In the current article, I would like to review the chain of events that occurs…
What are the possible damages of Phishing and spoofing mail attacks? | Part 2#9
We are living in a dangerous world that produces many types of threats and risks to our organizational mail infrastructure, to our users and us.
In the current article, I would like to review some of the possible damages that we can experience in a scenario, in which Spoof or Phishing mail attacks realized.
Table of contents
- The great market of mail threats, possible damages and Phishing mail attack
- The existing threats and risks to your mail infrastructure.
- The possible damages of Phishing mail attack
- Why do I want to focus on Spoof mail and Phishing mail attacks?
- A little about Spam mail before we continue with the subject of Spoof E-mail attacks and Phishing mail attacks.
- Spam mail, a very brief review
- The next article in the current article series
The great market of mail threats, possible damages and Phishing mail attack
Regarding the threats and risks to our mail infrastructure, there are a variety of threats which we should be aware of and prepare accordingly.
So why did I prefer to talk about the specific threat describe as “Phishing mail attack”, and his relative – the Spoof mail attacks?
The reason is that Phishing mail attacks are fascinating from the risk management and security perspective and very challenging from the “possible solutions” perspective.
Phishing mail attacks are the representative of a modern threat that belongs to the famous family of advanced threats
The main character of Phishing mail attacks is, that this type of attack considered as a very sophisticated attack that can cause severe damage.
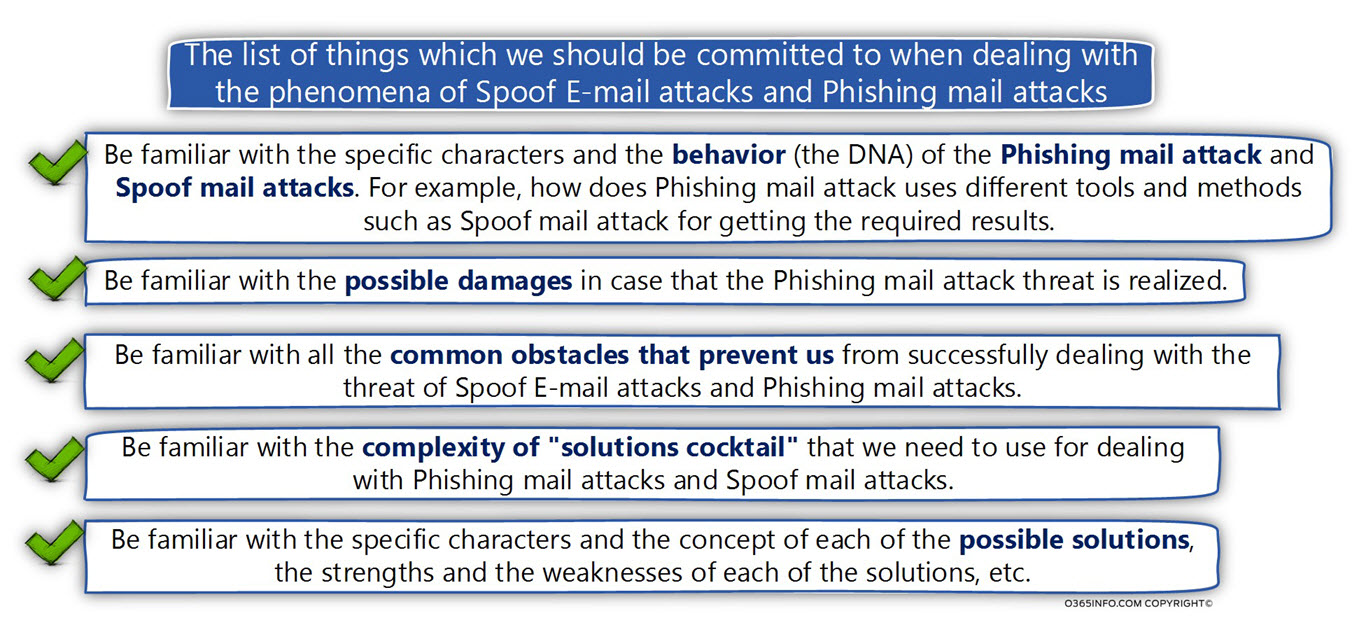
To be able to protect our users and our organization from the threat of Phishing mail attack, we will need to complete a couple of phases:
- Be familiar with the specific characters and the behavior (the DNA) of the Phishing mail attack and Spoof mail attacks. For example, how does Phishing mail attack uses different tools and methods such as Spoof mail attack for getting the required results.
- Be familiar with the possible damages in the case that the Phishing mail attack threat realized.
- Be familiar with all the common obstacles that prevent us from successfully dealing with the threat of Spoof E-mail attacks and Phishing mail attacks.
- Be familiar with the complexity of “solutions cocktail” that we need to use for dealing with Phishing mail attacks and Spoof mail attacks.
- Be familiar with the specific characters and the concept of each of the possible solutions, the strengths and the weaknesses of each of the solutions, etc.
Bottom line
To acknowledge that the subject of Phishing mail attack is a severe threat that needs our full attention.
The existing threats and risks to your mail infrastructure.
The modern mail environment includes a variety of “risks” and “threats” that we need to deal with.
A very general classification of these “mail threats” could be:
Mail attacks | Threats and risks that are executed by hostile elements.
This type of these “threats” executed by a hostile element; that tries to exploit existing vulnerabilities of our mail infrastructure, or the vulnerabilities our users.
The results of such attacks could be a minor damage – such as the cost of spam mail in which the damage is the harassment of our users, by sending mail that includes inappropriate content, such as advertising persuasion to purchase products, which will increase certain body organs.
The other side of the story could be mail attack such as a Phishing mail attack that can cause severe damage such as: stealing intellectual property, stealing money, stealing passwords, infects our infrastructure with malware and so on.
As an example, we can mention the following mail attacks:
- Spoof E-mail attacks – a scenario in which hostile element uses a false identity, usually an identity of a “trusted sender” in which the victim can trust.
- Phishing mail attacks –attack that can be described as – advanced or sophisticated attack, which combines a variety of methods such as – Spoof mail, social engineering, Phishing website, malware and so on for attacking the victim.
- Spam mail attacks – spam mail that can flood the organization mail infrastructure harasses and annoying mail users.
- Malware – a hostile code that could cause a minor damage, but at the same time, can cause a huge damage.
Another type of threats and risks
- Data leak – a scenario in which sensitive information is leaking by using the organization mail infrastructure as a “bridge”.
- Data privacy, data confidentiality, and data integrity – a scenario in which hostile element access data that transferred via the communication line, etc.
- Availability of mail infrastructure – a situation in which the necessary need of 7 X 24 availability of the organization mail infrastructure may be affected by various factors such as – failure of the mail server’s hardware, failure of communication lines and so on.
Although each of this “mail threats” that mentioned above is – an Important and respected threat, in the current article series, I would like to focus on the subject of “Mail attacks” and especially on the subject of Spoof mail attack and Phishing mail attacks.
The possible damages of Phishing mail attack
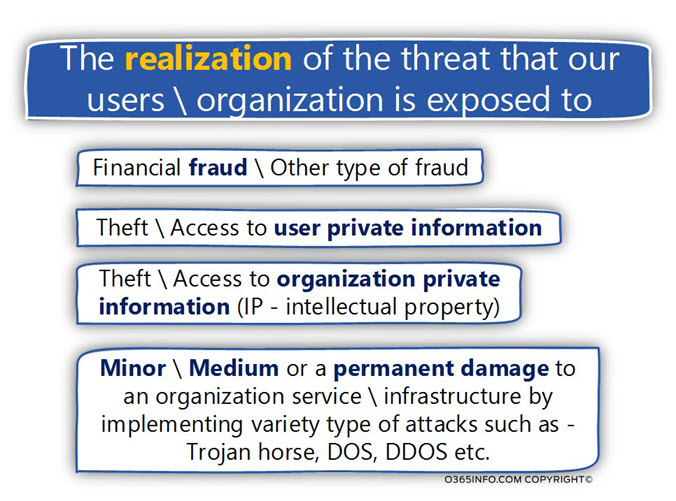
One of the most “interesting” characters of Phishing mail attack is, that there is a wide range of “damages” that could be realized by the Phishing mail attack.
The type of the “damage” depends on upon the creativity and imagination of the attacker.
Just in case, I would like to review the most common results from the Phishing mail attack:
1. Fraud
Under the section of “fraud,” there are a variety of possible types of scams, for example – Finical fraud, in which the victim is seduced to deposit money in the attacker bank account.
2. Theft / Access to user or organization private information
A scenario in which hostile element gets access to private information about the victim such as user password, bank account number and so on.
Another option is – A scenario in which hostile element gets access to the organization private data by using the victim as a “bridge” to enter that protected organization perimeter.
3. Variable type of “damages” to the organization infrastructure
I use this vague definition because the severity of the possible damage that can be caused by the attacker depend on upon the type of the Phishing mail attack that executed.
For example, the Phishing mail attack can tempt the victim to download and activate a particular file that is a malware such as – Trojan horse.
The damages that can be caused by a Trojan horse can be a minor damage such as in a scenario in which the Trojan horse serves as an adware (collect information about the user habit, etc.) Or can be translated into a severe damage in which the Trojan horse serves as a back door for the attacker, that take control on the victim’s desktop, and uses the victim’s desktop as a “bridge” to the rest of the organization infrastructure.
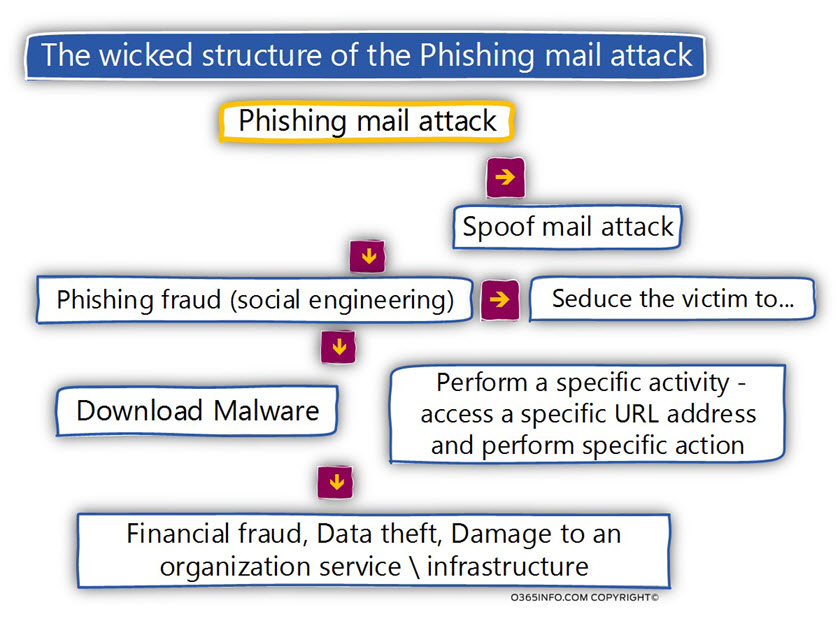
The wicked structure of the Phishing mail attack
As mentioned, the Phishing mail attack considered as a sophisticated attack which combined many malicious methods for implementing a successful attack.
For example, in a typical Phishing mail attack, the attacker will use a spoofed sender identity, which looks like trusted sender identity that the victim can trust.
The E-mail message content will include some “narrative” which based on social engineering methods; that will address a specific human vulnerability or a particular human character. This content will seduce and lead the victim “to do something” such as – download and open a particular file, click on a specific link that will lead the victim to a Phishing website and so on.
The result of the “user action” (the victim) could be data theft, money fraud, infect the user desktop with malware, etc.
What is my point?
My point is that if we manage to “catch the head of the snake”, we can avoid from the of a snake bite!
If we use a less metaphorically description – in case that we manage to identify and block the Spoof mail attack and Phishing mail attacks, we can prevent the painful results from the attack.
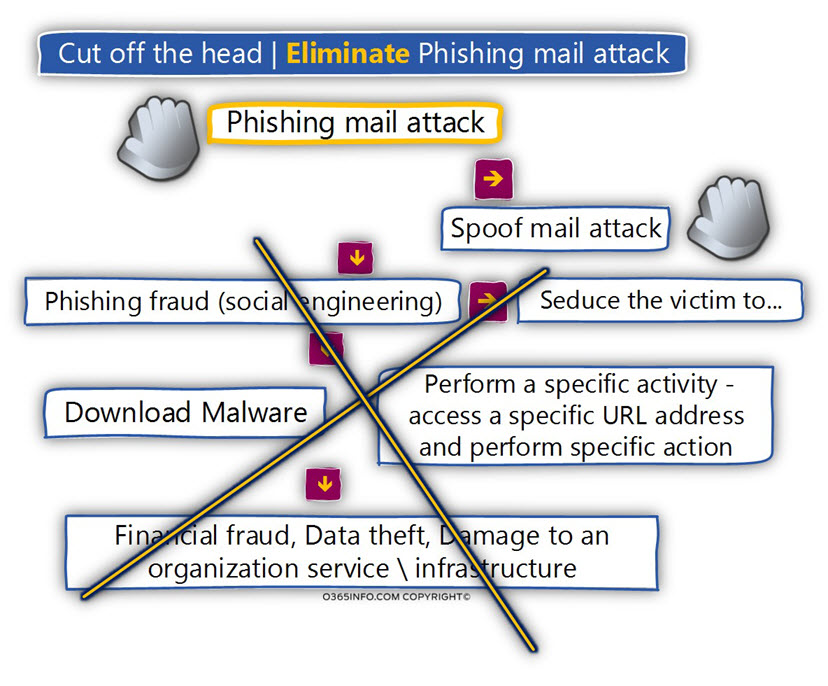
For example, along the current article series, we will review in details the subject of – “Spoof mail attack”.
We will discuss the characters of Spoof mail attack, and the way that we can use for dealing with a Spoof mail attack (by implementing sender verification mechanisms).
The Spoof mail attack doesn’t have a “life of its own”.
The meaning is that from the attacker’s point of view, the ability to spoof the sender’s identity, have a “value” only as “bridge” which will pave the way for the “reset” of the Phishing mail attacks.
In case that we will be able to identify and block most of the Spoof mail attack, the derivative is that we also be able to block most of the Phishing mail attack!
An important observation is that not all the Phishing mail attack uses Spoof mail attack and also, there is not guaranty that we will be able to identify 100% of Spoof mail attack.
Why do I want to focus on Spoof mail and Phishing mail attacks?
The answer to the question is that at the current time, there is a deadly cocktail that served at the local pub which includes the following Ingredients:
- The significant damage that caused by Phishing attacks (and Spoof mail attack that is part of the Phishing mail attack).
- The incredible ease of performing Spoof mail and Phishing mail attacks.
- The incredible lack of knowledge and understanding about the mechanism, and the characters of Spoof mail and Phishing mail attacks.
My main goal is – to be your wake-up call!
The lack of awareness of the risks that involved in Spoof mail and Phishing mail attacks.
Although it seems like that everyone knows the meaning of – Spoof mail and Phishing mail attacks, the simple truth is that most of the time, most of us, not really understand the huge impact of this type of attacks.
And, most of the time not really understand how this attack implemented, what are the main characters this attack and so on.
From my personal acquaintance with customers and organizations, there are some core beliefs; that prevent us from dealing with the risks of risks of Spoof mail and Phishing mail:
- It will not happen to me!
- Don’t rock the boat!
- We will deal with the problem when we get to it!
The type the above approach, causes us to close our eyes to this Immediate and tangible threat and hope that – if and when this risk will be realized, we will know how to deal with this “issue.”
Another belief is that when the time come, we will find a way to “outsource the responsibility” to another factor that we can blame.
The less good news is that in the case of Spoof mail attack and Phishing mail attacks, we can rely on the famous Murphy’s Law – “If anything can go wrong, it will!”
Alternatively, if you want, to put it differently – it’s not a matter of “if”, it’s a matter of “when.”
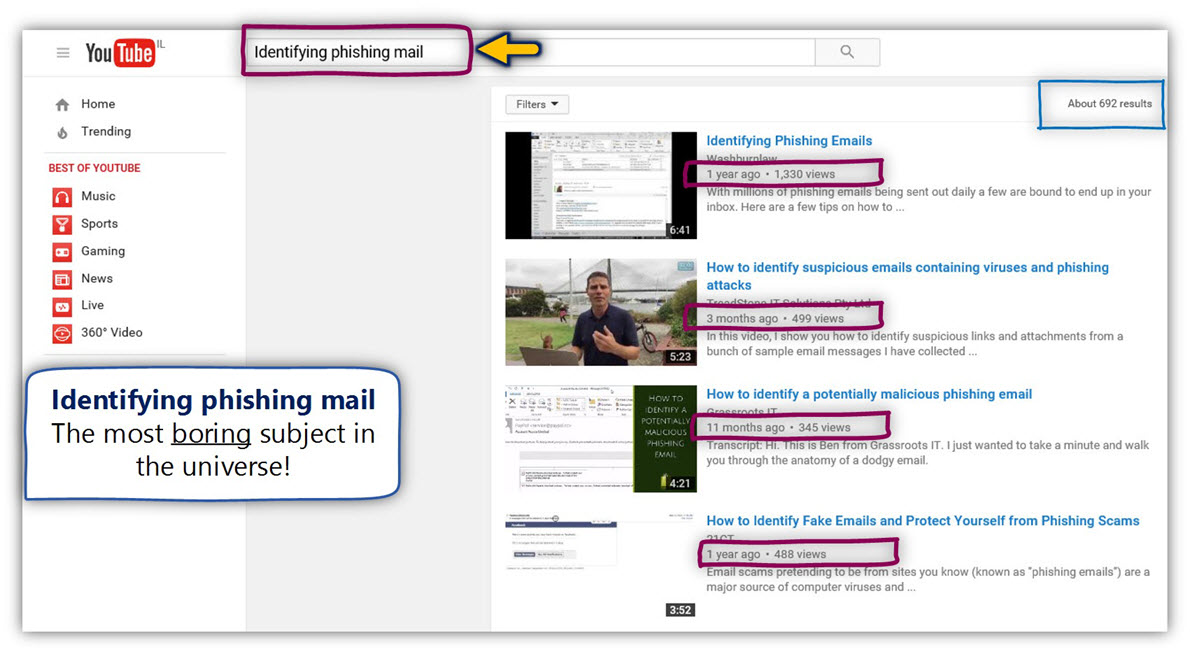
To emphasize my point, let’s do a little test that will enable us to be impressed from the
“level of interest” regarding two important subjects: Identifying phishing mail, and Kim Kardashian.
For the purpose of this test, let’s use the YouTube site as an indicator of the “level of interest.”
In the following screenshot, we can see the search results for the term “Identifying phishing mail.” We can clearly see that this issue is not a very popular subject.
The sum of the results that deal with this subject of Phishing mail is 700~.
The first result is a video that created a year ago, and the average number of “views” for the video results that appear on the first page measured in hundreds.
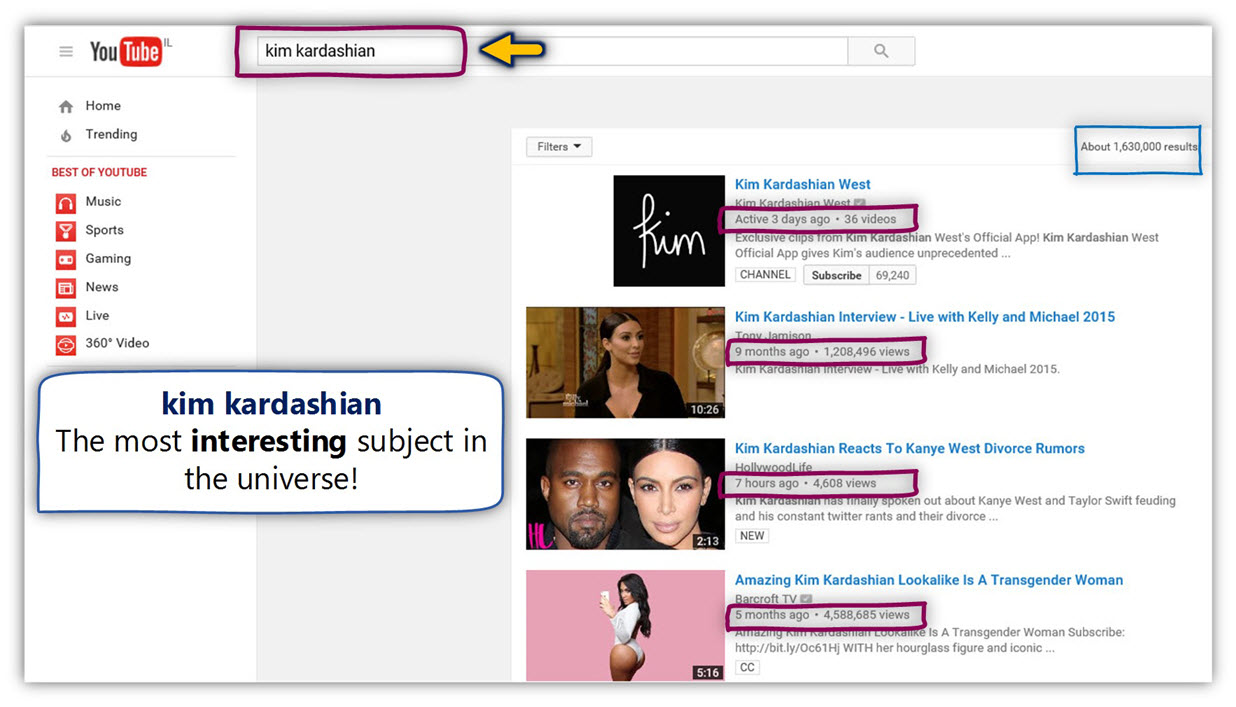
In the next screenshot, we can see the search results for the term – “Kim Kardashian.” We can clearly see that this issue is a very popular subject.
The sum of the results that deal with this subject is 1, 630, 000~.
The average number of “views” for the video results that appear on the first page measured in thousands and some video watched 4,500,000 ~.
A little about Spam mail before we continue with the subject of Spoof E-mail attacks and Phishing mail attacks.
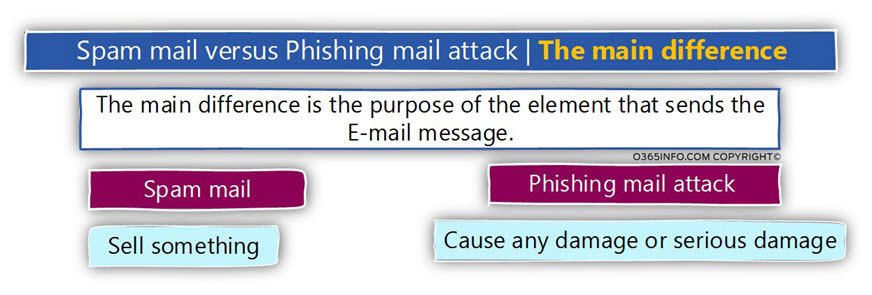
When reading a technical article about the subject of mail security and mail threats, the Phishing mail attack is frequently described as – a “subcategory” of spam mail.
I am strongly opposed to the above definition because this classification minimizes and reduces our awareness of the significant risk of Phishing mail attack vs. spam mail.
If we want to condense the primary goal of all the types of mail attacks, the simple answer is – “to earn money”.
The main difference between spam mail attack and Phishing mail attack is – the “way” that the element uses for getting the amount of money.
The similar characters of spam mail and Phishing mail
The common denominator of spam mail and Phishing mail is that way that the E-mail message is “distributed” among many destination recipients.
The primary target of “element” that sends spam mail and the element that sends Phishing mail is – to reach the largest possible number of target recipients, by using the option of bulk mail or mass mail.
The method for getting the E-mail address of the “victims,” could be similar such as using the option of Harvested E-mail address.

Note: This observation is not complete accurately because, when using a specific Phishing mail attack that described as – spear phishing, the attacker doesn’t use the option of bulk mail, but instead, aim his attack to a very specific organization recipient such as the company CEO and so on.
The difference between spam mail and Phishing mail
The main difference between spam mail attack vs. Phishing mail attack is the level of damage or the level of “wickedness.”
Most of the times, the “standard spam mail” can be considered as an E-mail that includes some kind of a message, that tries to convince you to buy “something.”
Apart from the harassment that caused by accepting “unwanted E-mail message” that compels the user to waste the time required for read or delete the spam mail, there is no other critical damage.
Note: There are “other damages” that are caused by spam mail such as – flooding of an organization, communication lines and the waste of storage space on the mail server but, from the “user perspective,” the spam mail is considered as a non-useful mail, and that’s all.
Regarding the subject on – possible damage that is caused by a Phishing mail attack, in this case, the story is entirely different!
The Phishing mail attacks “damage” could be translated into a specific user damage such as – breaking into a particular person’s bank account and stealing his money.
Another flavor of Phishing mail attacks can realized as an attack, that infects the organization infrastructure with malware that can take control over the organization infrastructure, encrypts hard disks and asking for a ransom and so on.
Regarding the “damage level” which can be caused by a Phishing mail attack, the sky is the limit!
Spam mail, a very brief review
Although this article series dedicated to the subject of Spoof E-mail attacks and Phishing mail attacks, I would like to “pay my debt” to the subject of spam mail, by providing a very brief review on this subject.
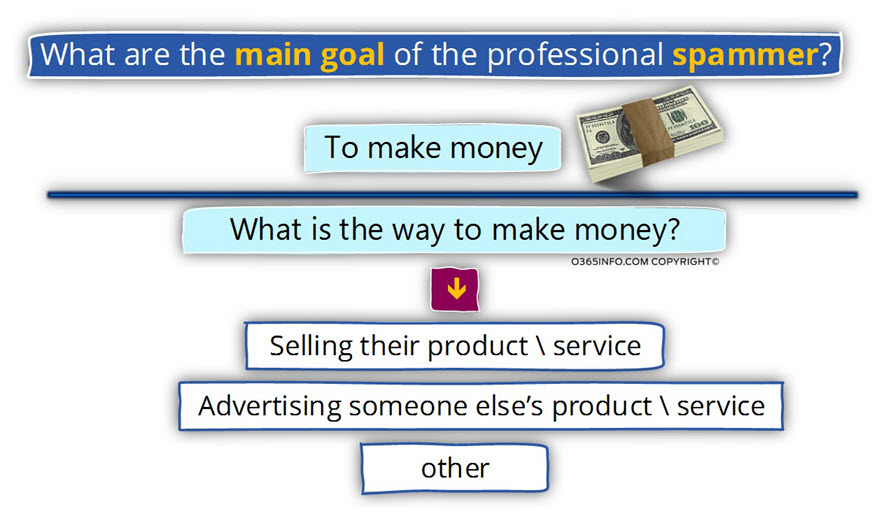
Know your enemy | What is the motivation of the spammers?
The main motivation of the elements which perform spam mail attack is – money.
A very useful way to make money and even a lot of money is – by selling something to someone.
One of the easiest and the profitable way of addressing a huge amount of “potential buyers” is – by using the Internet infrastructure.
The “thing” that the spammer wants to sell could be a product, a service or even an “idea.”
- The spammer may wish to promote a specific product \ service which he provides.
- The spammer may wish to promote a specific product \ service someone else’s product (affiliate programs).
- Other – I add the “other,” as a space holder for any other thing that the spammer has an interest to promote.
Spam mail | The risk level and the consequence
In general, we can define the “risk level” of spam mail as low or medium.
Although no one would like to get a spam mail, the damage of spam mail is not considered as a real threat to crucial assets of the organization.
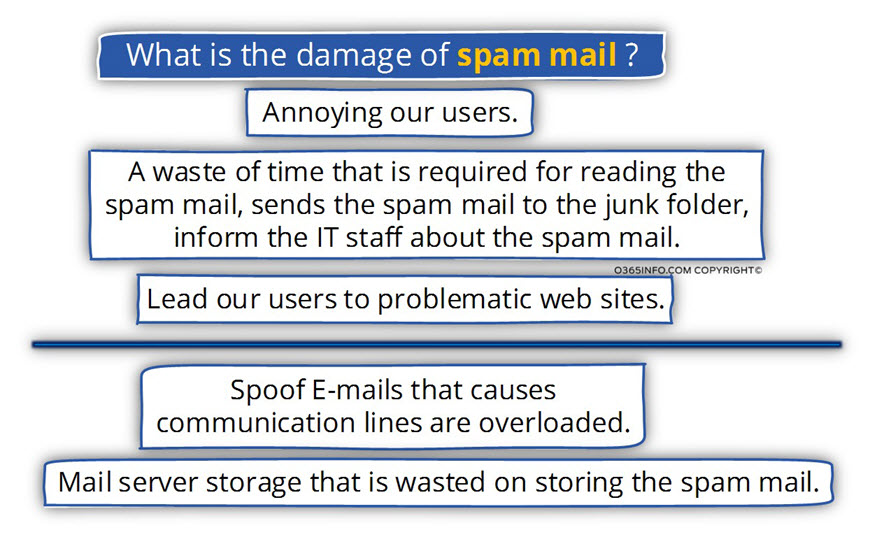
The possible damage from the spam mail attack could be:
- Annoying our users.
- A waste of time that required for reading the spam mail sends the spam mail to the junk folder, inform the IT staff about the spam mail.
- Lead our users to problematic websites.
Another type of damages that caused by spam mail are the damage of the organizational infrastructure such as communication line and storage:
- Spoof E-mails that causes communication lines are overloaded.
- Mail server storage that is wasted on storing the spam mail.
The way that spammers get our E-mail address
The last thing that I would like to relate to the subject of “spam mail” is the method which the spammers use for getting the information about the E-mail address of their “victims” (our users).
In a spam mail scenario, the most common complaint of the users is – that they never registered a particular mail list or didn’t provide their E-mail address to the element that sends the spam mail.
The simple answer is that most of the time, they are right!
The spammer gets the required information about the “E-mail address” of their victims by purchase E-mail lists of mediators who have a database of harvested email address.
These “brokers” know how to harvest this E-mail address from many types of resources such as – chat rooms, newsgroups, websites, social networking, blogs, Internet directories and so on.
Additional methods that spammer use described as – running a dictionary attack.
The dictionary attacks implemented by software engineers who know how to generate billions of combinations, which create “optional E-mail address” that are used by the spammer.
Note – the same methods for getting the E-mail address of the potential victims utilized by the hostile elm nets that perform Phishing mail attacks.

This Post Has 0 Comments