In the following article, we will review how to write and run PowerShell script; that…
Send E-mail to office 365 using PowerShell script | Part 1#2
In the following two article series, we review the subject of – how to use a “Send E-mail PowerShell script,” that will use Office 365 mail server as his mail server. The most common use of using “Send E-mail PowerShell script” are:
- Testing the process of sending E-mail to Office 365 mail infrastructure
- Using the “Send E-mail PowerShell script” for automation purposes such as sending a daily report.
Generally speaking, there are two major options in which we address the Office 365 mail infrastructure
1. Anonymous SMTP session
2. Authenticated SMTP or TLS session.
- In the current article, we will review the method which can be disrobed as – Anonymous SMTP mail session.
- In the next article, we will review the method which can be disrobed as – authenticated TLS mail session and in addition, how to use the windows task scheduler component for using the Send E-mail PowerShell script”
Table of contents
- The two main methods for addressing Office 365 mail server
- Method 1 – addressing Office 365 mail server using standard SMTP session
- General guideline and requirements for using the “Send mail PowerShell script
- Scenario description
- Task 1#3 – Get the information about the host name of the MX record that represents your public domain name in Office 365
- Task 2#3 – Create a “Send mail PowerShell script”
- Task 3#3 – Running the “Send mail PowerShell script”
- The next article in the current article series
The two main methods for addressing Office 365 mail server
Before starting with the exact instruction about how to create the required “Send E-mail PowerShell script” let’s briefly review the method in which client can address the Office 365 mail services.
When we want to address the Office 365 mail server (Exchange Online), we can use one of the following methods:
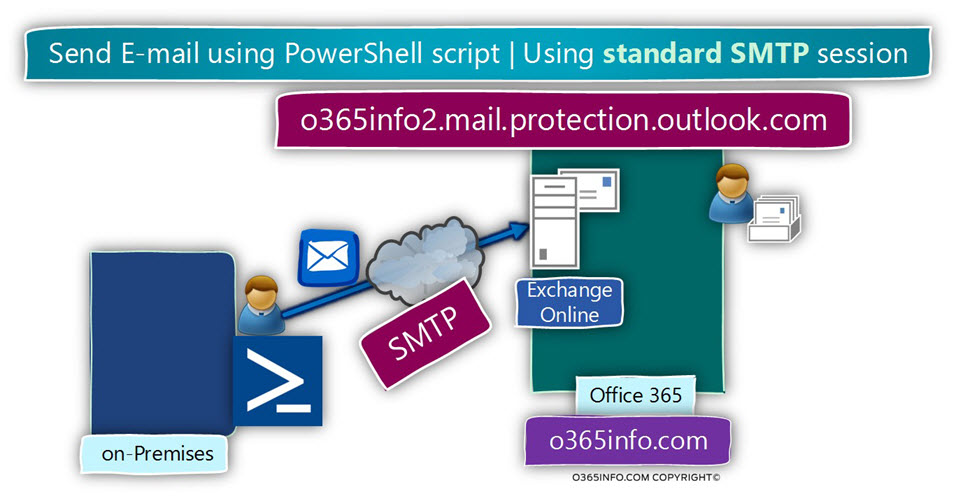
Method 1 – addressing Office 365 mail server using standard anonymous SMTP session
A method, in which we the PowerShell script addresses the Office 365 mail server using SMTP session (non-encrypted session).
The SMTP session is created using an Anonymous connection.
The meaning of ” Anonymous connection ” is that the side that addresses the Office 365 mail server (the PowerShell script), doesn’t provide any user credentials.
Advantage
The main benefit of this method is that we are avoiding from the procedure of providing user credentials. The need for providing credential is “blinded” to other tasks such as the need for securing the credentials and so on.
Disadvantages
The main disadvantages of using Anonymous connection are that the mail server cannot trust the sender because the sender appears anonymous.
Most of the time, the E-mail that will be sent by the PowerShell script will Identify as Spoof email because – the Office 365 recipient E-mail address that we use as the “sender address” is not authenticated.
Addition disadvantages are, that when using “anonymous session,” we cannot send E-mail to “external recipient” meaning, recipients whom their E-mail address is not hosted by the Exchange Online server which hosts our domain.
The solution for this problem can be implemented by creating Exchange Online incoming mail connector or define ten E-mail addresses of the sender in the whitelist of allowed senders.
If you need more information about how to create such mail connector, read the article – Send mail to Exchange Online using standard SMTP session | Part 2#4
Method 2 – addressing Office 365 mail server using TLS session + credentials
A method, in which the PowerShell script addresses the Office 365 mail server, using TLS session (encrypted session) + providing user credentials (authenticated session).
Advantage
Securing the communication channel – when using TLS protocol, the communication channel between the host who sends the E-mail and the Office 365 mail server is encrypted.
Authenticated session – the main advantage of this method is that when we provide the Office 365 recipient credentials, the Exchange Online relates to the “sender” as a trusted sender.
For this reason, we don’t need to add an additional configuration setting on the Exchange Online server side and also, we can send the E-mail to external recipients who are not hosted on the Exchange Online server.
Disadvantages
In case that we want to use “Send E-mail PowerShell script” as a scheduled task, we will need to find a solution in which the PowerShell script can access the required credentials that store in a file.
Keeping user credentials such as a password in a not secured format is bad practice!
Although we can add the password to a non-protected text file (the PowerShell file), this option is not recommended.
The solution for this “security needs,” will be implemented by a method, in which we create an encrypted password file, and instruct the “Send mail PowerShell script” to access the encrypted file and fetch the required password from this file.
The procedure in which we need to encrypt the credentials, consider as more complicated vs. the scenario in which we use SMTP session without credentials.
Method 1 – addressing Office 365 mail server using standard SMTP session
In this section, we review how to create a “Send E-mail PowerShell script,” that will address the Office 365 as a -mail server.
In this scenario, we will create a standard SMTP session, and we will not provide any user credentials (anonymous connection).
The tasks that we need to complete are as follows:
- Get the hostname of the mail server, which we will address
We will need to “fetch” the information about the Exchange Online host name meaning, the MX record that represents your public domain name in Office 365 from the Office 365 portal | DNS settings.
- Create a PowerShell script, that will include the required parameters such as the sender E-mail address, the recipient E-mail address, the mail server name, the mail server port number, the user credentials, etc.
- Running the “Send E-mail PowerShell script,” and verify that the E-mail successfully sent to the destination recipient.
General guideline and requirements for using the “Send mail PowerShell script
Before we run the “Send mail PowerShell script,” we will need to make sure that the following requirements implemented:
1. PowerShell console and Set-ExecutionPolicy
By default, the PowerShell console doesn’t allow to run a PowerShell script.
In case that we didn’t use in the past the existing PowerShell console for running PowerShell script, we will need to configure the PowerShell console to “allow” PowerShell script execution.
In case that you need instruction reading how to enable the PowerShell script execution, you can use the instruction in the following Section
2. Network Firewall and outbound communication
The communication channel to the Exchange Online server based on port 25.
We will need to verify that our network Firewall, include a rule that enables our desktop to implement SMTP session (port 25) with the Office 365 mail server.
3. Dynamic vs. static IP Address
In case that you run the “Send E-mail PowerShell script” from a desktop that uses “dynamic Public IP address” such as Home network, the Office 365 mail server (Exchange Online) will not accept the communication requests.
You will need to use a host who located on a network that uses a static IP address for representing internal hosts.
Scenario description
To be able to demonstrate the way that we use “Send E-mail PowerShell script” for sending
E-mail via the Office 365 mail server (Exchange Online), we will use the following scenario:
Organization information
- Our organization public domain name is – o365info.com
- Our mail infrastructure is hosted at Office 365 (Exchange Online).
User credentials
The Office 365 recipients whom we will use his credential is –admin@o365info.com
Source sender and destination recipient
In our scenario, we will use the following recipients:
- The sender E-mail address is – admin@o365info.com
- The recipient E-mail address is – admin@o365info.com
Office 365 mail infrastructure
In the Office 365 environment, if we want to use a non-authenticated session with Office 365 mail server, we will need to locate the host name of the Exchange Online that represents our public register domain in Office 365.
- In our specific scenario, the host name of the Office 365 mail server is – o365info2.mail.protection.outlook.com
Note – we will review how to get the information about the Exchange Online host name in the next section.
- The communication port that we use is 25 (TLS)
Task 1#3 – Get the information about the host name of the MX record that represents your public domain name in Office 365
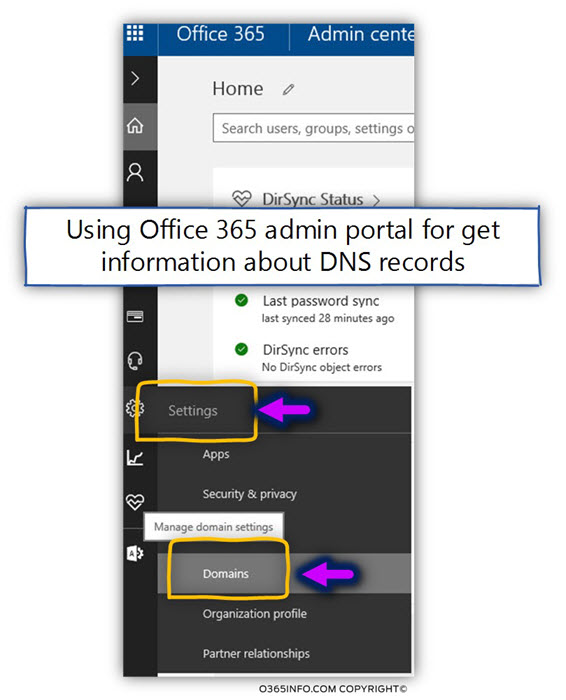
To be able to get the hostname of the Office 365 mail server that represents our public domain name, we will use the Office 365 management portal.
- Login into Office 365 management portal
- On the left menu bar, select the Settings icon
- Select the Domains menu
In our scenario, we will select to view the setting of the domain name – o365info.com by double-click on the selected domain name.
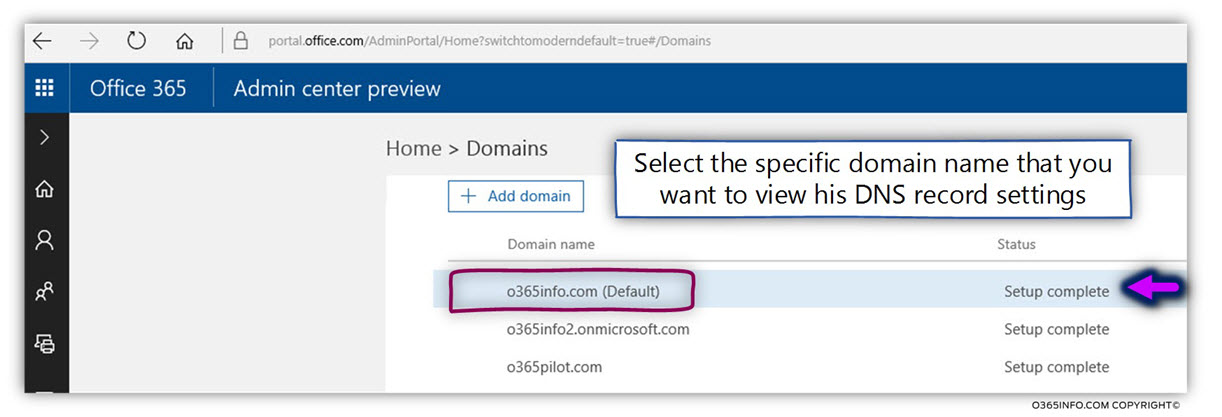
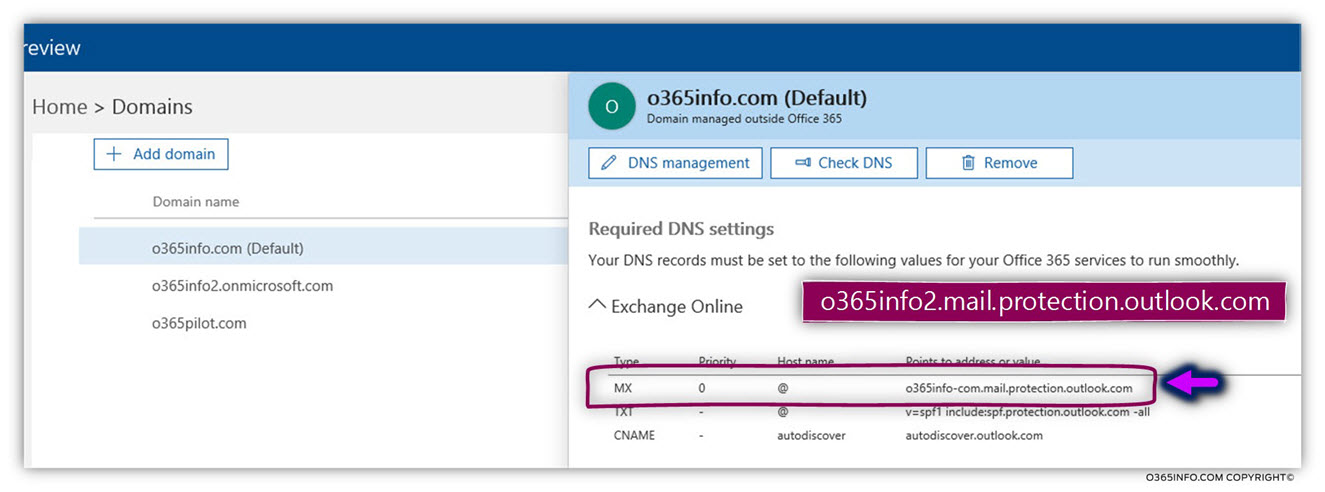
In the following screenshot, we can see the DNS setting of the o365info.com domain.
We will copy the information about the hostname who appears in the MX record.
In our scenario, the host name of the Exchange Online that represents our domain is – o365info2.mail.protection.outlook.com
Task 2#3 – Create a “Send mail PowerShell script”
To be able to send E-mail using PowerShell, we will use the PowerShell command:
Send-MailMessageThe “Send mail PowerShell script” is created using the following PowerShell syntax:
Send-MailMessage –From <sender> –To <recipient> –Subject "<Subject>" –Body "<Subject>" -SmtpServer <SMTP server> -Port <port number>In our scenario, we will use the PowerShell command syntax using the following parameters:
Send-MailMessage –From admin@o365info.com –To admin@o365info.com –Subject "Test Email" –Body "Test SMTP Relay Service" -SmtpServer o365info2.mail.protection.outlook.com -Port 25To create the PowerShell script, we can use any text editor.
In our example, we use the notepad.
We will copy the following information to the text file:
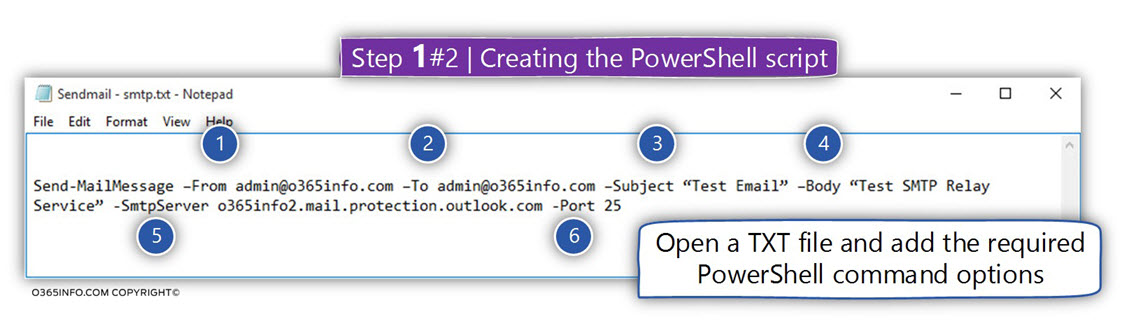
The PowerShell command syntax includes the following parts:
- From (number 1) – we will use the E-mail address – admin@o365info.com for representing the sender E-mail address.
- To (number 2) – we will use the E-mail address – admin@o365info.com for representing the destination recipient E-mail address.
- Subject (number 3) – this is the text of the E-mail subject
- Body (number 4) – this is the text that will appear in the E-mail message “body”
- SmtpServer (number 5) – this is the host name or the IP address of the mail server that we want to address. In our scenario, we want to address the Exchange Online server, as the “mail server.” server”. We will provide the host name whom we get from the previous step – o365info2.mail.protection.outlook.com
- Port (number 6) – this is the port number of the mail server that will “listen” to our communication requests. In the Office 365 environment, the Exchange Online will listen using port 25.
Saving the PowerShell script file
The next step is – saving the text file as a PowerShell script.
We use notepad for creating the PowerShell script.
In our scenario, we will name the PowerShell script – Sendmail-smtp.ps1
- In the section – Save as type” select the option – All Files (*.*).
- The additional recommended option is, to save the PowerShell script
using UTF-8
This is not a mandatory requirement, but, from my experience, when saving the PowerShell script using standard formats such as ANSI, we can experience a problem when we try to run the PowerShell script from the PowerShell console.
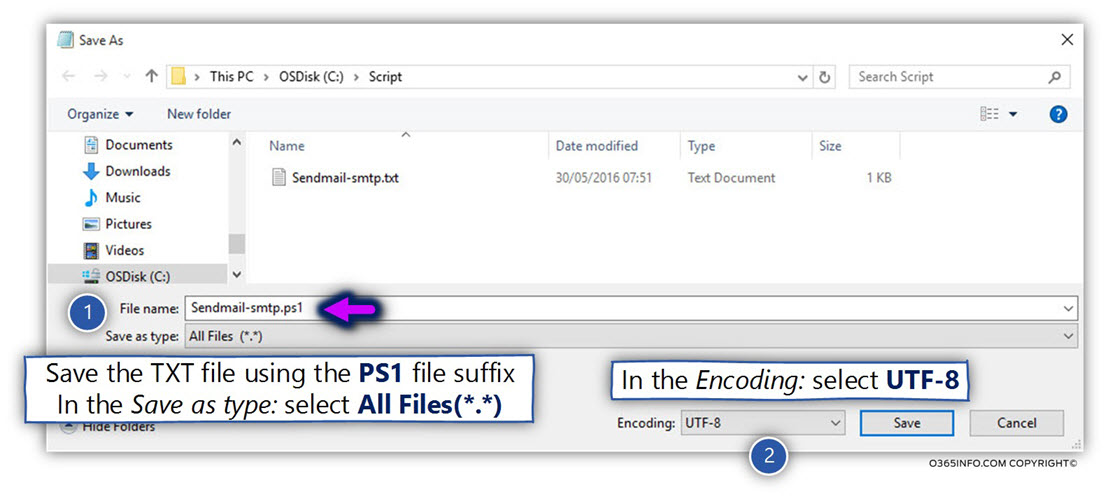
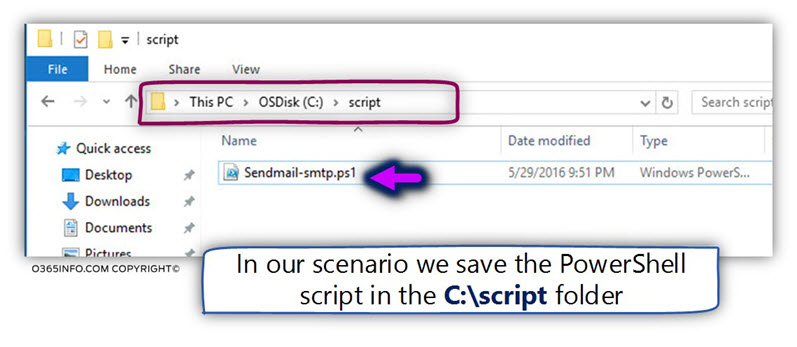
In our scenario, we save the “Send E-mail PowerShell script” in the script folder, that we have created in drive C:
Task 3#3 – Running the “Send mail PowerShell script”
Running PowerShell script | First time configurations
By default, the PowerShell console will prevent us from running the PowerShell script.
To be able to run the PowerShell script, we will need to set the default PowerShell exaction policy.
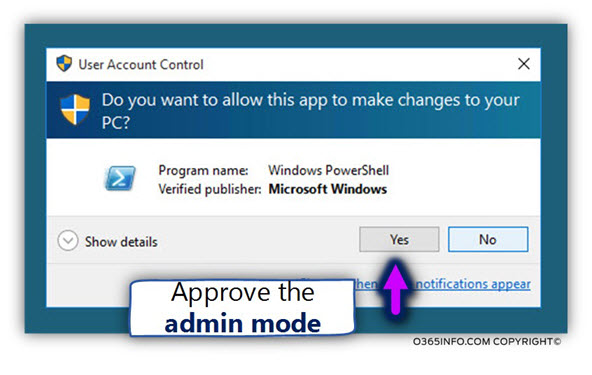
To be able to update the existing PowerShell exaction policy, we need to run the PowerShell console as Administrator.
- Search for the PowerShell icon, right click on the PowerShell console icon and select the menu – Run as administrator
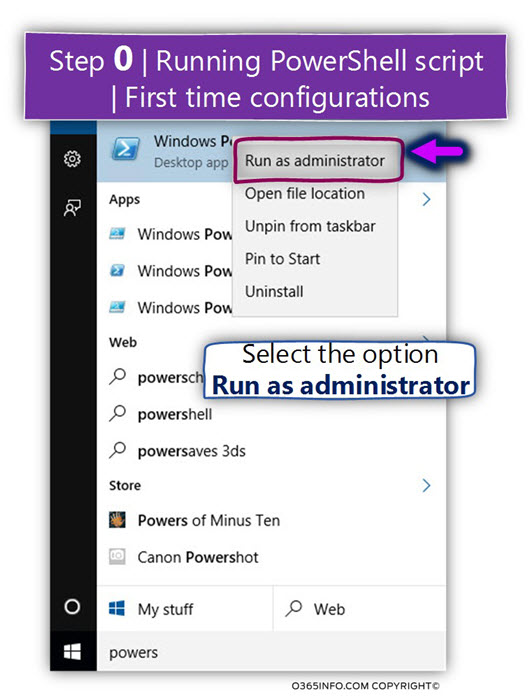
A pop out window appears, asking from us to approve the “run as administrator” task
- Click Yes to approve
Run the following PowerShell command:
Set-ExecutionPolicy Unrestricted -force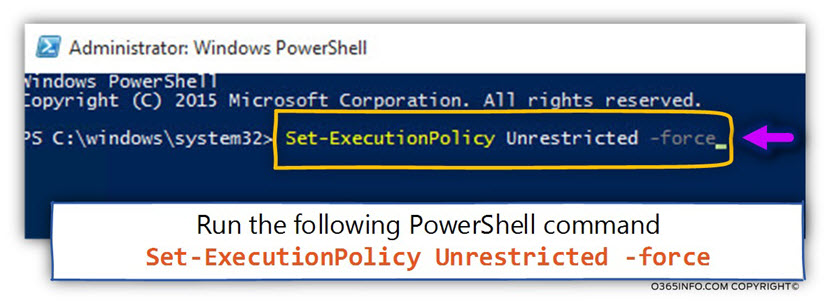
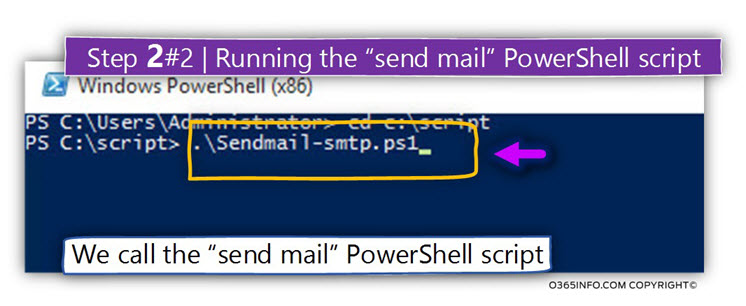
Task 2#2 – Running the “Send mail PowerShell script”
We will run the “Send mail PowerShell” from the PowerShell console, by using the following commands:
- Access the PowerShell script by navigating to the path in which the PowerShell script located.
In our scenario, the PowerShell script saves in the C:\script folder.
Type the following command:
cd C:\script- Run the PowerShell script
To execute the PowerShell script, we can write the full name of the
script – Sendmail-smtp.ps1 or use the PowerShell autocomplete feature.
For example, to call a PowerShell script we need to write the following characters – .\ , type the first letter of the PowerShell script (“s“) and hit the Tab key.
After “hitting” the TAB key, The PowerShell consoles, we complete the rest of the PowerShell script name by himself.
To verify if the E-mail message successfully sent, we will login to the admin mailbox using OWA mail client.
In the following screenshot, we can see that the E-mail successfully sent to the destination recipient, but it’s important to emphasize that the E-mail sent to
the junk mail folder.
This is an expected result because as mentioned, the PowerShell script uses the identity of Office 365 recipient (admin@o365info.com). Because the PowerShell script didn’t provide any user credentials, Exchange Online considers the E-mail message as a ” suspicious E-mail” and for this, reason stamps the E-mail as Junk!
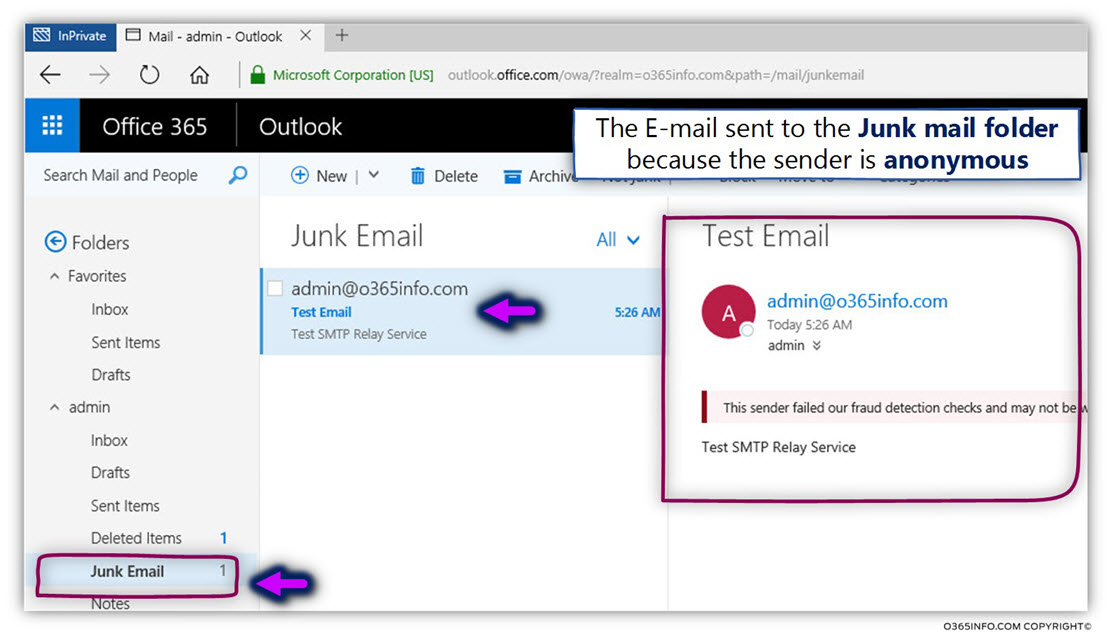
If you want to avoid this scenario, it’s recommended to create an Exchange Online Connector which will identify the “source sender” by his public IP address.
You can read more about this configuration is the article – Send mail to Exchange Online using standard SMTP session | Part 2#4
The next article in the current article series
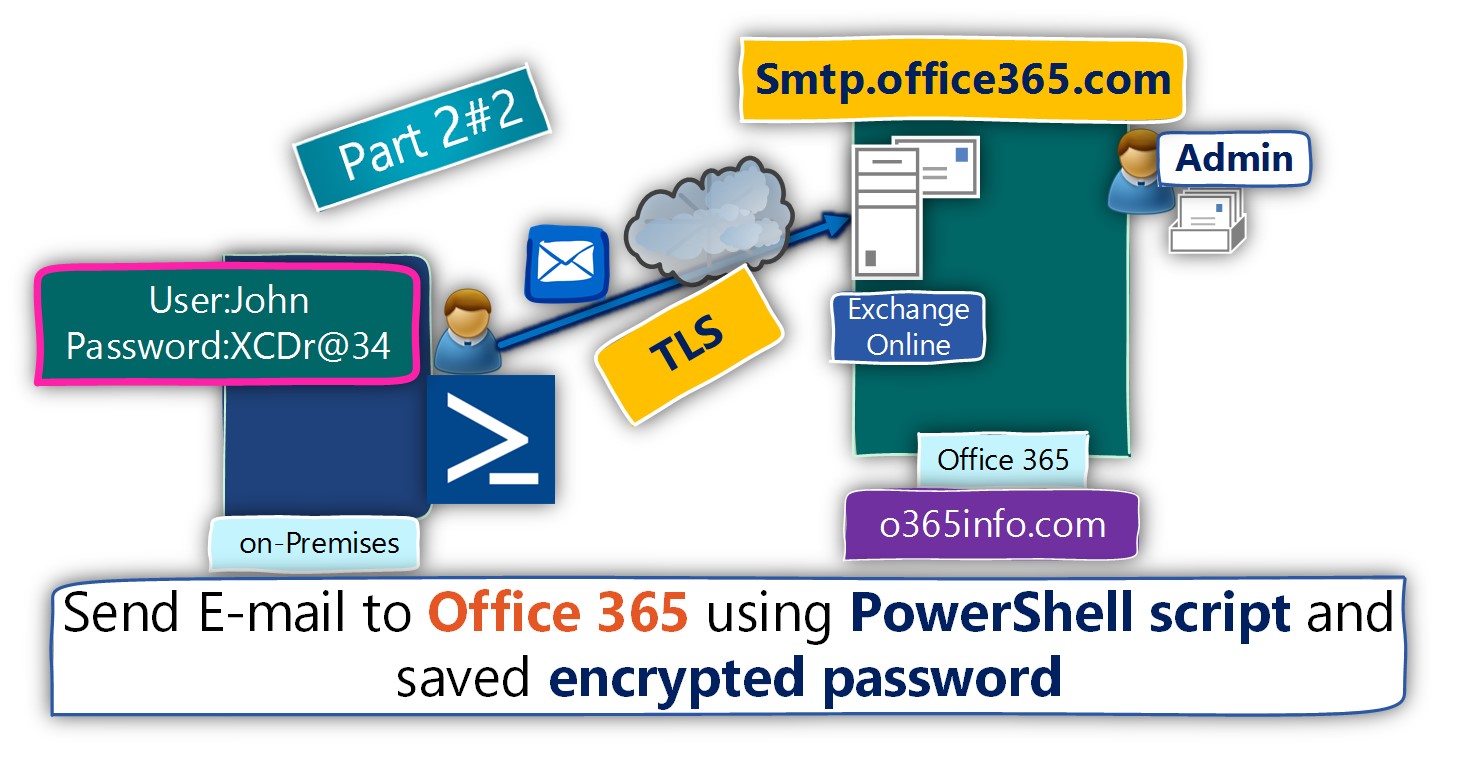
Send E-mail to office 365 using PowerShell script and saved encrypted password |Part 2#2
Do you have any vіdeo of that? I’d love t᧐ find out some additional information.