In the current article and the next article: My E-mail appears as spam | Troubleshooting…
My E-mail appears as spam | The 7 major reasons | Part 6#17
The current article is the continuation of the previous article (My E-mail appears as spam | The 7 major reasons | Part 5#17) in which we continue to review the major reasons; that could lead to a scenario in which
E-mail that is sent from our organization, identified as spam E-mail.
In the current article, we will review the following causes:
- False positive
- User Desktop malware
- “Problematic” Website
Table of contents
4. False positive
Regarding the subject of internal \ outbound spam, the term “false positive”, relate to a scenario in which a legitimate E-mail is recognized by mistake as a spam \ junk mail.
Q: Is there an option to completely avoid a scenario of “false positive”?
A: Sadly, the answer is no. There are different “elements”, which can identify our organization E-mail by mistake as a spam \ junk mail.
For example, your E-mail message could be mistakenly classified as spam \ junk mail by a blacklist provider who recognizes aspects in your E-mail message that “look like” charters of spam \ junk mail (no system is perfect).
Another example could be: destination recipient looks at your E-mail message, and it seemed to him like a spam \ junk mail.
For this reason, he decides to report the particular E-mail message as spam \ junk mail.
In the following diagram, we can see that there could be “additional element” that could “decide” to identify a particular E-mail as spam \ junk mail such as – the mail user application or the security application that installed on the user desktop.
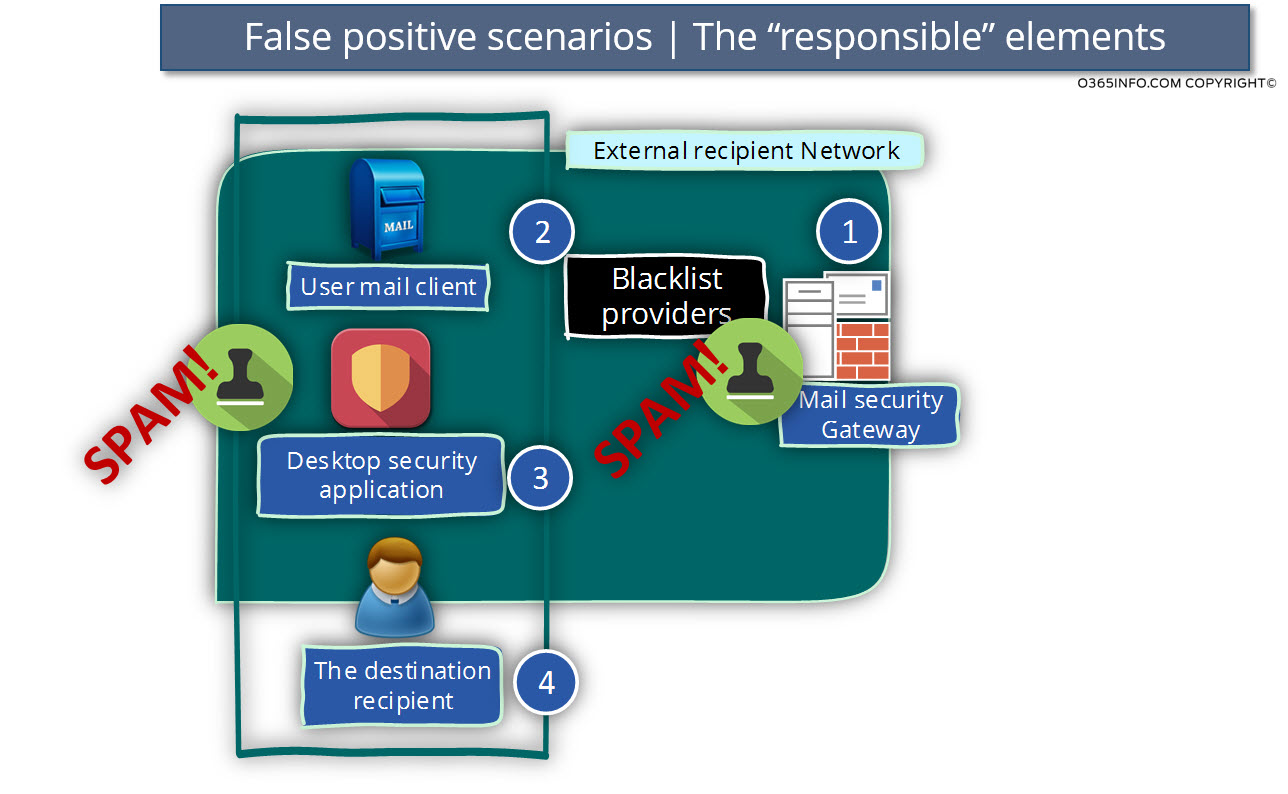
How to avoid?
There is no real method for “avoiding” this scenario. In case that legitimate E-mail that was sent by organization users is classified as spam \ junk E-mail by a particular blacklist, all we can do is to address the specific blacklist owner and ask to be removed from the blacklist.
Another best practice could be: implement a procedure, in which we check the “spam score” of commercial E-mail, before we send the specific E-mail message to the large group of recipients.
You can read more information about the option of testing your spam score in the article: My E-mail appears as spam | The 7 major reasons | Part 5#17
5. User Desktop malware
In case that the user desktop is infected with Malware (virus, spyware, etc.) the result can be a “stranger phenomenon” such as: mail that disappears, spam mail that sends from our organization recipient without his knowledge and so on.
One of the major charters of such a scenario (a scenario in which the user desktop is infected by Malware) is that the organization user is not aware that spam E-mail sent by his name to other recipients.

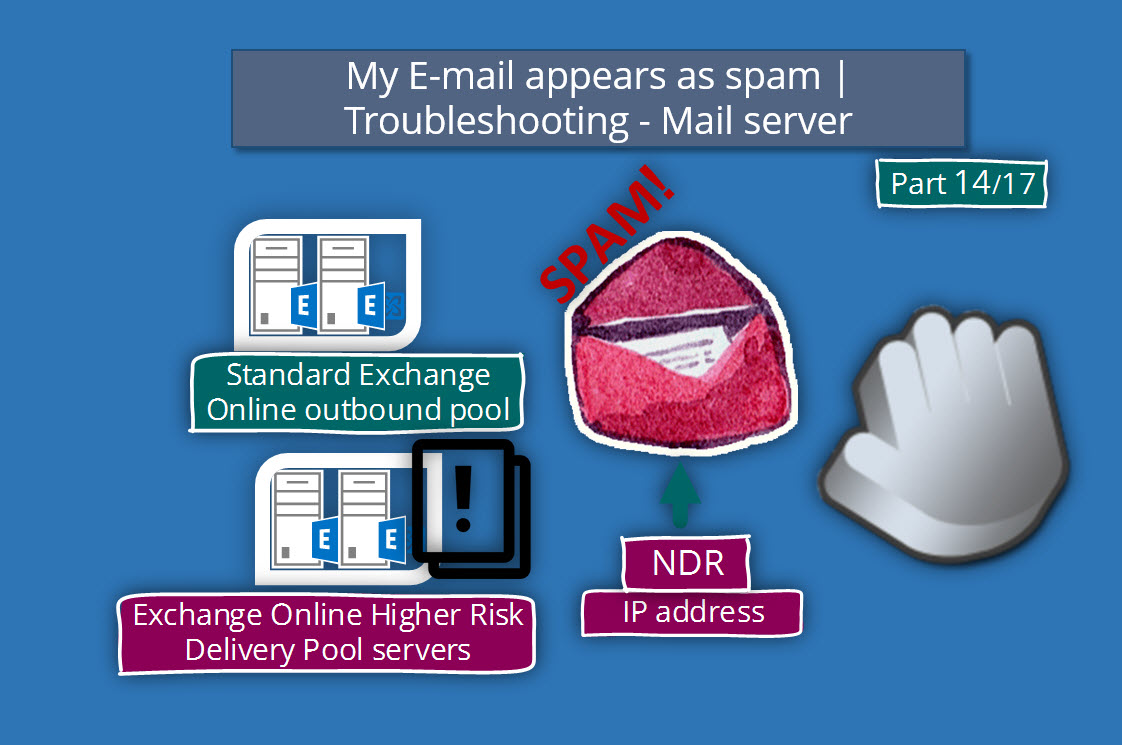
The “point” in which we become conscious of this issue is, only if the destination mail server replies using the NDR message or worse scenario, in which our organization appears as blacklisted.
In a scene of an “NDR”, it’s easy to implement the reverse engineering process in which we understand that the problem is related to a particular recipient organization.
In a scenario in which the “destination mail server” doesn’t reply using NDR or, in a scenario in which we found that our organization is blacklisted, there is no thread or “bread cramp” that could lead us to the “source of the problem.”
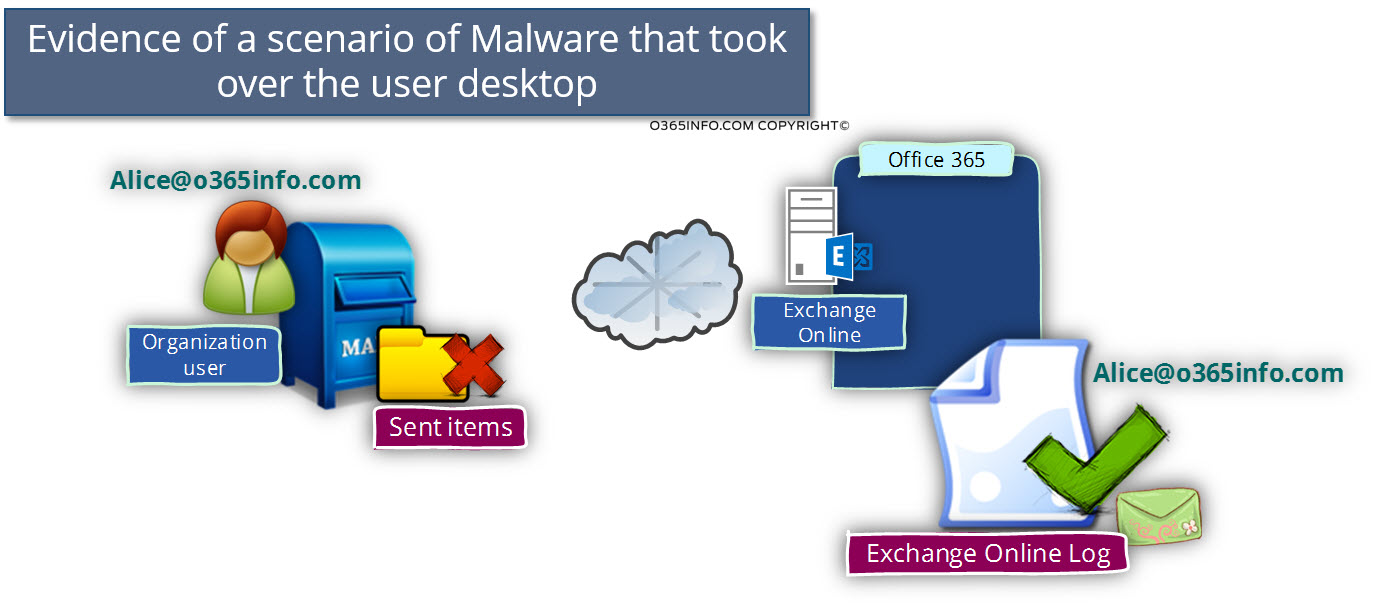
Q: How to recognize a scenario in which a user’s desktop infected with Malware that sends an E-mail message on behalf of the user?
A: There is no “magic formula” that will help you to capture this type of scenario. Our primary “weapons” is the awareness for the charters of this kind of scenarios (in which the user desktop compromised by malware that sends spam E-mail on behalf of the organization user).
One of the main charters for this type of scenario is “lack of coordination” between the evidence that exists in the user mailbox vs. the “evidence” that exists in the Exchange Online mail server.
For example – an organization’s user report about a strange phenomenon in which he gets the NDR message for E-mail that he didn’t send. The NDR message informs him that his E-mail was rejected by the destination mail server because he identified as spam / junk mail.
Note: There is another spam scenario that has similar characteristics named: NDR backscatter. In this scenario, the organization users get an NDR message that informs them that their “destination recipient” doesn’t exist. This is a scenario in which a spammer impersonated himself to a legitimate user from using our organization user identity.
When we start to investigate this strange issue by looking at the user mailbox and, in particular in the Sent mail folder, we cannot see any evidence to the mail that sent from the user mailbox.
The reason for this strange phenomenon is that most of the time, the malware will prefer to “cover his track” by deleting the E-mail that he sent from the sent item’s folder or by connecting the mail server directly and bypassing the desktop mail client.
The phenomenon becomes even stranger when we look at our Exchange Online message trace log and finds out, that the Exchange Online log includes information about dozens or even hundreds of E-mail messages that were sent by the specific organization user.
This scenario is a clear evidence of a situation of Malware that took over the user desktop and impersonated as a legitimate organization user.
Q: How to avoid a scenario in which organization user desktop can be compromised?
A: Verify that you implemented the basic security best practices that relate to the desktop user security:
- Verify that the desktop includes installation of antivirus software.
- Verify the antivirus software include all the last updates.
- Verify the antivirus software service is turned on.
Another option:
- Reset the organization user password
- Monitor the “problematic user” activity by using the Exchange Online message trace log.
For example, look at the Exchange Online log and try to locate a “strange behavior” in which there are many E-mails that are sent “by the user” to unknown E-mail address.
6. “Problematic” Website
Another interesting and unknown reason for classifying E-mail as a spam \ junk mail is related to the website address (URL) that appears in E-mail message.
Exchange Online and other mail server are using the services of a special blacklist provider, such as: SURBL that specialized is a specific “realm” that focused on a URL address that considers is “problematic URL address” and that appear in a user E-mail message.
Attached a quotation from the surbl website:
SURBLs are lists of websites that have appeared in unsolicited messages. Unlike most lists, SURBLs are not lists of message senders.
I have read the information on the website that explains the method that used and I must admit, that I’m sure that I completely understand the full concept of the “methods” that are utilized by the surbl service.
As I understand it, the first step that is implemented by the surbl service is to – create a list of public web sites that their name (their URL address) appears in E-mails that was classified or identified as spam \ junk mail.
The fact that a particular website URL address “appear” in unsolicited E-mail messages, “stamp” this website “suspicious”.
In case that user sends an E-mail, which includes the URL address of a website that appeared on the list of “suspicious website”, the E-mail could be considered as mail item that contains spam content.

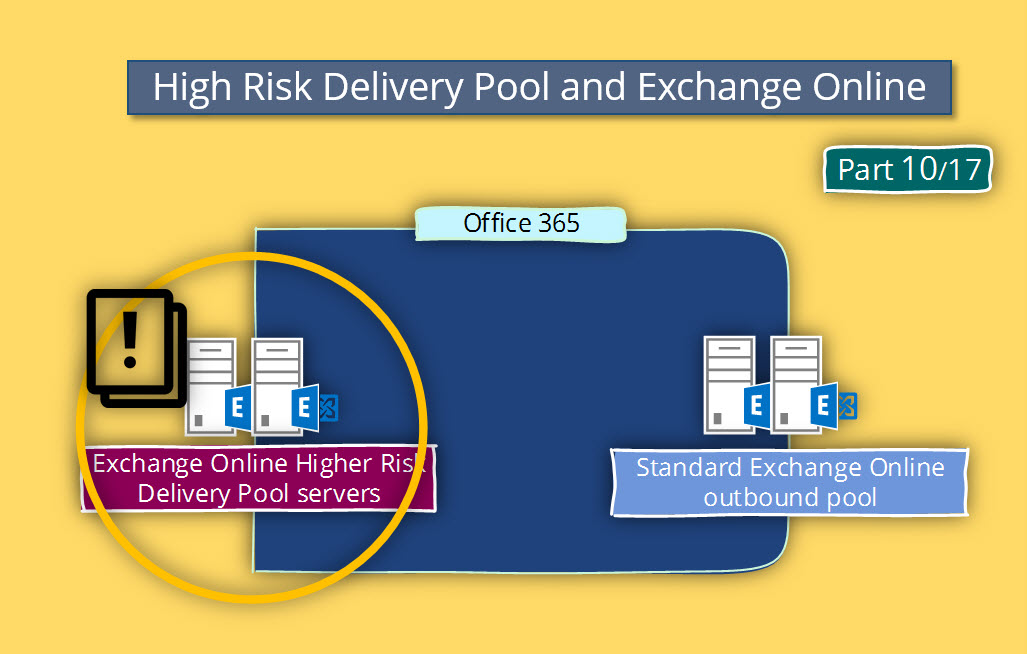
Non-Office 365 and Exchange Online issues
Under the subject of – “factors and element that can lead into a scenario in which E-mail that is sent from your organization could be identified as spam \ junk mail” there could be additional causes that we didn’t review.
The reason that we have not reviewed these factors is – because that in Office 365 and Exchange Online this element cannot realize.
An example of such causes could be:
A mail server that is hacked by spammers, a mail server that configured as an open relay, Mail application that doesn’t use standard or non-RFC compliant SMTP protocol, missing MX record, missing PTR records, using a dynamic IP address as the IP address of the mail server and more.
Although in Office 365 and Exchange Online we should not be concerned about the above issues, in case that we manage a “private mail infrastructure” it’s important to be aware of this potential problem.
This Post Has 0 Comments