In the current article, we will review the options that are available for analyzing the…
Configuring exceptions for the Exchange Online Spoof E-mail rule | Part 3#12
In this article, we will review the subject of how to create an Exchange Online rule exception. As the name implies, the “exceptions” part of the Exchange rule was created to prevent the execution of the Exchange Online rule in a specific scenario.
In the current article, we will continue to use the scenario we reviewed in the previous article.
Table of contents
Just a quick reminder for our scenario requirements:
- We want that Exchange Online will scan incoming E-mail message and identify
E-mails that look like spoofed E-mail. - We don’t want to delete the E-mail messages that identified as spoofed E-mail, but we want to inform a designated recipient about this E-mail, and we want to be able to send a copy of “original E-mail message” that identified as spoofed E-mail.
The “trigger” that will activate the Exchange Online “Spoofed E-mail rule” will be based on the following two conditions (a combination of condition 1 + condition 2):
- An incoming email message that sent to a non-authenticated recipient (recipient who doesn’t provide user credentials).
- The recipient present himself by using an E-mail address that includes our public domain name. In our specific scenario and E-mail address that include the domain name – o365pilot.com
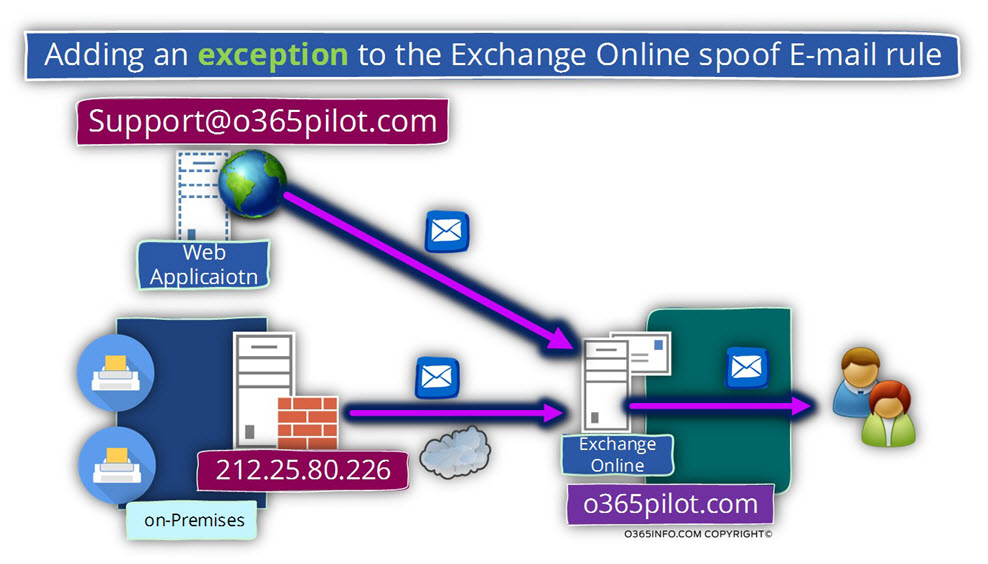
The way we define the characters of a spoofed E-mail poses a problem because part of our mail flow infrastructure based on a web application and mail-enabled devices that address Exchange Online serve as “their mail server” but, without providing any user credentials (anonymous session).
In case that we “activate,” the Exchange Online Spoofed E-mail rule that we have created in the previous article, the mail that is sent by this host will be identified as spoofed E-mail.
The good news is that we can use the required Exchange Online Spoofed E-mail rule + add to the rule a specific instruction in which the rule will not be applied to as specific hosts or in other words, define an Exchange Online rule exception.
The description of the hosts/services that will be excluded from the Spoof email rule
In our specific scenario, the next hosts are addressing Exchange Online as their mail server by using and “anonymous SMTP session” (without providing user credentials):
- External web application – our organization uses, a web application that sent E-mail messages to organization users. The web application sends E-mail messages using the E-mail address – support@o365pilot.com. The web application doesn’t provide any user credentials.
- Mail-enabled devices – the organization’s network includes a mail-enabled device such as scanners and printers, which uses Exchange Online as their mail server. The mail-enabled device doesn’t provide any user credentials.
Theoretically, when we will “activate” the Exchange Online Spoofed E-mail rule, each E-mail message that will be sent by these “entities”, will be considered as spoofed E-mail and in a response Exchange Online will generate and send an incident report to the designated recipient’s.
We wish to prevent this scenario by “telling” Exchange Online, that in case that the E-mail sent by one of these hosts (the web application or the mail-enabled device that located on our network), Exchange will “ignore” this E-mail.
Adding the required exceptions to the Exchange Online Spoof email rule
In the following section, we will demonstrate how to add exceptions to the Exchange Online Spoof email rule reviewed in the previous article.
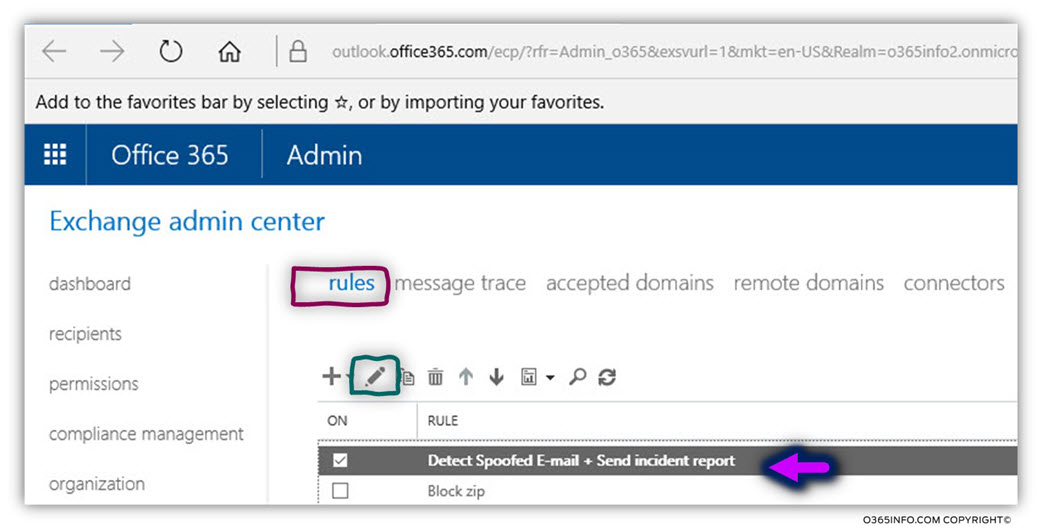
- Log in to the Exchange admin portal
- On the left menu bar, choose – mail flow
- On the top menu bar, choose – rules
In our specific scenario, we will select the rule named – Detect Spoofed E-mail + Send an incident report (the rule reviewed in the previous article).
We will select the pencil icon for editing the rule
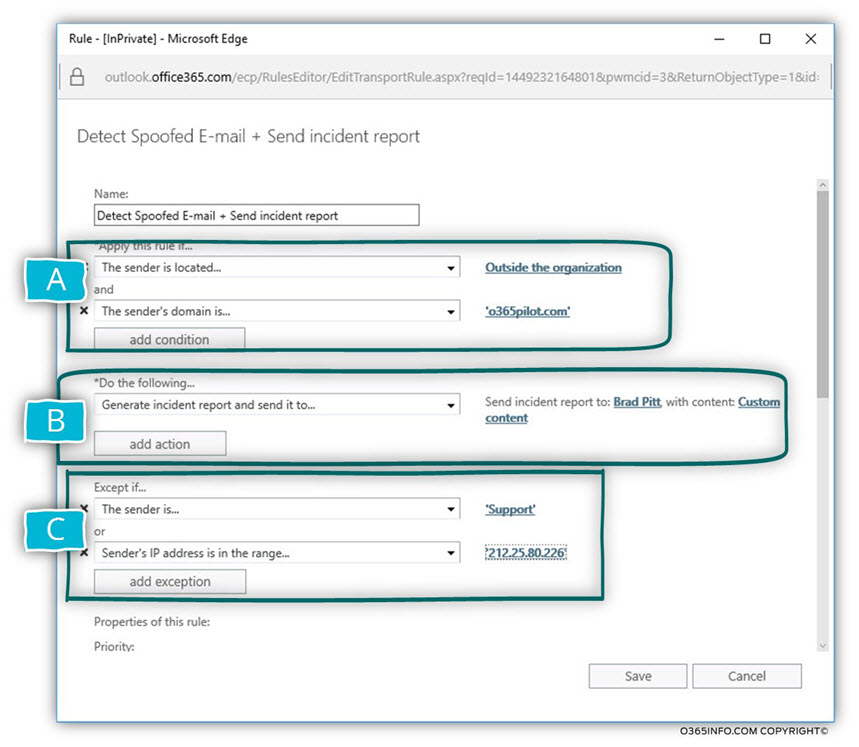
In the following screenshot, we can see the structure of the Exchange Online rule.
In the current scenario, we will edit the “third part” that enable us to define some exceptions to the rule.
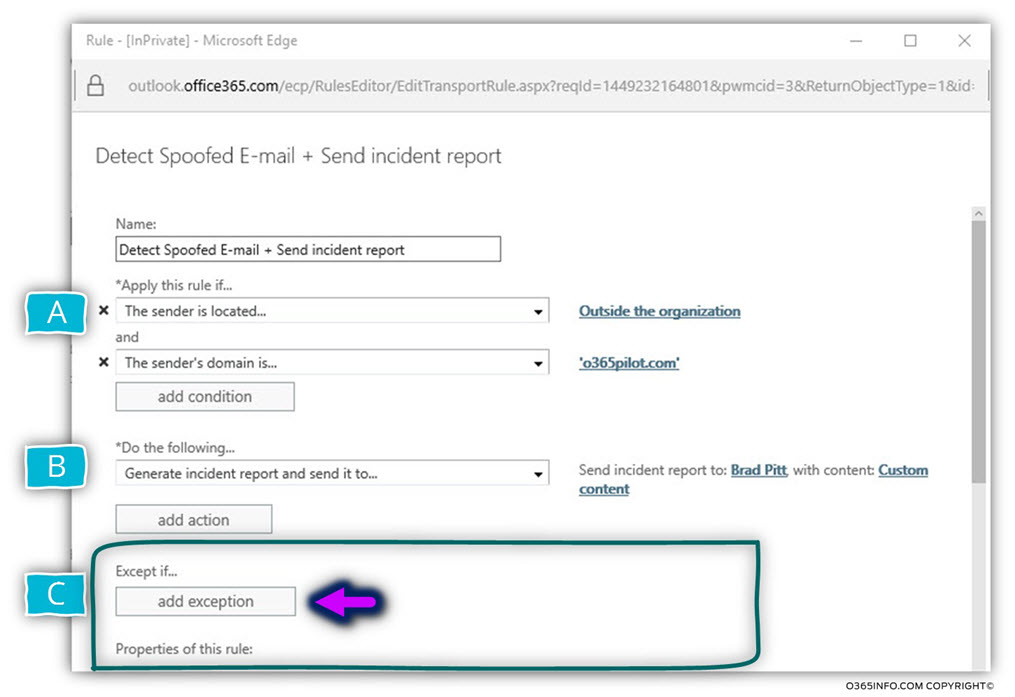
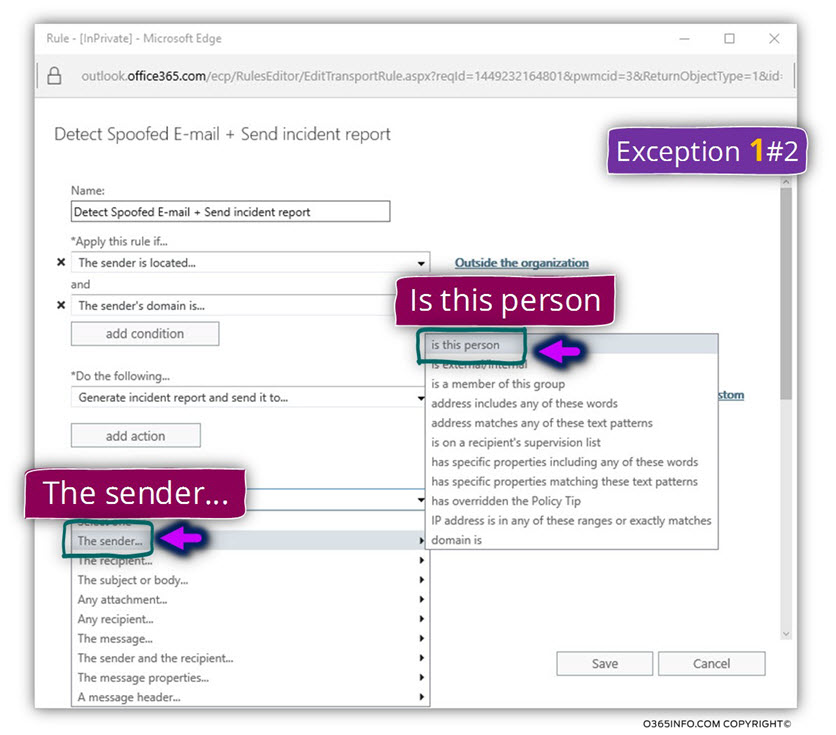
Configuration exception 1#2 – exclude the external web services that use the E-mail address – support@o365pilot.com
Click on the option – add exception
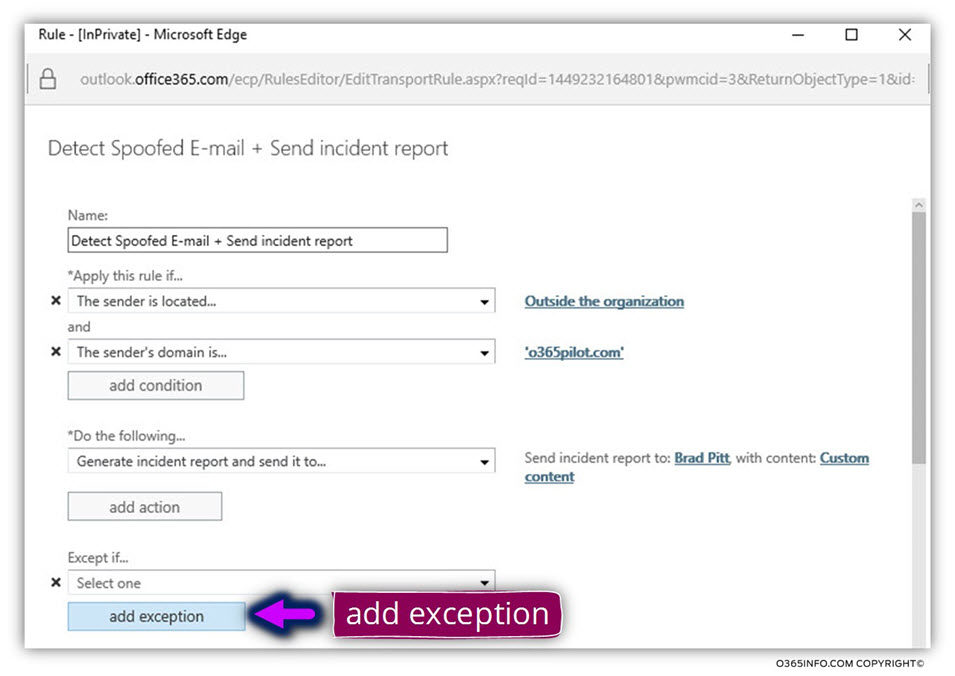
- In the section named – Except if…, Click on the small black arrow
- Choose the menu – The sender…
- In the submenu, choose the menu – Is this person
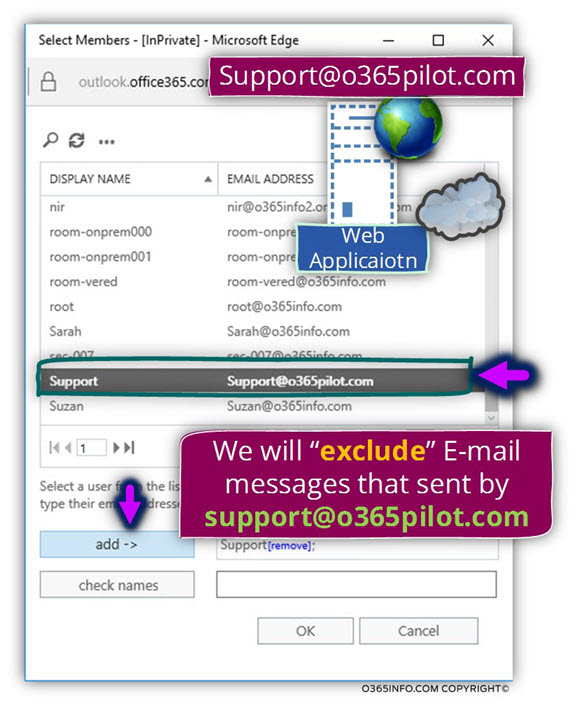
In our specific scenario, the “person” is represented by the E-mail address – Support@o365pilot.com
Select the required E-mail address and click on the add-> button
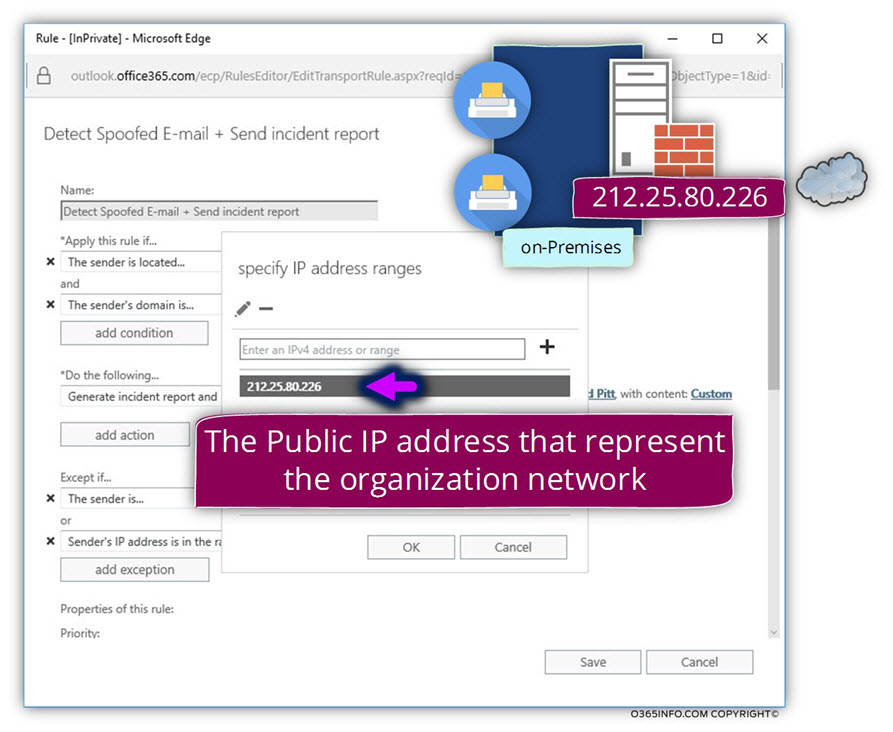
Configuration exception 2#2 – exclude the mail-enabled host represented by the IP Address 212.25.80.226
In this section, we will add the second exception that “defines” all the mail-enabled hosts that are located on our company network that is represented by the public IP address – 212.25.80.226
Click on the option – add exception
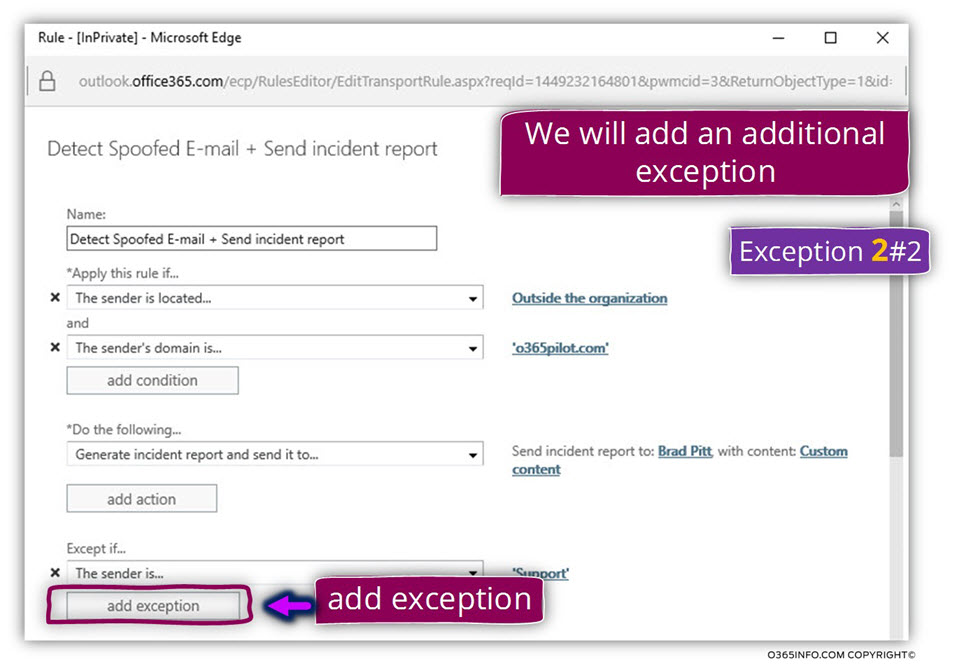
- Under the section named – or, click on the small black arrow
- Choose the menu – The sender…
- In the submenu, choose the menu – IP address is any of these ranges or exactly matches
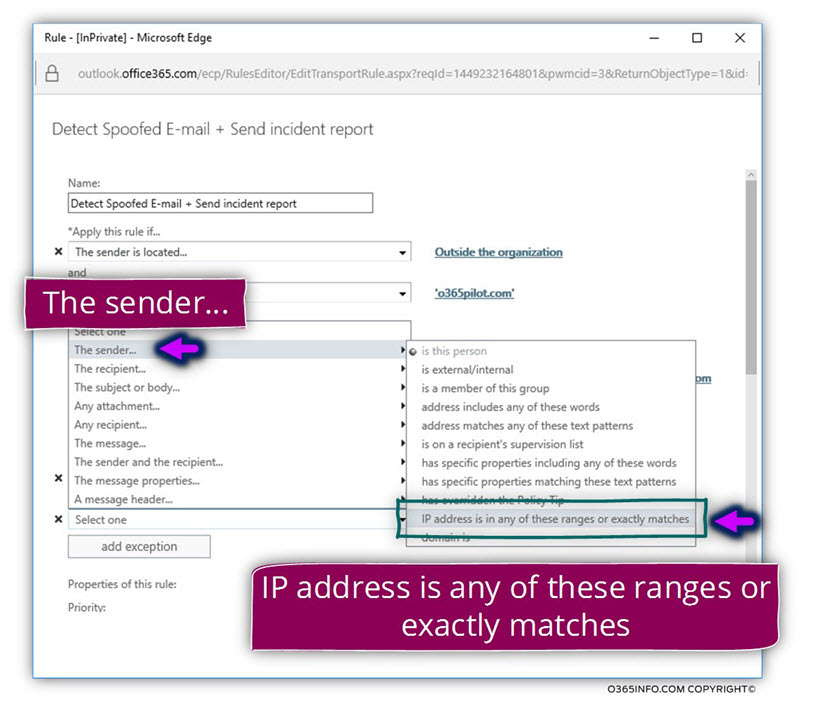
In the text box – specify IP address ranges, we will add the Public IP address that represents the organization’s network
In the following screenshot, we can see the “final result” – an Exchange Online rule that consists of three separate parts:
- The first part (A) defines the condition in which a specific E-mail message will be classified as a spoofed E-mail message.
- The second part (B) defines the action that will be “executed” by Exchange Online when he recognizes a specific E-mail message as “spoofed E-mail message”.
- The Third part (C) defines the exception for the condition which is used in part A.
The next article in the current article series
In the next article – Detect Spoof E-mail And Mark The E-mail as spam Using Exchange Online Rule |Part 4#12, we will review how to create an Exchange Online rule that will identify events of spoofed E-mail and, as a response will raise the SCL value of the Spoof E-mail.


This Post Has 0 Comments