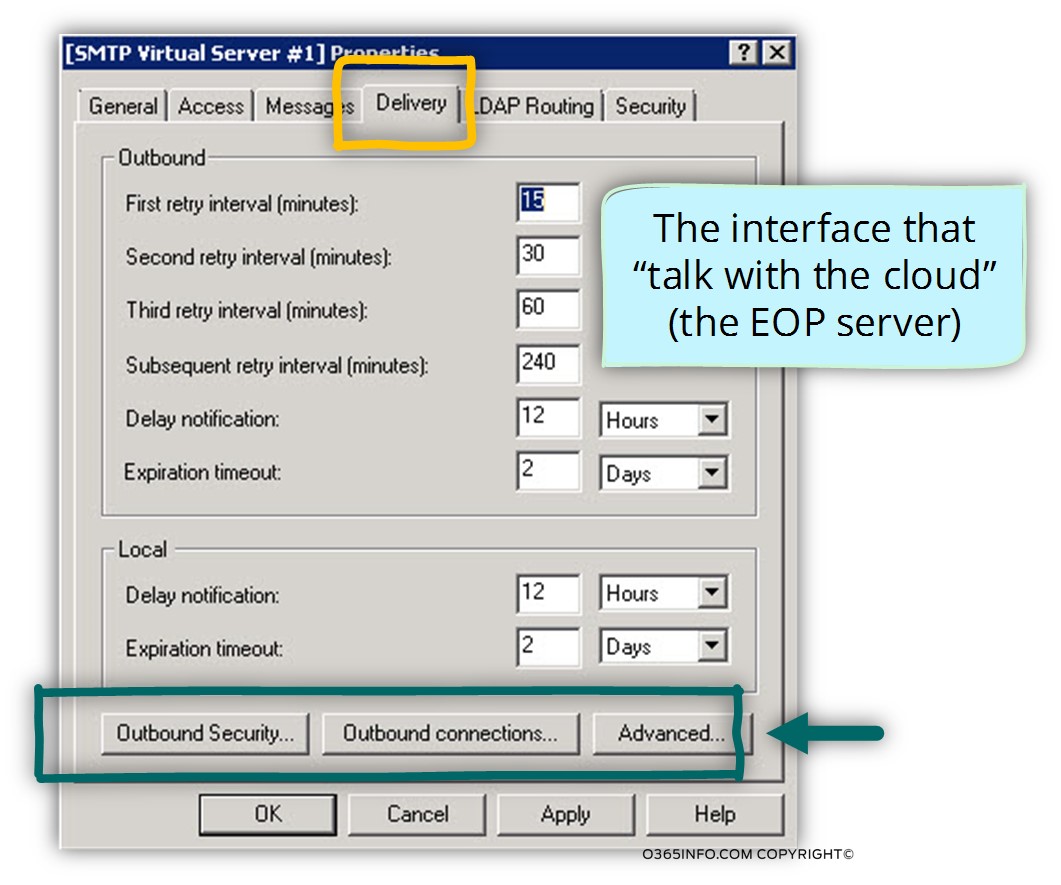
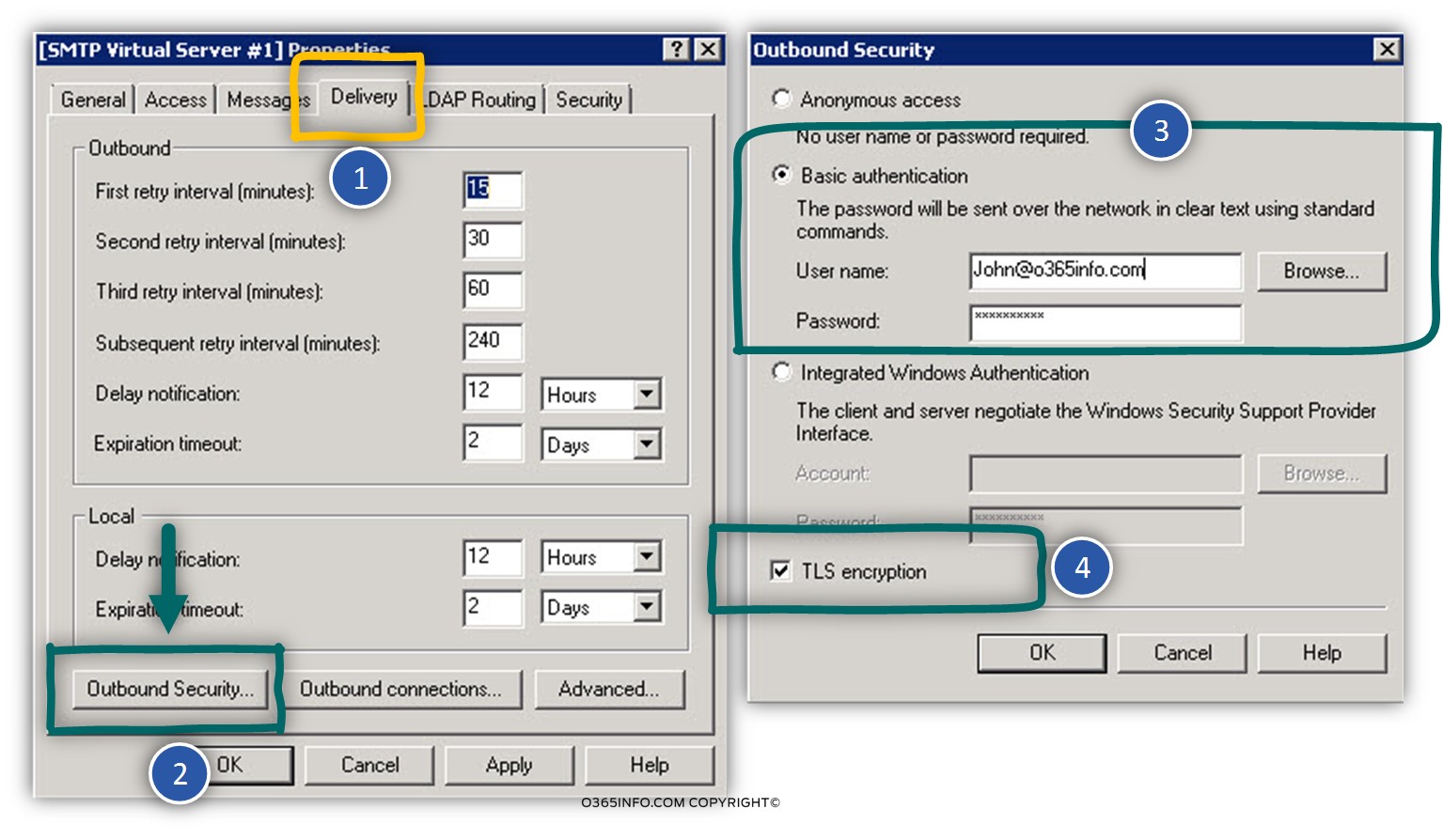
1. Delivery Tab | Outbound security
Select the Delivery tab -> Outbound Security option.
In the Outbound Security window select the option: Basic Authentication
We will need to provide the Office 365 user credentials which have Exchange Online Mailbox. In our example, we will use the credentials of a user named: John@o365info.com
Select the Delivery tab -> Outbound Security option.
In the Outbound Security window select the option: TLS encryption (for creating a secure communication channel to Exchange Online).
2. Delivery Tab | TCP port
Select the Delivery tab -> Outbound Connection option.
The TLS port number that we use for communicating with the Exchange Online is:25 (or Port 587)
(Please verify that the organization Firewall will have the required outbound rule that will enable the IIS SMTP Server to use this port ).
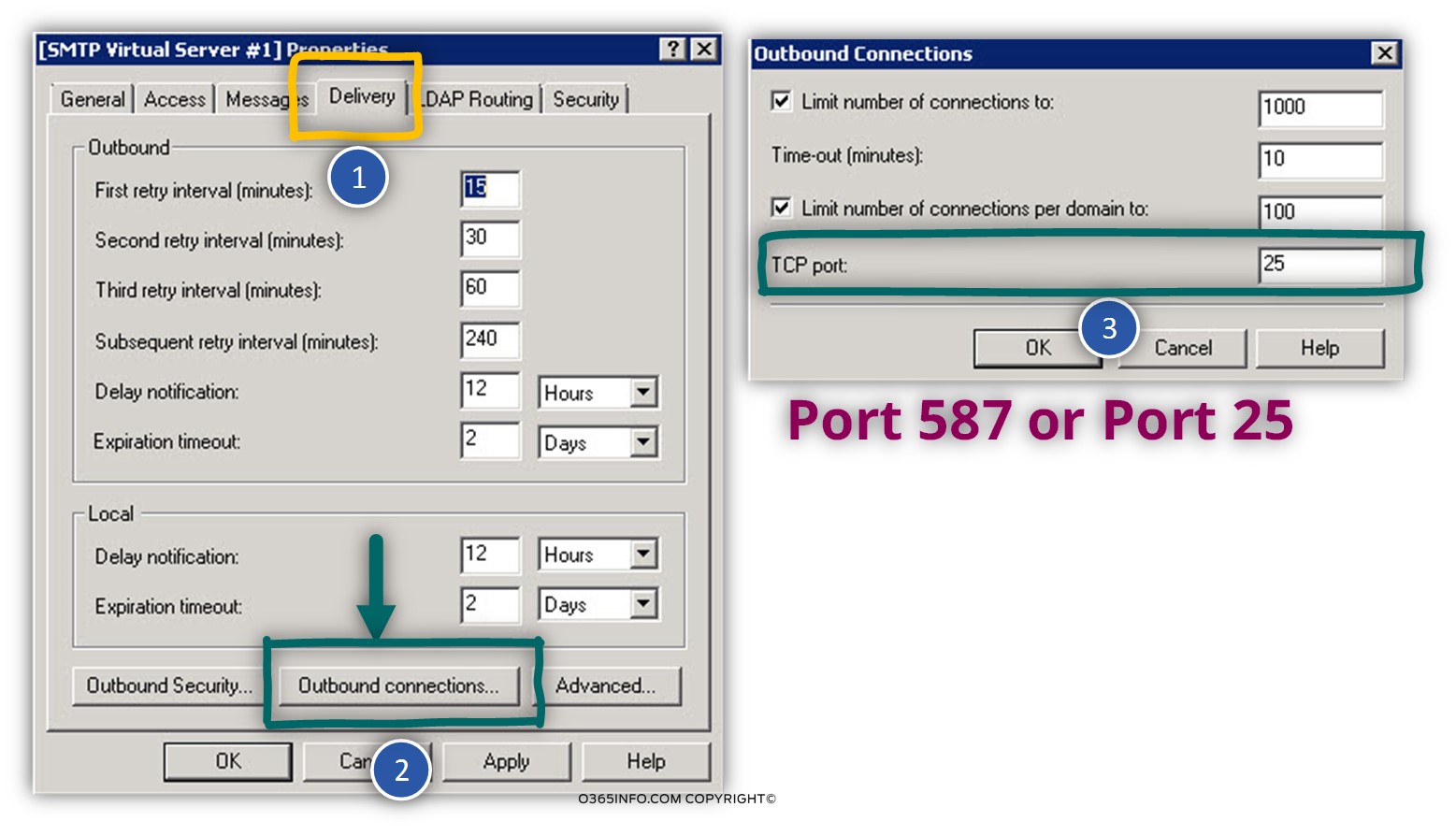
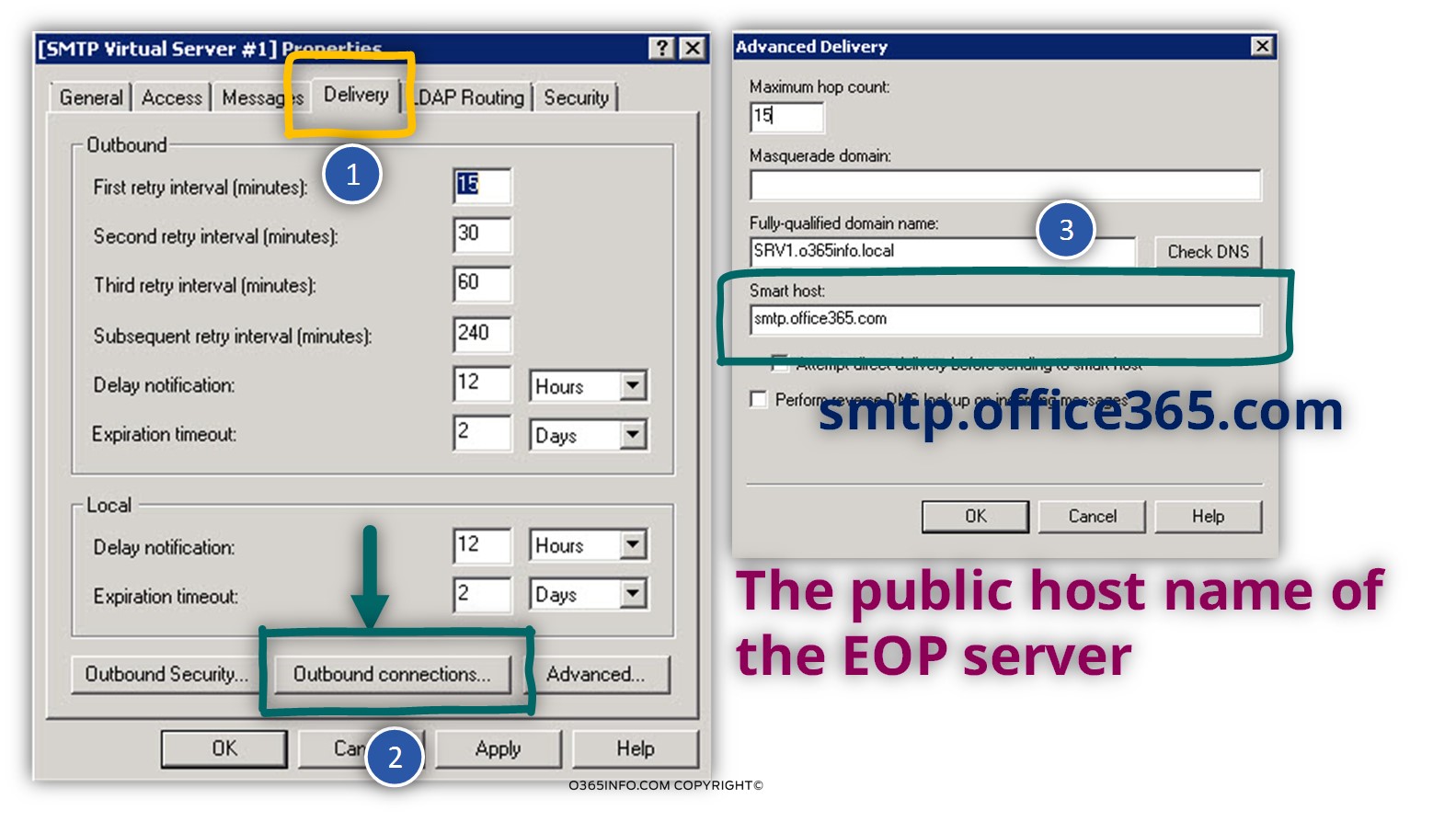
3. Delivery Tab | Advanced
Select the Delivery tab -> Advanced option
In the Smart host text box, we need to provide the Exchange Online server name.
Note: In case you need a reminder about how to find the Exchange Online server name, read the section: 3. Exchange Online server Host name
The section of Fully qualified domain name is not a mandatory requirement. You can add the FQDN of the IIS SMTP server.
Part 3 – Enable the IIS SMTP relay to send mail on behalf other Email address
After creating the required setting for the IIS SMTP relay, we will need to solve the additional issue that can describe as Enable the IIS SMTP relay to send mail on behalf another Email address.
For the demonstration purpose, let’s use the following scenario:
We want to enable two internal Hosts, to send email using the IIS SMTP server.
One Host is a Helpdesk application that uses the Email address:HelpDesk@o365info.com, and the other host is a Fax machine that uses the use the email address: FaxService@o365info.com
In case that this Hosts will try to relay mail to the IIS SMTP server, that mail message will be rejected by the Exchange Online server because: by default, a recipient (in our example: John@o365info.com) cannot send email “on behalf” other recipient’s (in our example: FaxService@o365info.com and HelpDesk@o365info.com).
The good news is that we don’t need to create a user account and Mailbox that will “represent” these Hosts, who will relay mail to the IIS SMTP Server.
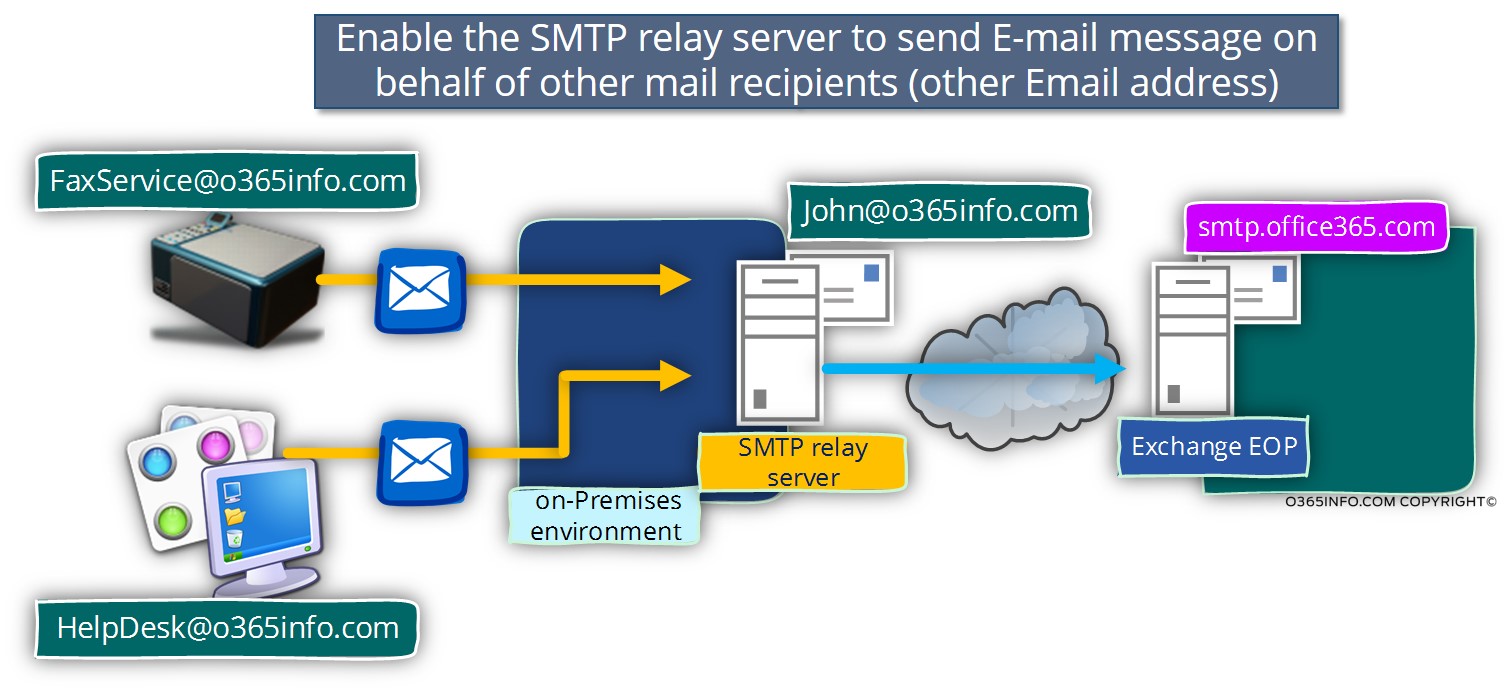
To enable the IIS SMTP server to send email for this Hosts, we can choose one of the following solutions:
1. Using distribution group and assign “Send as permissions”
This solution based on creating a distribution group for each of the Hosts who needs to relay E-mail to the IIS SMTP server.
The distribution group configured as a security group (a Security\Distribution group).
The next step is: assigning “Send as permission” for the recipient whom the IIS SMTP Server use for authentication (in our example:John@o365info.com).
The Send As permission could be assigned by using the Web interface or by using a PowerShell command.
Assign “Send as permission” using the Office 365 Web management interface
- Log in to Office 365 portal, in the Admin menu choose the option: Exchange
- In the Exchange admin center choose the recipient menu –> groups
- Click on the “Add” option and choose the Security group option.
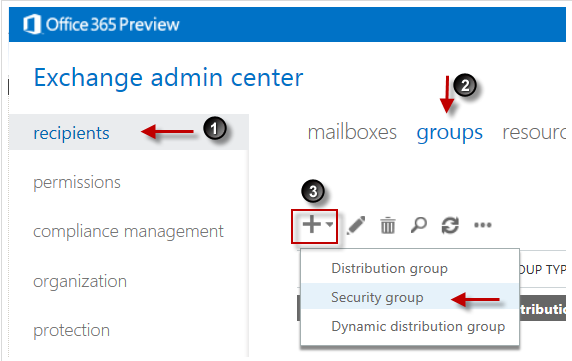
- In our example, we will name the new security-distribution group as FaxService
- Double click on the name of the new security-distribution (FaxService) and choose the menu – group delegation.
- Click on the add option and, add the recipient name that we use for the IIS SMTP credentials (in our example: John).
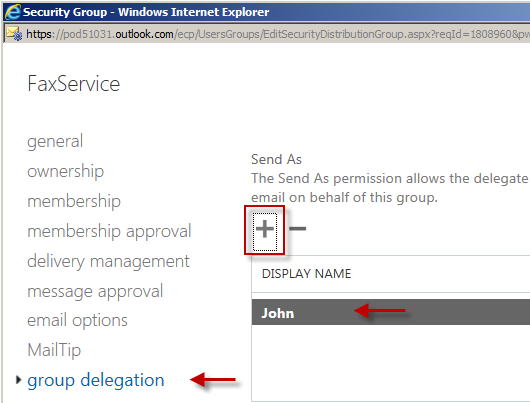
We will need to repeat this procedure, for each of the LAN Hosts that will need to relay email using the IIS SMTP Server.
Assign “Send as permission” using PowerShell command
Assign “Send As” Permissions for a Mailbox/Distribution group
PowerShell command syntax example:
Add-RecipientPermission FaxService -AccessRights SendAs -Trustee John2. Add additional Email address ( Alias)
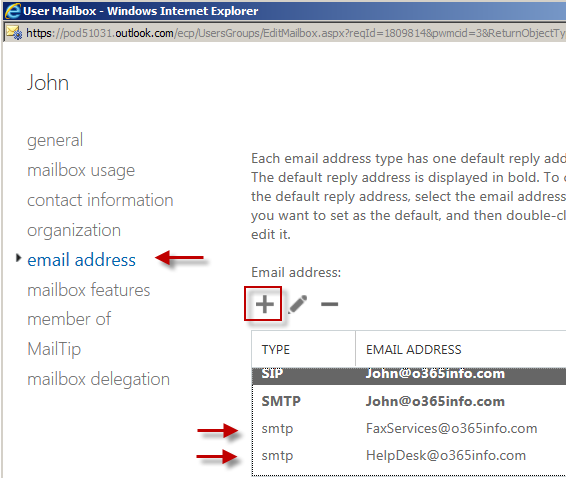
The other option that we can use ( instead of the security\distribution group solution) is: add the email address that will be used by the LAN Mail enabled Devices\Applications as an additional email address (Alias) for the recipient who is used by the IIS SMTP Server.
In our example, we will add two additional email address to the recipient named: John
- Log in to Office 365 portal, in the Admin menu choose the option: Exchange
- In the Exchange admin center choose the recipient menu –> mailboxes
- Choose the recipient name that is used by the IIS SMTP Server (in our example- John).
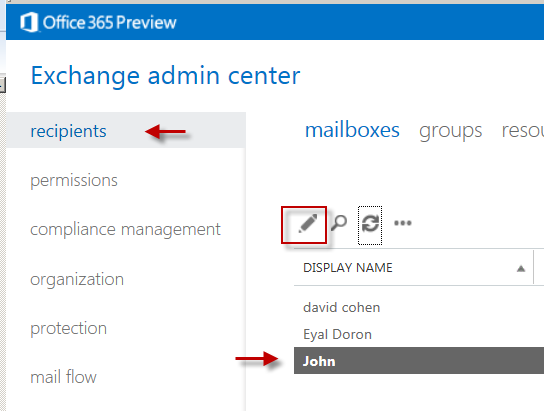
- Click on the “add” option
- In the Mailbox properties choose the option: Email address.
- In our example, we will add to “John Mailbox” additional two email addresses (Alias): FaxService@o365info.com and HelpDesk@o365info.com

Wow! 10 years later, and the ‘send as’ still does the trick! Thank you, sir!!!
Is there any limitation when using the IIS SMTP relay for O365?
We are having delay about 10 minutes for any messages that sent through smtp relay.
Our traffic could be 5k-8k emails per day.
Awesome post.
But since MS block simple auth, I guess some updates are needed.
May I simply just say what a comfort to find somebody that actually
knows what they are discussing on the web. You actually understand how to
bring a problem to light and make it important. More people have to
check this out and understand this side of
your story. I was surprised that you’re not more popular because you certainly have the gift.
Hello everybody
I have one concern regarding the “SMTP mail relay using IIS server”, if someone grabbing the IP address of these Mail enabled Devices\Applications, so he can sends email instead of these applications, which means that the authentication between the IIS server and the office365 is useless in this case, it will be only additional layer that will help hacker to authenticate their emails. ?
I followed your instructions from Part1 to Part4 and I’m still running into issues. I have a hp 4730 MFP. How would I configure the email server settings of this printer so that I receive email alerts? This is what I have entered in the email server settings: smtp.office365.com
port:587
username: john
password: password1
Domain: jerry.com
Device email address: john@jerry.com
In the SMTP gateway settings of the mfp I have:
Send E-mails directly from device
Device’s SMTP Gateway: smtp.office365.com
Port:587
Maximum Attachment Size (MB):0 I’m I missing something. Should I switch it to port 25?
excellent points altogether, you simply gained a new reader.
What could you suggest in regards to your publish that you just made a few days in the past?
Any sure?
wonderful Article, helped me figuring out the fault I was in trying to send from my fax to office 365, Thank you ALOT
Where have you been all my life? This article is great, I wish I would have found it sooner as it spells out each option we use. Excellent work!
Terrific article! Especially the troubleshooting section. Thanks for sharing the SMTP Test app, this will come in handy in the future!
One thing is if you use an alias, when the other end receives the email it will still show up as the person’s primary SMTP address.
Hi
First of all thanks again for very interesting article
you can also add an anonymous or not anonymous relay using ip and custom connector in 365
to the cloud using 25 with or without ssl
from the source nat ip of the on premises.
i noticed few times that either authentication(straight to 365) didnt work for older devices
or it was too complicated to setup a fault tolerance smtp iis’s and all the other settings for hundreds of relay hosts.
its true it isnt the most secure maybe(cause everyone using that nat could potentially use it)
I think that it’s the best article that i read about SMTP Relay.
It helped me to solve a case with a customer of mine.
Perfect KB.
Nice, but what about if want to relay you mails from Office365 –> Outbound Smarthost? The Outbound Smarthost only supports Basic Authentication and no IP Whitelist or something. Office365 doesn’t support relay authentication. what a shame.
Regards
Seth
Steve is there a link to this article MS sent you?
I was wondering if any one successfully used anonymous authentication. MS told me that I could point to my MX record and use port 25. It even was detailed out in the article they sent me. You have to create an inbound connector in the Exchange admin panel.
Benefit: You dont need to create email address or do send as permissions. It just works!
We previously had this working using mail.messaging.microsoft.com
Do you ever run into the Event Viewer error regarding TLS will not work unless the server has a certificate installed? If the server doesn’t have a certificate installed will the above configuration work?
Excellent Article but I have done everything as per the document. I am getting following error530 5.7.1 Client was not authenticatedcan you please
Excellent Article. Probably the most comprehensive I’ve seen on this topic. Most seasoned Email Geeks should have figured this on their own, but for rookies getting on Office365 it’s great to have a guide like this.Include additional how tos on powershell connectivity to ensure the article is entirely complete on it’s own.Anyway, once again…. thanks for the great post!!
It works from network not connected to our domain, but it is failing on network with local domain same as email domain. any ideas if that could be a problem?
It is nice article but i have a problem with this one, we just moved to office 365 and all is nice just relay wont work, i tried it from different network and it works from there thou all settings are the same, would local domain beeing the same as email domain affect relay capabilities?logs wont leave anything besides status code 5.0.0
Great article, all works for me apart from setting up the security group containing all the users that need to use scan to mail. What I have to do at the moment is add the scantomail account as an alias on each user so they can receive the email. Not ideal for 850 users as you can imagine. Has anyone else run into this issue and have you managed to sort it?
Cheers
Great, You are a Super Star!.Thanks a buch!
thank you for the article
Yes, how can we eitherA- use dirsync so password change flows to iis orB- use powershell to set acct pwd to never expire
How to troubleshoot when there is a email delay from scanner to office 365?
Check iis logs to see first if mail got there
How to troubleshoot when there is a email delay from scanner to the office 365 servers?
I have done everything as per the document. I am still getting following error”Diagnostic-Code: smtp;550 5.7.1 Client does not have permissions to send as this sender”can you please let me know anything to be checked?getbind@gmail.com
great article- save me a lot of time- thanks for your time in creating the series…
well written and clear -your time spent in turn saved me a lot of time- very grateful for that. Thanks
ROFL! “The little thing that we forgot is that…”
awsome article
Hi There, Is it possible to do the “enabling SMTP Relay to send on behalf of other email” but leveraging on Security Group created at Organization’s Active Directory end. Its a 365 + DirSync environment we are having here.Thanks, YJ
This article is absolutely fantastic!!!
Ron
This article is excellent!!! Works
We where trying to configure Avaya ip office voicemail to email but it could only work with port 25….this was the perfect work around
You are the man!!!
love this! really helped me out, one little problem. The system is passing email from things but it still shows up as coming from the default account (in your example john)
Hello I’m happy to hear that the article helps you :-)Regarding your question: I assume that you need to use the option of “impersonation” in which the SMTP Relay server send mail “on behalf of” other “object” such as an application or device. In that case, two conditions should be fulfilled: the “application” should be configured to send mail using user X credentials and the account that is used by the SMTP relay server should have “send as” permission for this account ( user X account). Most of the time we will implement this need by creating a distribution group that will “represent” user X and assign to required permission (Send as permission).
Its work!!!!How can i set the subject of the incoming mail ? ThanksItamar