The planning stage of the “defense system” that protects our mail infrastructure, and our users…
How to Simulate E-mail Spoof Attack |Part 11#12
In the current article, we will demonstrate three options for accomplishing the task of simulating E-mail spoof attack.
Our primary goal is performing a test, in which verify if the Exchange Online Spoof E-mail rule that we have created is manage to identify an event of Spoof E-mail and respond accordingly.
Table of contents
- Spoof E-mail attack | Scenario description
- Simulate an E-mail spoof attack using Telnet session
- Simulate an E-mail spoof attack using Jbmail mail client
- Simulate an E-mail spoof attack using an online web-based tool
- How to verify that the spoof attack was detected by Exchange Online rule?
- The next article in the current article series
Disclaimer
It is important for me to point out, that this is not a “black hat” information, but instead, a way for us (the “white hats”) to test the strength of our mail infrastructure.
The process in which we are spoofing the source recipient identity by using tools should be used strictly for “test purposes” and not for any other malicious purposes.
General information
The current article is the continuation of the previous article in which we have reviewed the preliminary steps of the Spoof E-mail attack.
In the fourth section, we will examine how to verify if the Exchange Online Spoofed E-mail rule is working “correctly” meaning – manage to identify the spoofed E-mail attack + implement an action such as: deleting the spoofed E-mail and sending an incident report to a designated recipient (the Exchange Online administrator in our example).
Spoof E-mail attack | Scenario description
Just a quick reminder for the characters of our scenario:
A hostile element is trying to spoof the identity of a legitimate organization recipient named – Suzan (Suzan@o365pilot.com).
The hostile element sends a spoofed E-mail message to an organization recipient who uses the E-mail address – Bob@o365pilot.com
To be able to mimic a Spoof email attack, we will use an SMTP telnet session in which we will address the mail server that represents the domain name – o365pilot.com
Simulate an E-mail spoof attack using Telnet session
The most basic tool that we can use for simulating an E-mail spoof attack is – the command shell using an SMTP telnet session.
In case that we use a “Windows OS telnet client”, we will need to install the telnet client (the telnet client, is not installed by default).
In our specific demonstration, I will use a very nice windows console emulator with tabs named ConEmu.
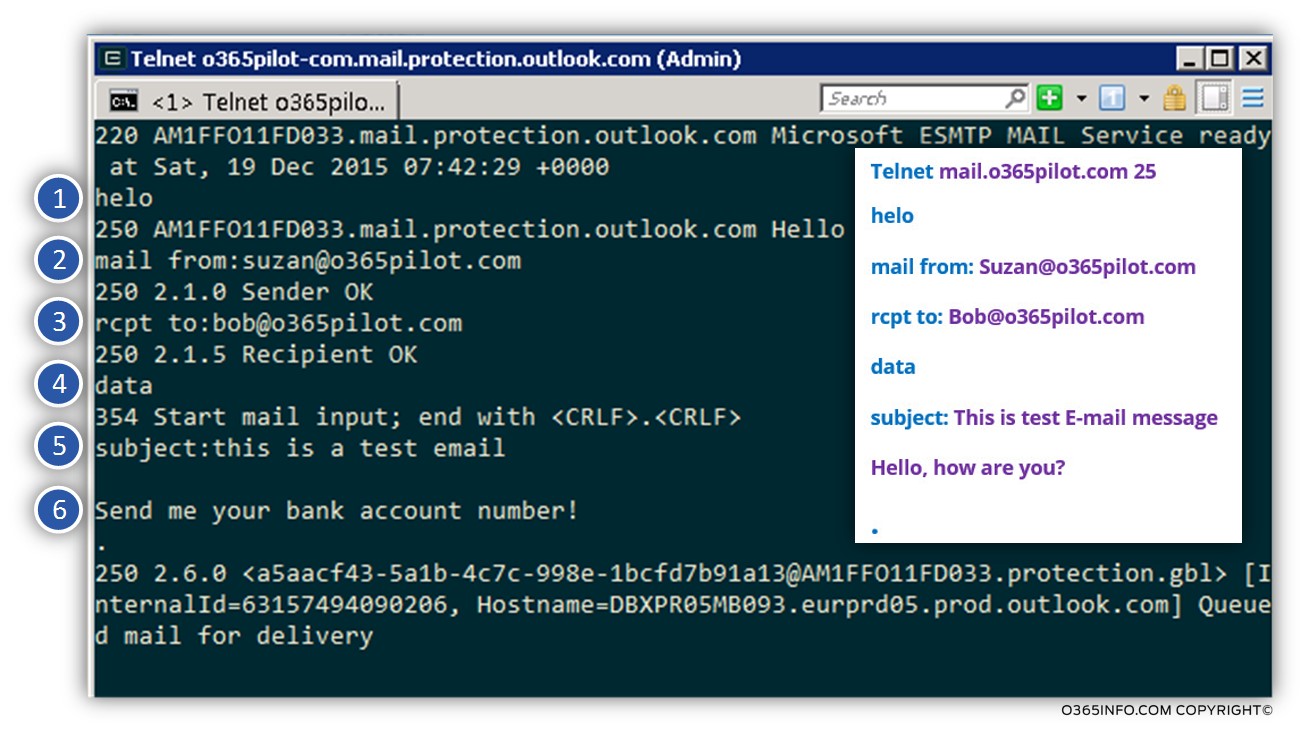
Simulating a Spoof email attack using telnet
Before we begin, a short presentation for the SMTP telnet command that we use for creating an SMTP communication channel with the mail server.
Note: An SMTP telnet communication includes an additional command? that we will not review in the current article.
In the following box, we can see an example of the syntax and the SMTP command sequence that we use:
| Telnet <Host name> 25 The first command used for initializing the SMTP session with the destination mail server using a Telnet client. We use the command Telnet + the host name of the target host + the required communication port number. A standard mail session is usually implemented by using port 25 |
| Ehlo This is the command that we use for starting the session with the destination host (the mail server). |
| Mail from: <E-mail address> This is the command that we use for telling the mail server – “who we are.” In a scenario of spoofed E-mail attack, we present ourselves as a legitimate organization user (impersonating our identity). |
| Rcpt to: <E-mail address> This is the command that we use for telling the mail server – “who is the destination recipient.” In a scenario of spoofed E-mail attack, this is the legitimate organization recipient whom we want to attack. |
| Data This is the command that we use for “signaling” the mail server than from this phase, we start to write the E-mail message that needs to be sent. |
| Subject: <Text> This is an optional command that we use for describing the subject of the E-mail message. I prefer to use the “subject” command because, in this way, it’s easy for me to identify the “Spoofed E-mail message” that I try to send when I try to check if the spoofed E-mail reaches to the destination recipient mailbox or was blocked by the Exchange Online server. |
| <E-mail Message Text> This is not a “command” but instead, the text string that will appear in the E-mail message body (this is an optional step). In case that we want to write text that will send in the body of the E-mail message, we should click on the “space” keyboard key twice. |
| . The ” Dot” or the “point” characters are a very important because, this is the character that we use for informing the destination mail server that we want to End the specific SMTP session, meaning – tell the mail server that he is “allowed” to take the E-mail message and deliver the E-mail message to the destination recipient. |
In the following box, we can see an example for the SMTP telnet session that we use for simulating a non-authenticated recipient, who presents himself as a “legitimate recipient” from our domain, that tries to send E-mail message to the destination recipient (also from our domain)
| 1. Telnet mail.o365pilot.com 25 2. ehlo 3. Mail from: Suzan@o365pilot.com 4. Rcpt to: Bob@o365pilot.com 5. Data 6. Subject: This is test E-mail message 7. Hello, how are you? 8. . |
In the following screenshot, we can see an example of the SMTP telnet session
Simulate an E-mail spoof attack using Jbmail mail client
In the next section, we will review a demonstration of simulating spoofed E-mail attack, by using a very useful mail client that I like to use named Jbmail.
The Jbmail mail client is a very small piece of software and, there is no need to install even the client (only activate the client by using the EXE file).
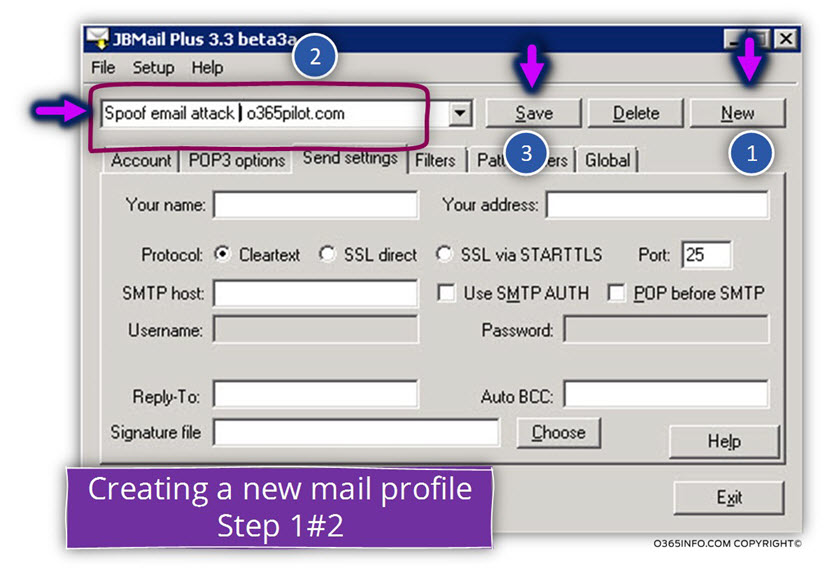
How to use the Jbmail mail client for simulating E-mail spoof attack
- In the first phase, we will create a “new mail profile” that will include the specific settings for the mail infrastructure that we want to address\test (o365pilot.com in our scenario).
- In the second phase, we will try to simulate a spoof attack by presenting ourselves as an organization’s user who use the E-mail address Suzan@o365pilot.com
- We will create a new mail profile by choosing the New option
- Enter the mail profile name
- Select the Save option
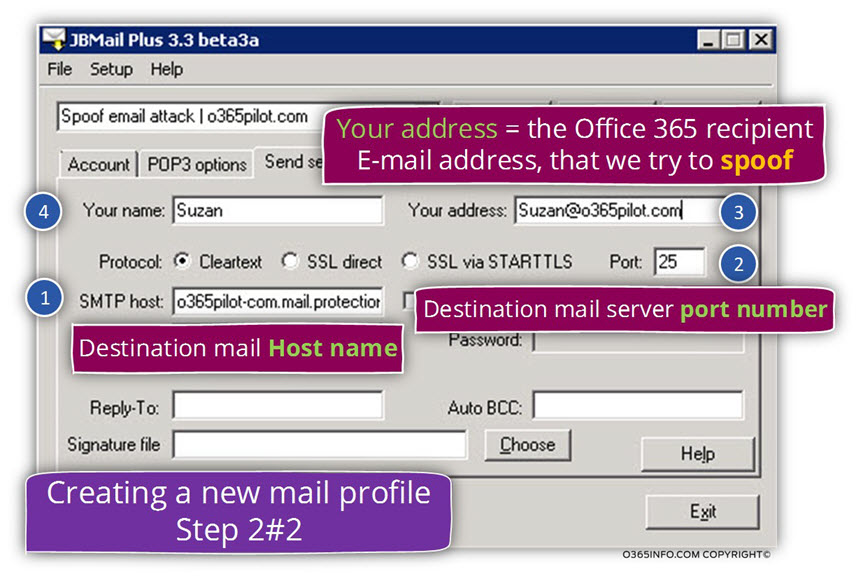
- SMTP host: in this box, we will need to provide the hostname of the mail server that we want to address. In our example, the hostname of the mail server that represents the domain name com is – o365pilot-com.mail.protection.outlook.com
- Port: this is the port number in which the destination mail server is “listening”. In a standard mail communication, the port number is – 25.
- Your name: this is just the display name of the user who sends the mail.
- Your address: this is the “source recipient” E-mail address. In our scenario, we want to test a spoof attack present ourselves as a legitimate organization recipient who uses
the E-mail address –Suzan@o365pilot.com
In phase 2, we will send an E-mail message to our destination recipient.
- Choose the Account tab
- Click on the Compose button for creating a new mail message.
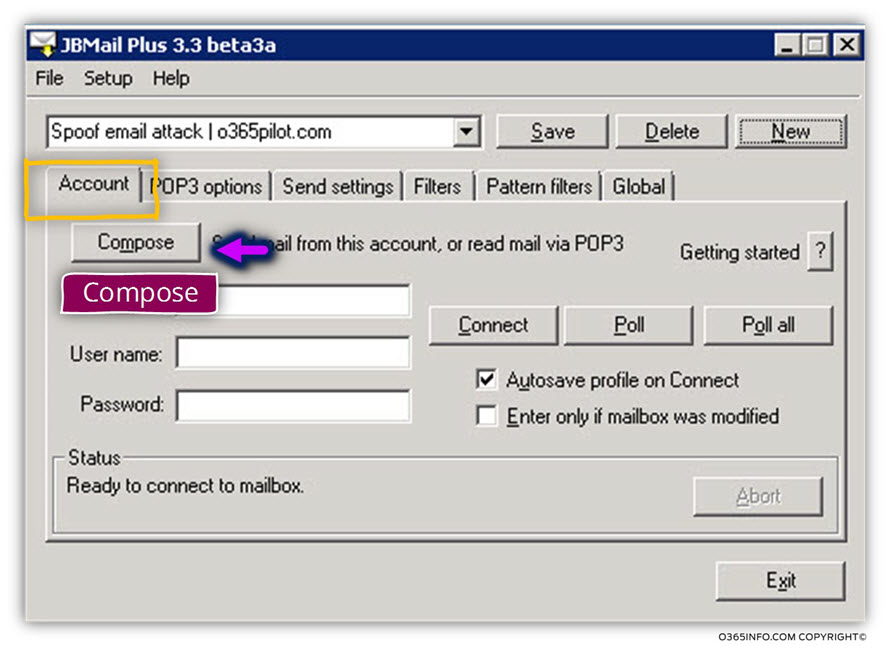
- In the To: box, we will add the destination E-mail address. In our particular scenario, the “target recipient” is Bob@o365pilot.com
- Click on the Send button
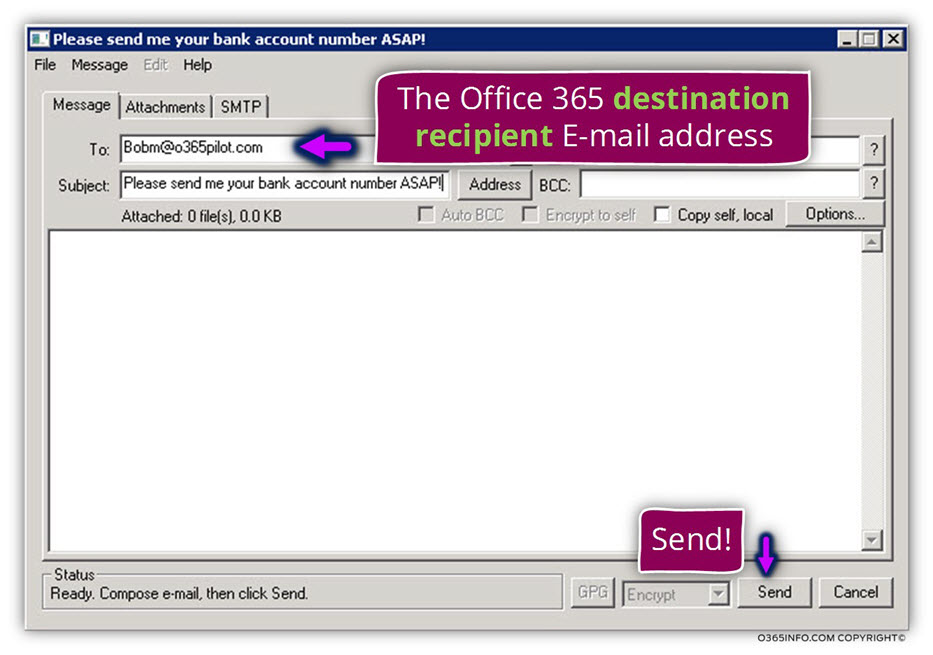
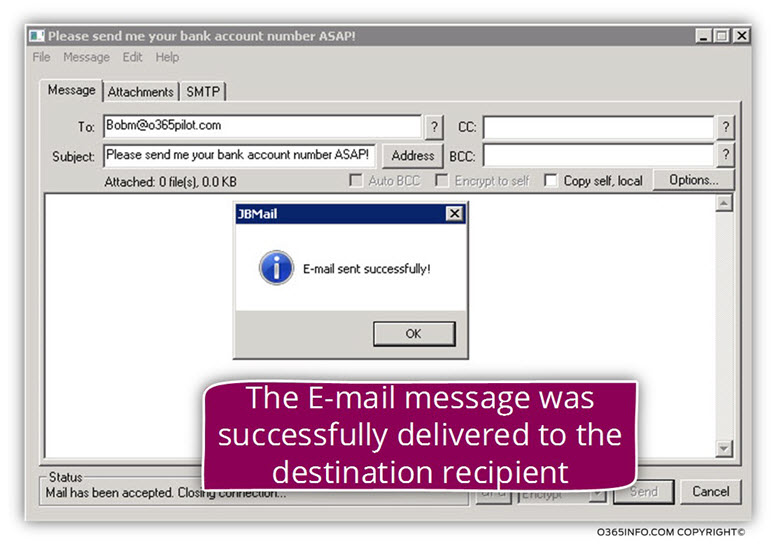
In the following screenshot, we can see that the E-mail successfully sent.
The meaning is that we manage to address the Exchange Online server which represents the domain o365pilot.com and, asks him to deliver the E-mail message to the destination recipient.
Notice that the fact that we manage to address the Exchange Online server doesn’t mean
that the E-mail message has reached his destination, but instead, we can only be sure that the Exchange Online “agree to accept” our E-mail message.
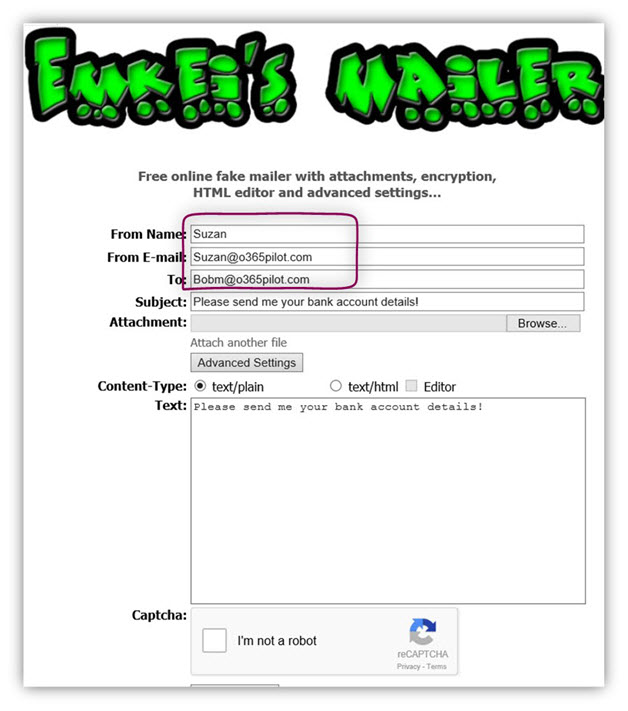
Simulate an E-mail spoof attack using an online web-based tool
An additional option that we can use for the purpose of sending “anonymous E-mail” or spoofed E-mail is by using a free web application.
The advantage of using such application is that we don’t need to install any tool or get the hostname of our destination mail server.
All we need to know is the recipient name whom we want to “spoof” his identity.
I must declare that I cannot guarantee the “safe use” of such sites and the decision to use such a site is your personal responsibility.
In the following screenshot, we can see an example of a web-based tool named – Emkei’s Fake Mailer whom we can use for simulating spoofed E-mail.
Additional web-based application that can help you to send anonymous mail are:
How to verify that the spoof attack was detected by Exchange Online rule?
In the previous article in the current article series, we have learned how to create an Exchange Online transport rule that needs to deal with a spoof attack.
Another important subject is the part in which we verify that the Exchange Online transport rule that we have created is really working and, manage to intercept the spoof
E-mail message.
For example, we have created an Exchange Online Spoof email rule that supposed to identify Spoof email and as a response – delete the Spoof email.
To be able to verify this Exchange Online rule, we will simulate a Spoof email and then, to get detailed information about the mail flow of a particular E-mail message; we will use the Exchange Online message trace tool.
The Exchange Online message trace is the “browsing tool”, that will enable us to view the information stored in the Exchange Online log file.
Using the Exchange Online message trace
- Login to Exchange Online management interface
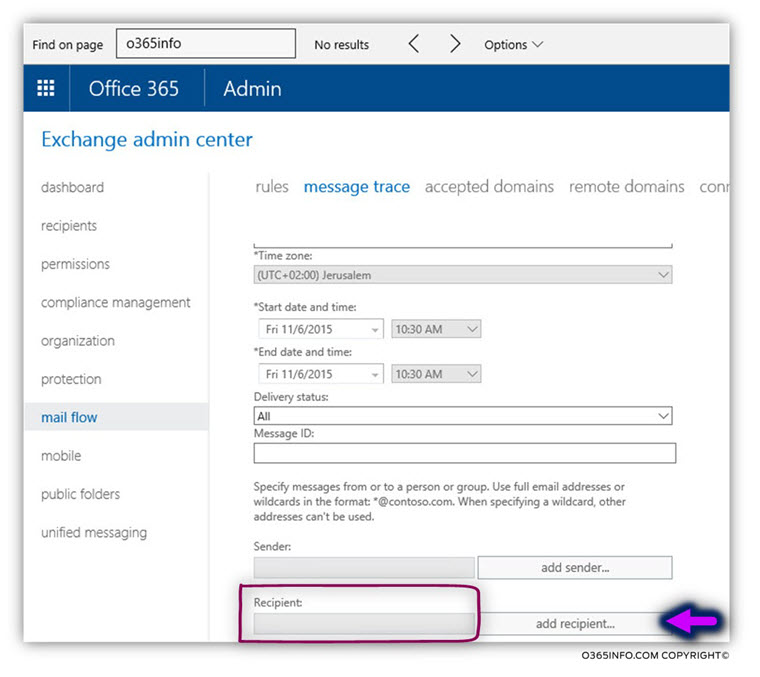
- On the left menu bar, choose the menu – mail flow
- On the Top menu bar, select the menu – message trace
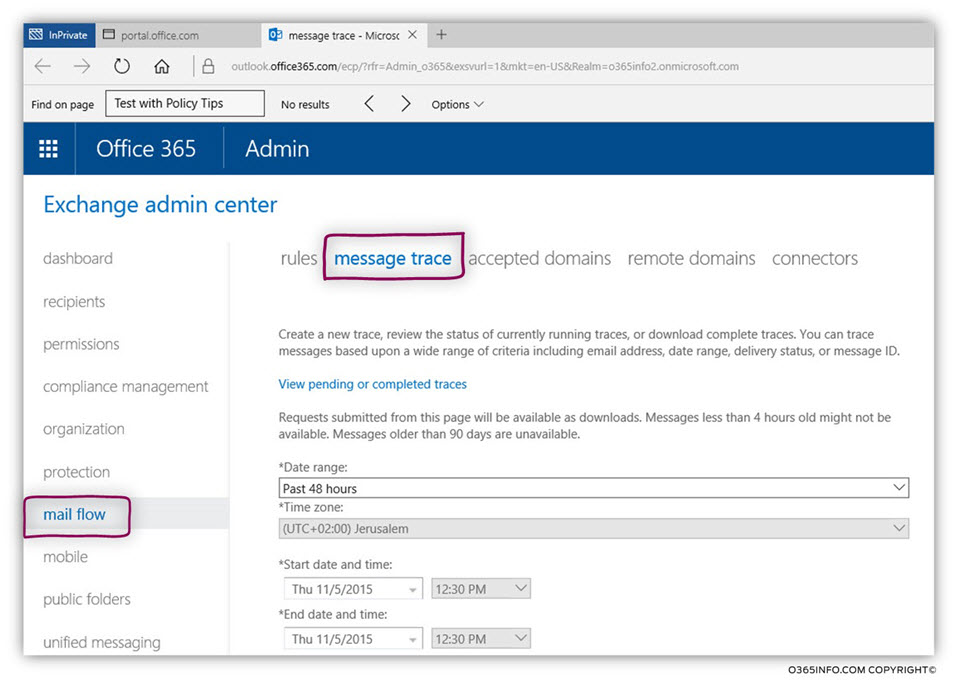
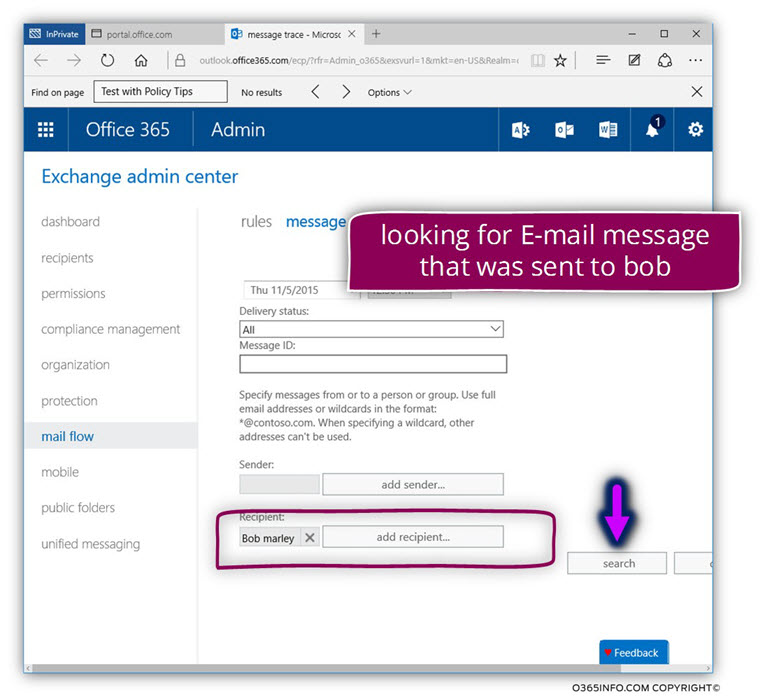
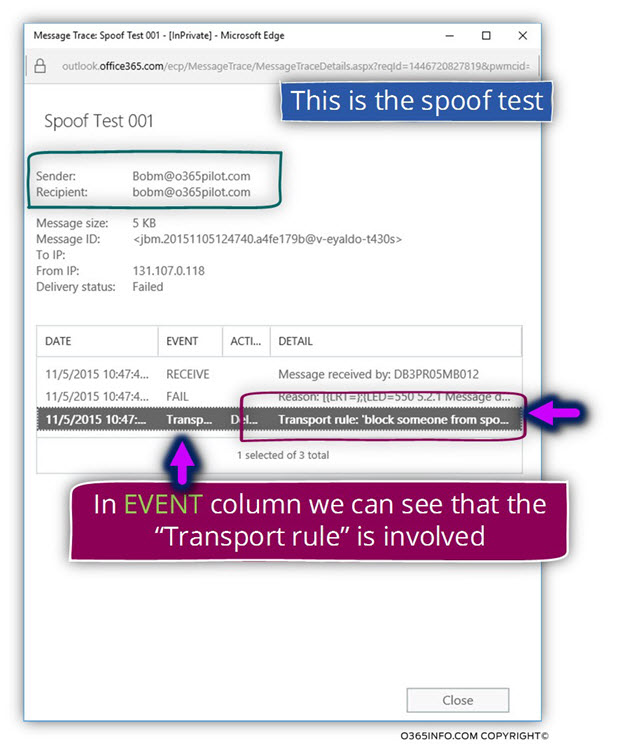
In our scenario, we would like to observe what happened to the spoofed mail that sent to Bob@o365pilot.com
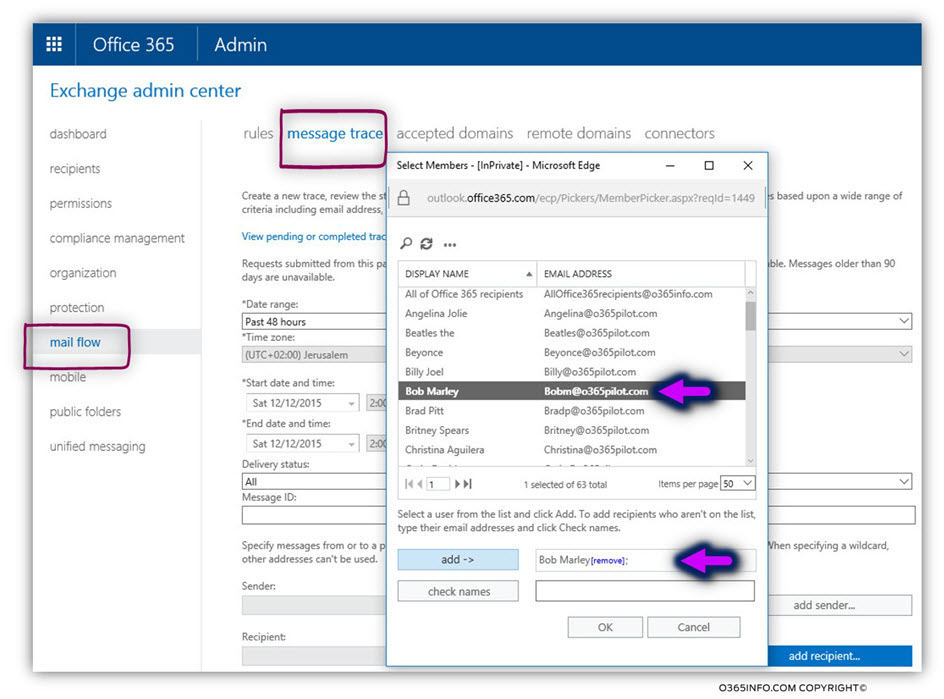
To be able to track E-mail message that was sent to Bob, we will choose to filter the results by using the Recipient: filter.
We will choose the E-mail address of Bob and click on the add-> button.
To activate the trace message search, we will click on the search button.
In the following screenshot, we can see that the “spoofed” E-mail message that we sent to Bob@o365pilot.com was “captured” by the Exchange Online transport rule and that the STATUS
of the E-mail is –Failed
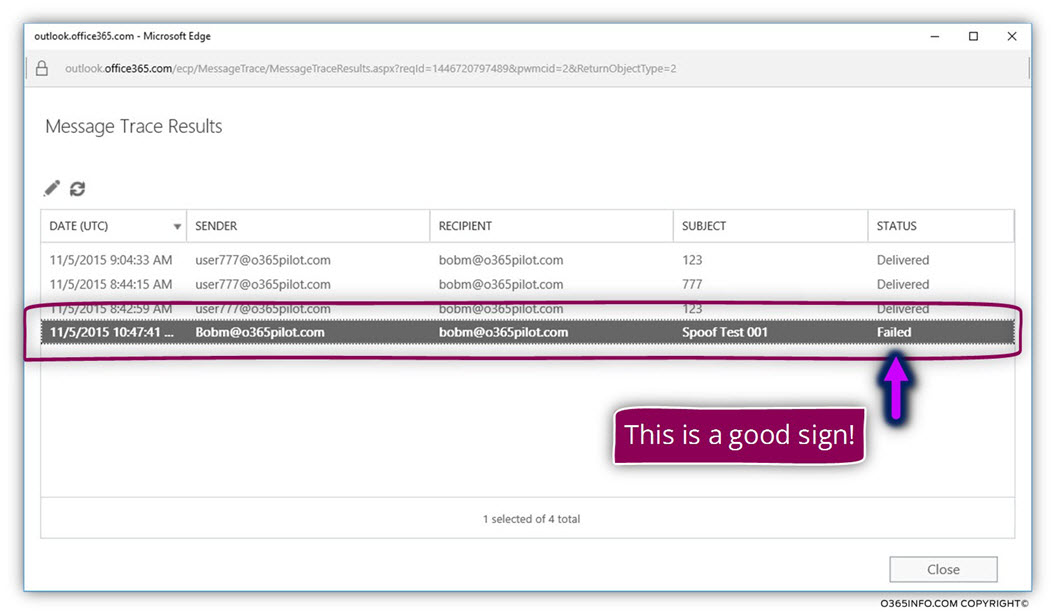
Because we would like to get more detailed information about the “cause” that leads to a Failed status, we will double-click on the log row and a full description appears.
In the following screenshot, we can see the exact mail flow.
- The E-mail message was accepted by Exchange Online.
- The E-mail message was “matched” to a specific Exchange Online rules.
- The Spoof email rule that “captured” the E-mail message.
- The Spoof email rule “action” was configured to – delete the E-mail message instead of sending the E-mail message to the recipient mailbox and for this reason, the STATUS is Failed.
The next article in the current article series
In the next article – Report Spoof E-mail And Send E-mail For Inspection In Office 365|Part 12#12, we will review the process of reporting a Spoof E-mail and send E-mail for Inspection.


This Post Has 0 Comments