One of our Office 365 recipients complains that the E-mail that he sent to an…
Implementing SPF Fail policy using Exchange Online rule (dealing with Spoof E-mail attack) | Phase 2 production | part 3#3
The current article is the last article in the article series, in which we review how to implement SPF Fail policy using Exchange Online rule. Just a quick reminder, our main goal is to detect and prevent a possible event of Spoof mail attack.
Table of contents
- SPF Fail policy article series
- SPF production mode
- The business needs | Guidelines for our SPF Fail policy
- Our specific scenario characters
- Configure Exchange rule to identify SPF Fail Event – route the E-mail for approval + send notification to the destination recipient
- Verify Exchange Online SPF fail rule works properly
SPF Fail policy article series
The SPF Fail policy article series included the following three articles:
- Implementing SPF Fail policy using Exchange Online rule (dealing with Spoof E-mail attack) | Introduction
- Implementing SPF Fail policy using Exchange Online rule (dealing with Spoof E-mail attack) | Phase 1 – learning mode
- Implementing SPF Fail policy using Exchange Online rule (dealing with Spoof E-mail attack) | Phase 2 production (this article)
SPF production mode
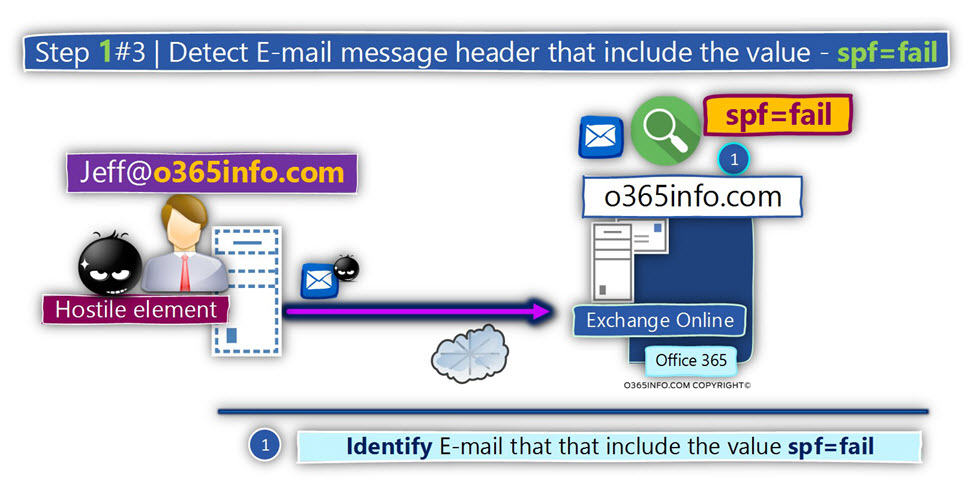
Given that our mail infrastructure uses an SPF sender verification check, in a scenario in which hostile element spoofs the identity of one of our legitimate organization users, the result from the SPF sender verification test is – “SPF = Fail”.
In the previous article, we implement the first phase, which described as – “learning” or “inspection” mode. The purpose of this first phase was:
- To get familiar with the common scenarios of Spoof mail attacks, which were aimed at our organization user
- Locate missing information in our SPF record about authorized mail servers
The basic assumption that we have already made the required adjustment for preventing false-positive events, which was caused by technically missed configuration and so on.
Now, we are ready to move on to the second phase, which I described as – “production mode.”
The main characters of this phase are that now we want to be more “active” meaning, intervene with the mail flow.
In this step, we want to prevent from E-mail messages that have a high chance of being a Spoof mail from being sent to the destination recipient.
If we want to be more accurate, we want to detect and block E-mail messages, in which the sender uses an E-mail address that includes our domain name and the SPF sender verification test result is – “Fail.”
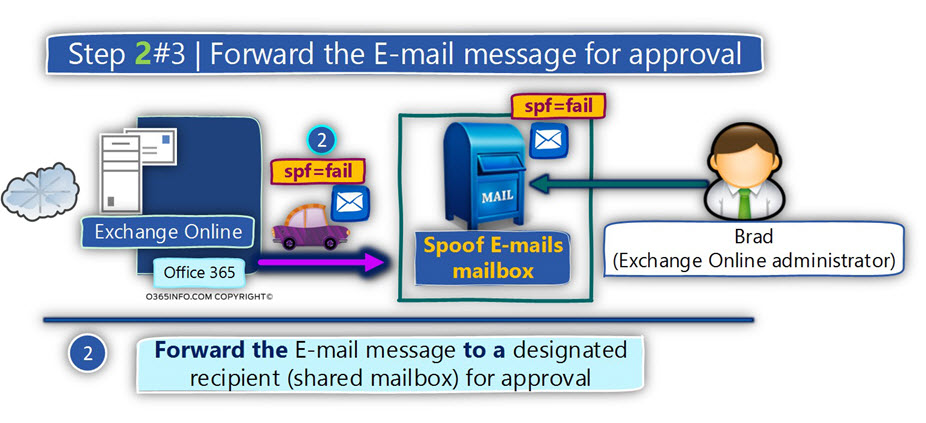
The “actions” that we will implement regarding the event of Spoof mail will be – “redirecting” the E-mail message to an isolated store (shared mailbox).
Only authorized personnel will have access this mailbox, and the designated user will need to examine the E-mail and decide if he approves to deliver the E-mail to her original recipient or not.
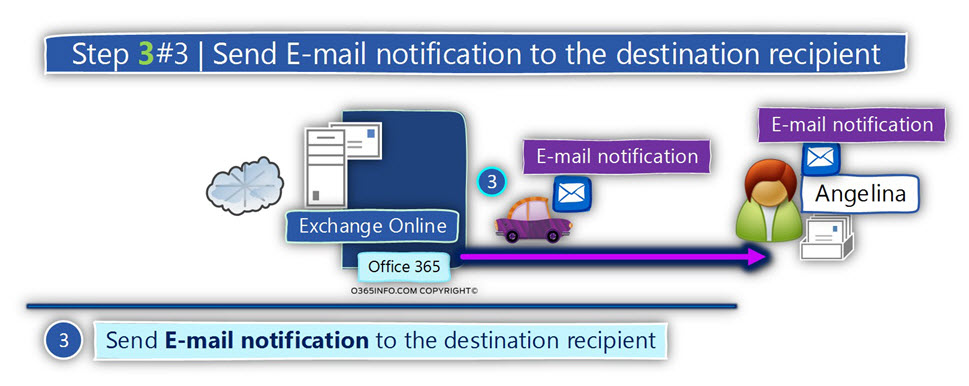
Also, a custom E-mail notification will be sent to the destination recipient, informing him that our mail infrastructure identified an E-mail that sent to him as – Spoof E-mail.
The business needs | Guidelines for our SPF Fail policy
The business need and the goals that we need to accomplish are as follows:
- We want to identify events in which E-mail messages that sent to our organization recipient have a high chance of being spoofed E-mail (spoofed sender).
From our perspective, the definition of “Spoof E-mail” is a scenario in which the sender E-mail address have our domain name (o365info.com) and also, the SPF sender verification test result is “Fail.” - We want to prevent from such an E-mail message reaching the destination recipient mailbox.
- We want to notify the destination recipient that E-mail message that was sent to him was blocked by our organization’s policy and sent to further inspection.
- The E-mail message that is identified by the Exchange Online rule as “Spoof E-mail,” will be forwarded to a designated shared mailbox named – spoof E-mail Mailbox.
- The “designated recipient” will be implemented by creating a dedicated shared mailbox for this purpose named – spoof E-mail Mailbox.
This mailbox will contain the incident reports that will be sent by the Exchange Online rule. - Only authorized user such as the Exchange Online administrator will be able to access the shared mailbox that stores the Spoof E-mails. This person will need to examine the E-mail message and decide if he approves to “release” the E-mail message and send it to the original destination recipient or not (reject).
Our specific scenario characters
To be able to demonstrate the way that we use Exchange Online rule for capturing the events of Spoof mail, in which the SPF sender verification test result is “Fail”, we will use the following scenario:
Our company public domain name is – o365info.com
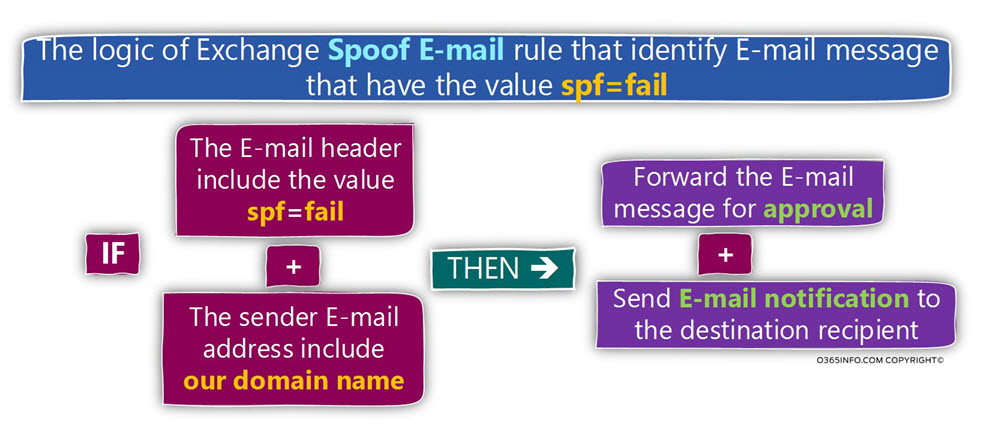
The condition | Identify an event of SPF = fail + sender domain is our domain
Our Exchange Online rule will be configured to “catch” event, in which the sender E-mail address includes the domain name – o365info.com in addition; the SPF sender verification test result is a Failure (SPF = Fail).
The Exchange Online rule “action”
The “response” of the Exchange Online rule will include two “steps”:
1. Forward the E-mail message to a designated mailbox (shared mailbox) for approval.
The Exchange Online rule will be configured to “route” to Spoof mail message to a designated mailbox, which will contain the “Spoof E-mails”.
An authorized person such as Brad our Exchange Online administrator will examine this E-mails
The authorized person will need to review the E-mail and decide if he approves or rejects the E-mail.
2. Send E-mail message notification to the original destination recipient.
Exchange Online will generate and send a custom E-mail notification that will inform the target recipient that E-mail message that was sent to him considered as Spoof mail.
The logic of the Exchange Online rule
A summary of the Exchange Online rule “logic” is presented in the following diagram:
Configure Exchange rule to identify SPF Fail Event – route the E-mail for approval + send notification to the destination recipient
In the following section, we will provide “step by step” instructions for creating the required “Exchange Online Spoofed E-mail rule” that will answer our business needs.
Part 1#2 – Configure the “condition part” of the Exchange SPF Fail rule
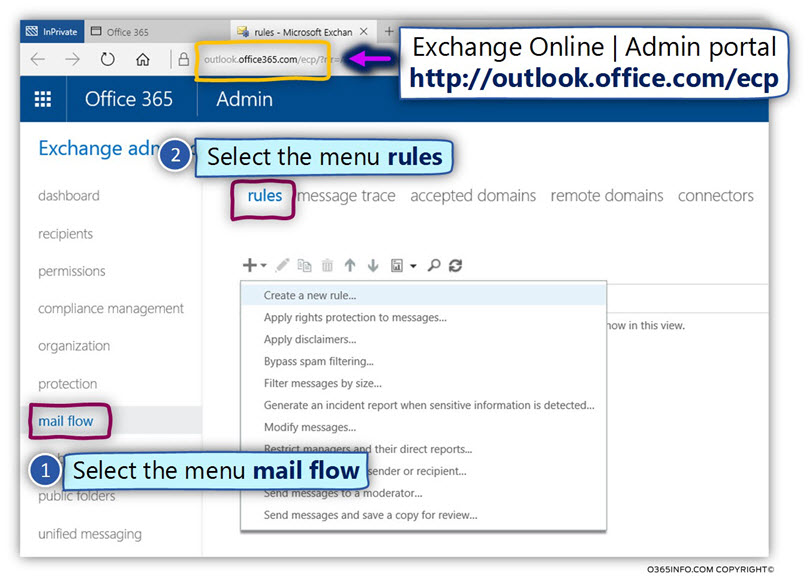
- Log in to the Exchange admin portal
- On the left menu bar, choose – mail flow
- On the top menu bar, choose – rules
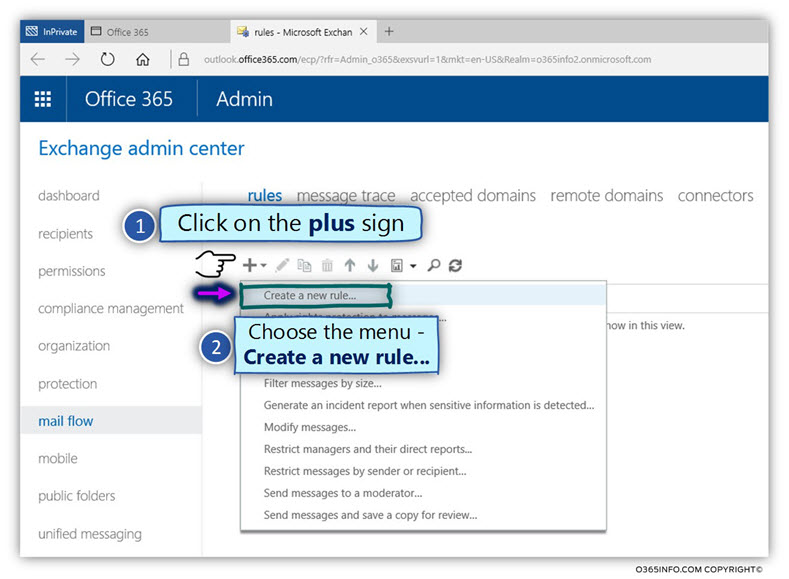
- Click on the plus icon
- Choose – Create a new rule…
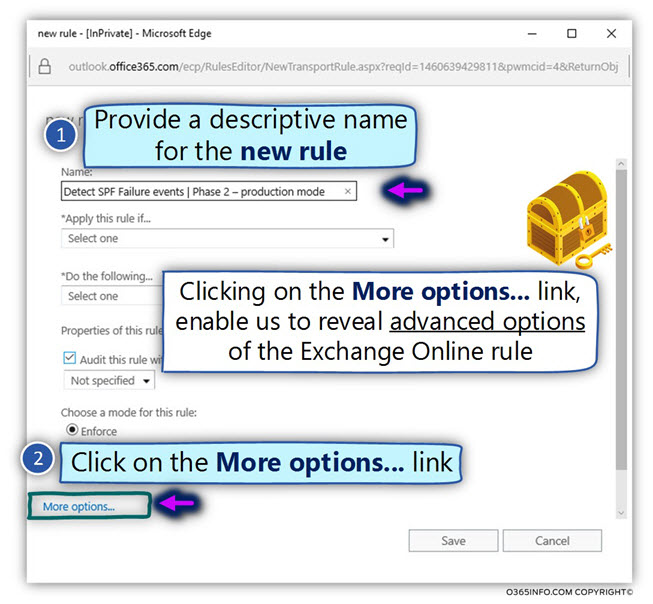
- In the Name: box, add a descriptive name for the new rule.
In our specific scenario, we will name the rule – Detect SPF Failure events | Phase 2 – Production mode. - Click on the –More Options… link
(by default, the interface of the Exchange Online rule includes only a limited set of options. To be able to display the additional options, we will need to “activate” the More Options…).
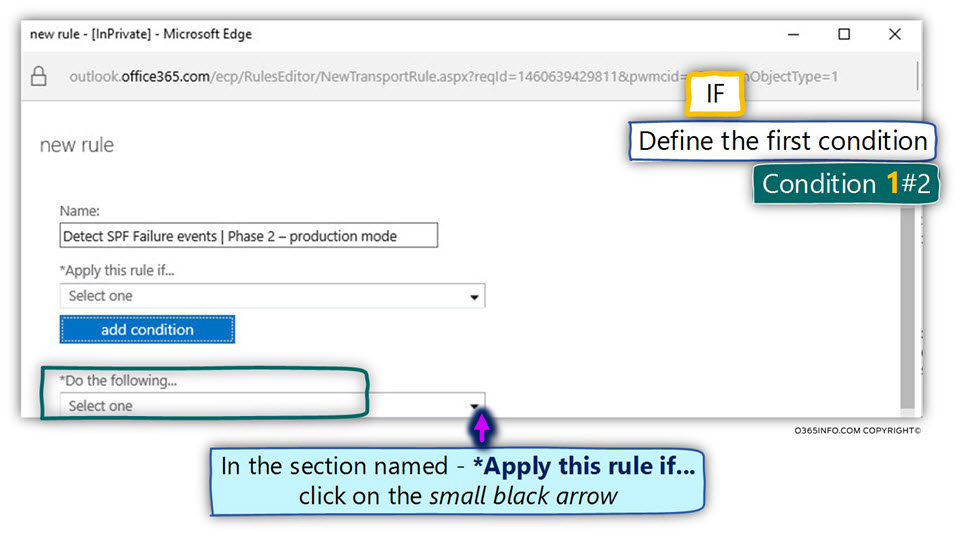
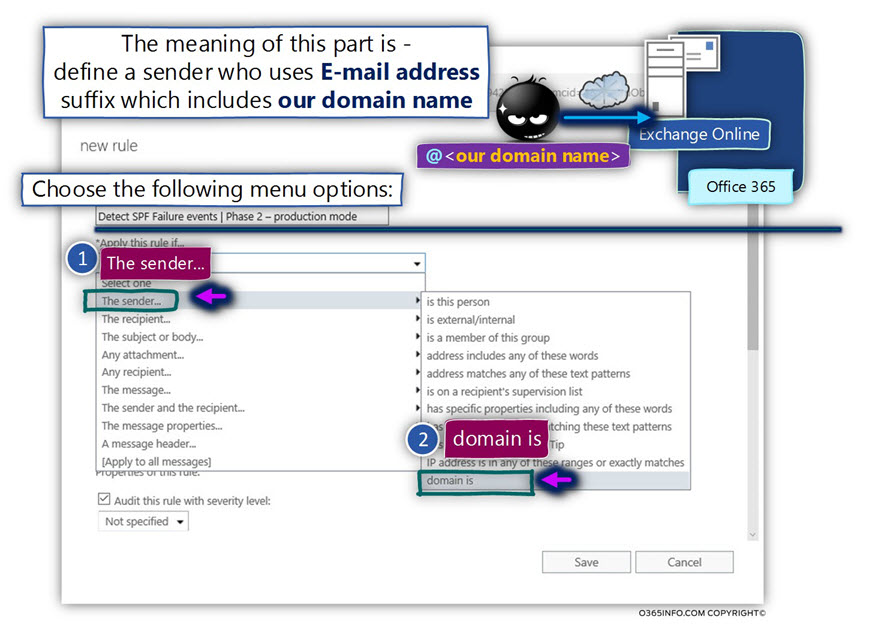
Condition 1#2
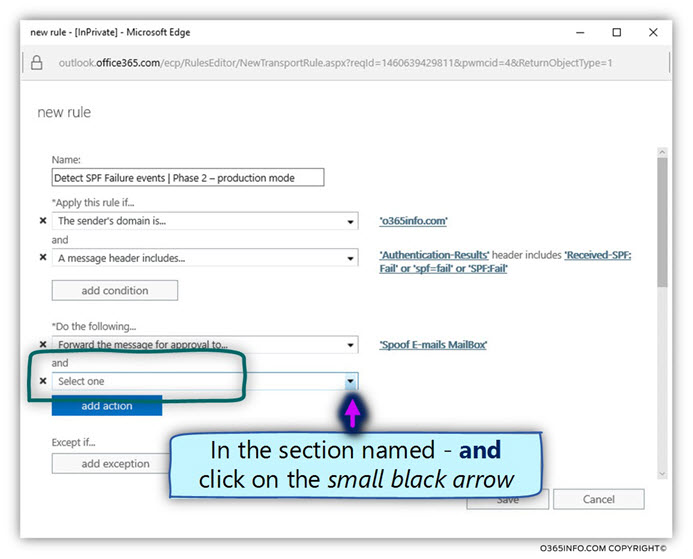
- In the section named –Apply this rule if… click on the small black arrow
- Choose the primary menu – The sender…
- In the submenu, select the option – domain is
- In the specify domain window, add the required domain name that represents your organization. In our scenario, the public domain name is – o365info.com
- Click on the plus icon to add the domain name to the list
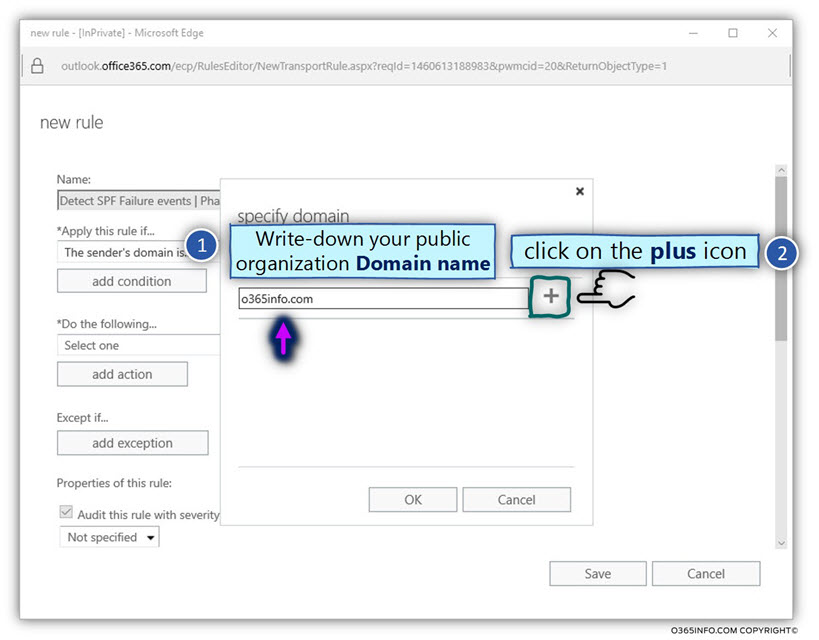
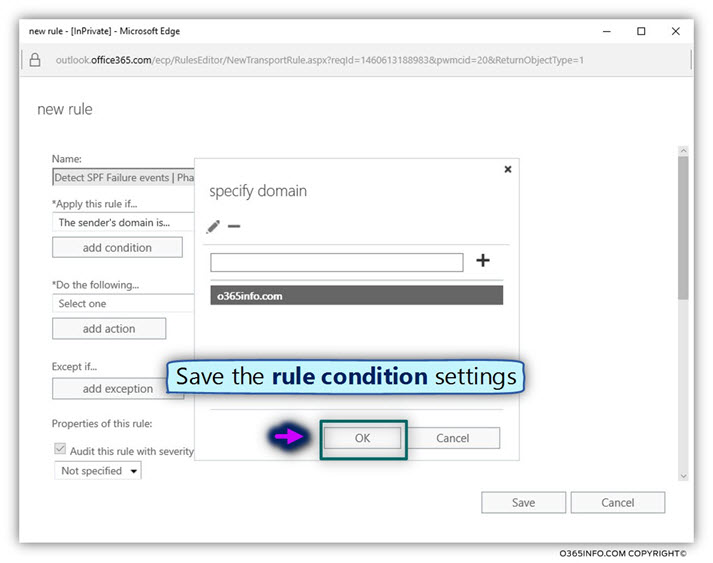
- Click on the OK option to save the Exchange Online rule settings.
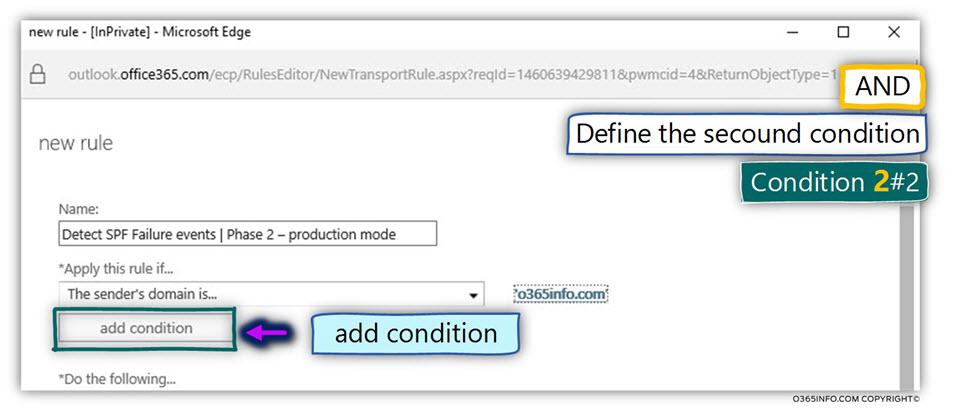
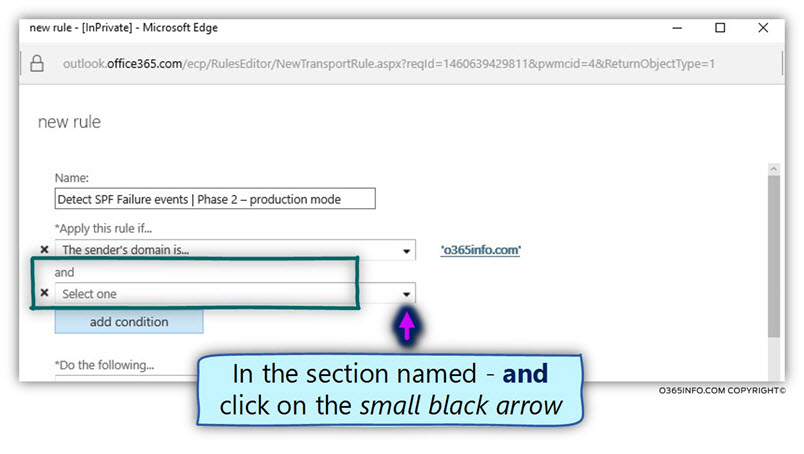
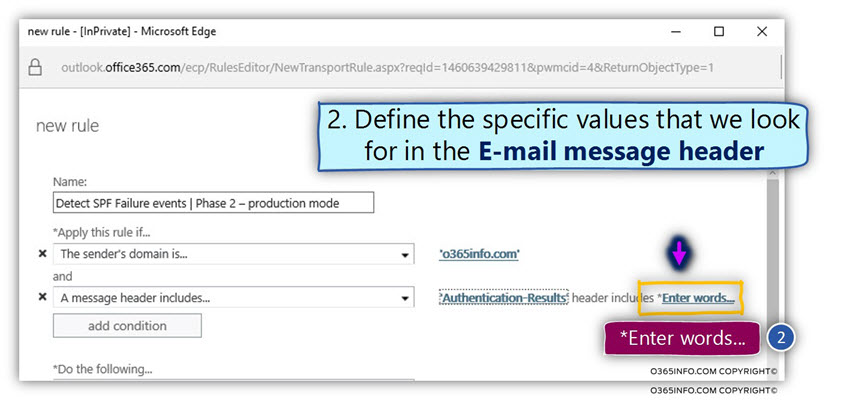
Condition 2#2
In the second condition, we instruct Exchange Online to look at each E-mail header and look for an event in which the SPF sender verification check is “SPF = Fail.”
- Click on the add condition
- In the box named – and, click on the small black arrow
- Select the main menu named – A message header…
- Select the submenu named – includes any of these words
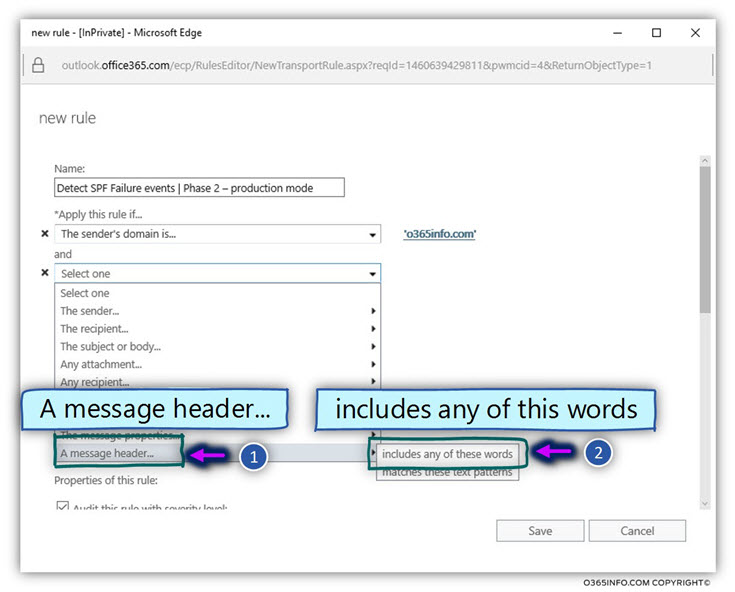
General information – the E-mail message header includes many “mail fields”.
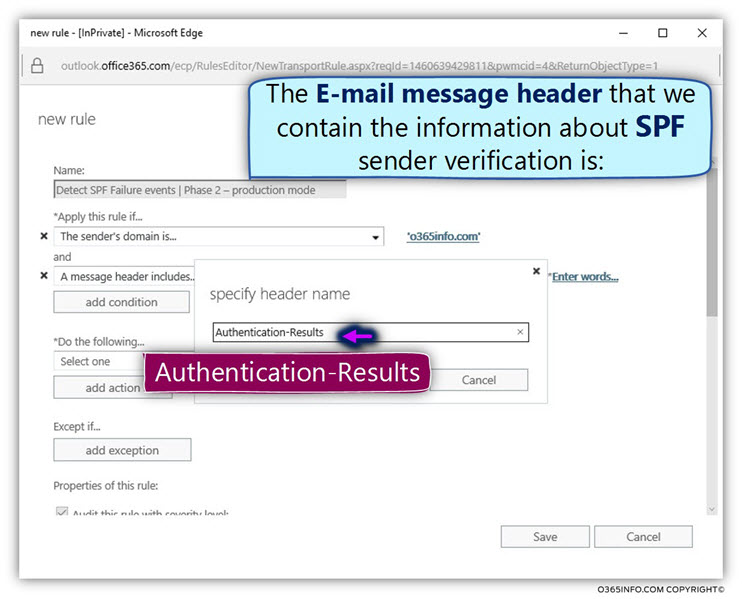
The specific mail field that contains the result of the SPF sender verification check is a mail field named – Authentication-Results
- Select the menu – *Enter text…
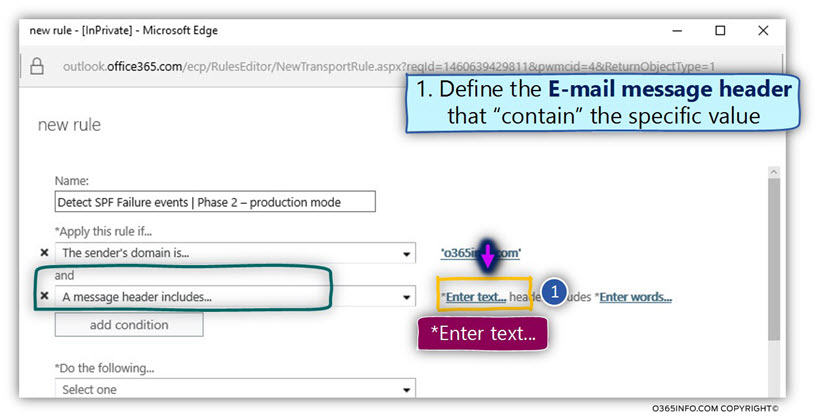
- Provide the name of the mail field that contains the result of the SPF sender verification check, in our scenario the mail field name is – Authentication-Results
- Select OK to save the information
General note – in this step, we provide the “text string” that we look for.
- Select the menu – *Enter words…
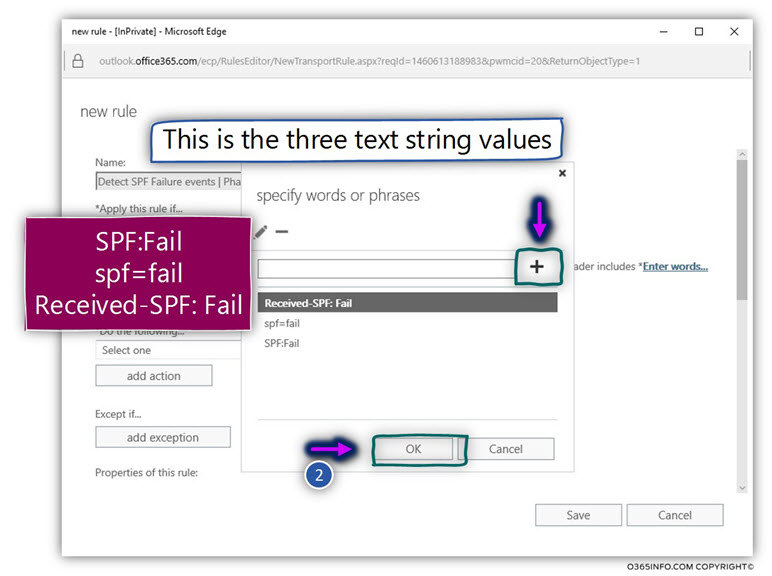
The information about the SPF sender verification test result, can appear in three different text style option:
- SPF:Fail
- spf=fail
- Received-SPF:Fail
We will add each of these options
- Write down the first option – SPF: Fail and click on the plus sign
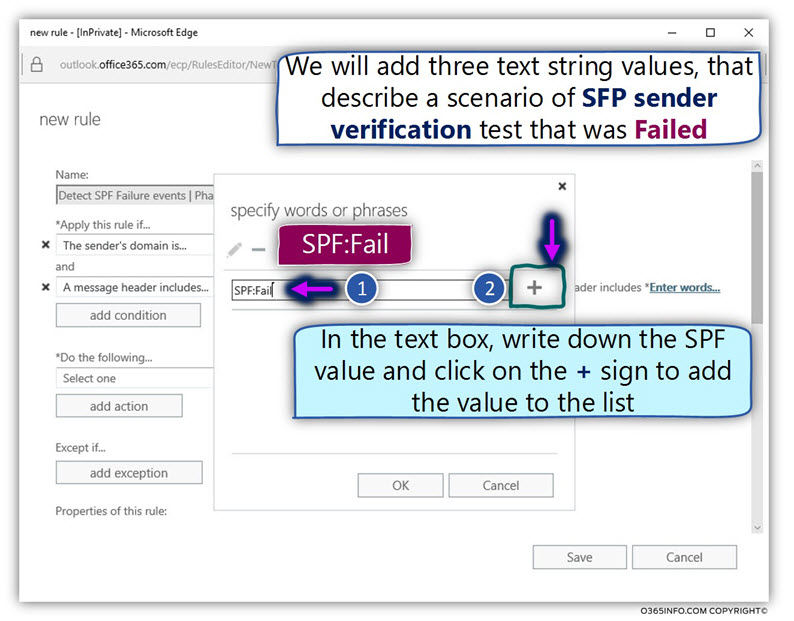
- Continue to enter the additional two SPF string values – spf=fail and Received-SPF: Fail
- Select OK to save the information that was entered
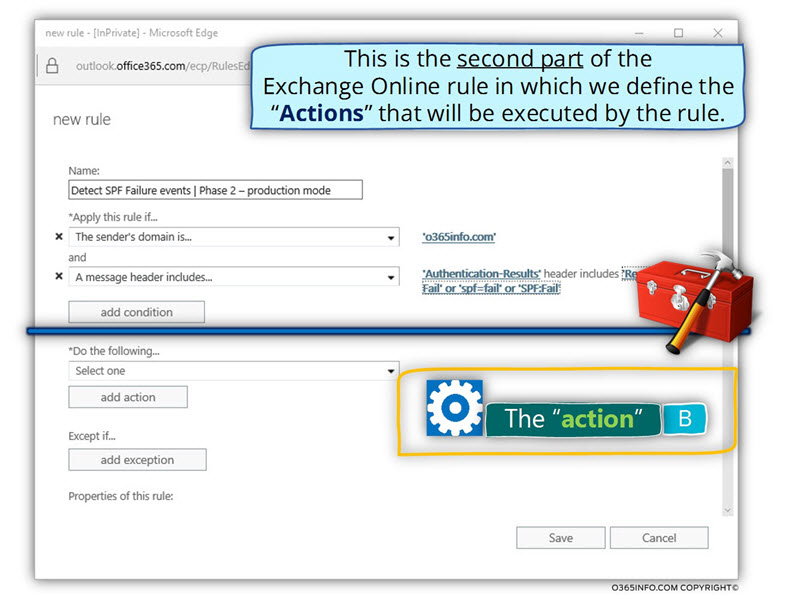
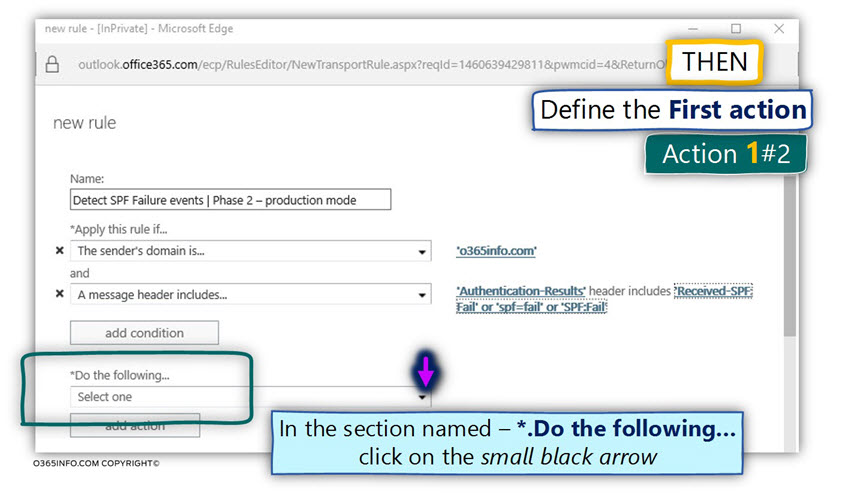
Part 2#2 – Configure the “action part” of the Exchange SPF Fail rule
In this phase, we will configure the “second part” of the Exchange Online rule.
In the second part, we define the actions (response) that the Exchange rule will execute.
The Exchange Online rule response, will include two distinct actions:
- Forward the E-mail message to a designated mailbox (shared mailbox) for approval.
- Send E-mail message notification to the original destination recipient who will inform him, that an E-mail message that was sent to him, is probably Spoof mail and that this E-mail message, was sent for further investigation.
Action 1#2 – forward the E-mail message to a designated mailbox (shared mailbox) for approval.
In our scenario, we wish to prevent the E-mail message from being sent to the destination recipient.
An E-mail that marked as Spoof mail will be sent to a “separate store”. In our scenario, the “separate store” is implemented by using a decided shared mailbox named Spoof E-mail Mailbox.
An only authorized user such as Brad our Exchange Online administrator will have access to this shared mailbox.
The person that is allowed to access the shared mailbox will need to inspect each of the E-mail messages that were classified as Spoof mail and decide if the E-mail is a legitimate E-mail (approve) or doesn’t approve (reject) the E-mail.
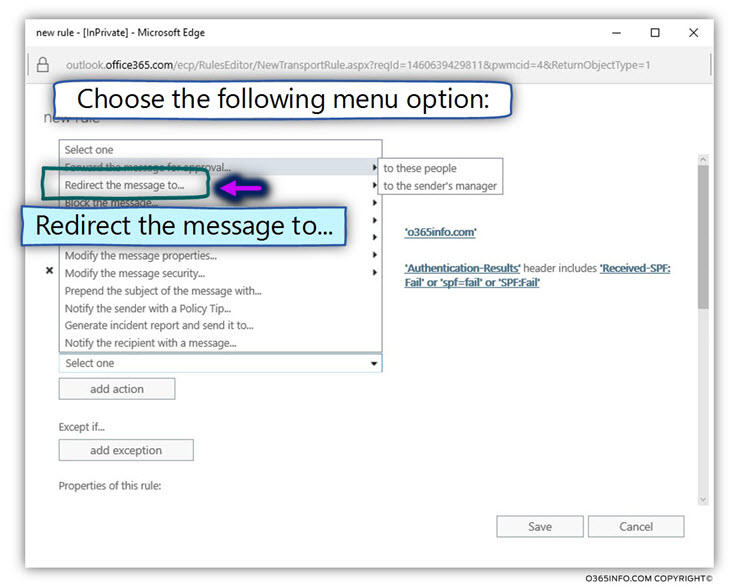
- In the section named – *.Do the following… click on the small black arrow.
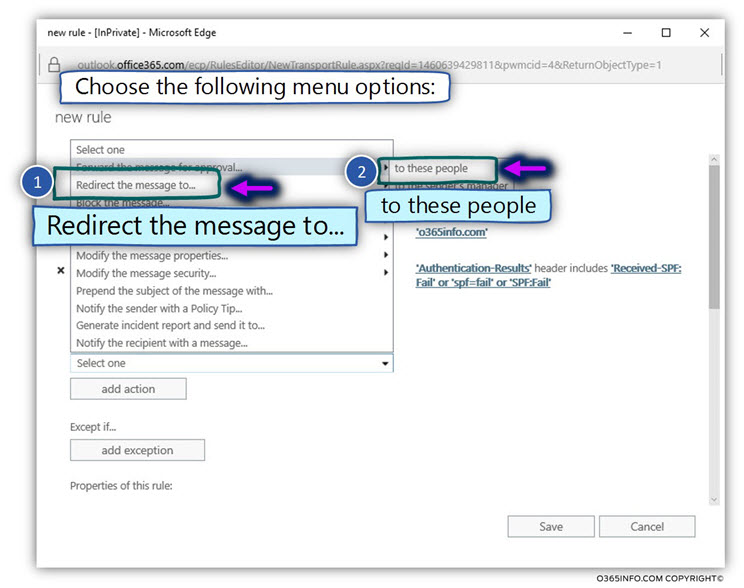
- Select the option – Redirect the message to…
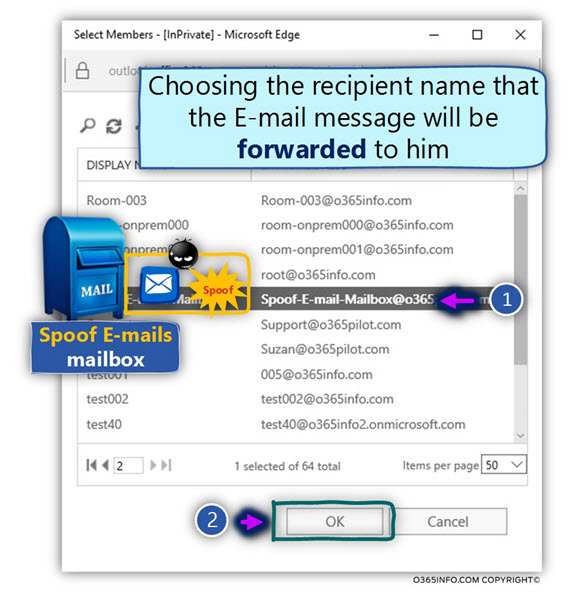
- Select the submenu option – to this people
- Select the specific recipient name (mailbox) to which the E-mail message will be forwarded. In our specific scenario, the recipient who will get the incident report is Spoof E-mail Mailbox.
Action 2#2 – sent E-mail notification to the original destination recipient
We would like to inform the destination recipient that an E-mail message that sent to him identified as a “problematic mail” (Spoof mail) and that the E-mail sent for examination by authorized personnel.
- Click on the option add action
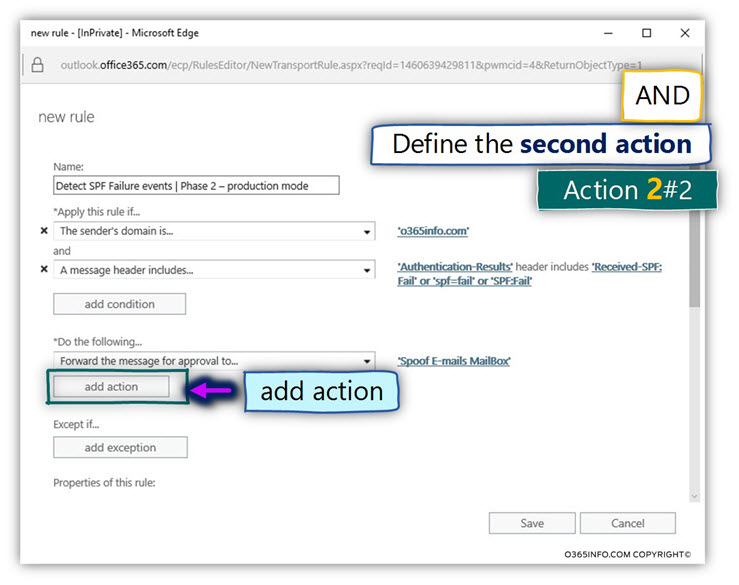
- In the section named – and, click on the small black arrow
- Choose the option – notify the recipient with a message…
In the following screenshot, we can see an example of E-mail notification information formatted using HTML.
If you want to download an example of such formatted text, click here
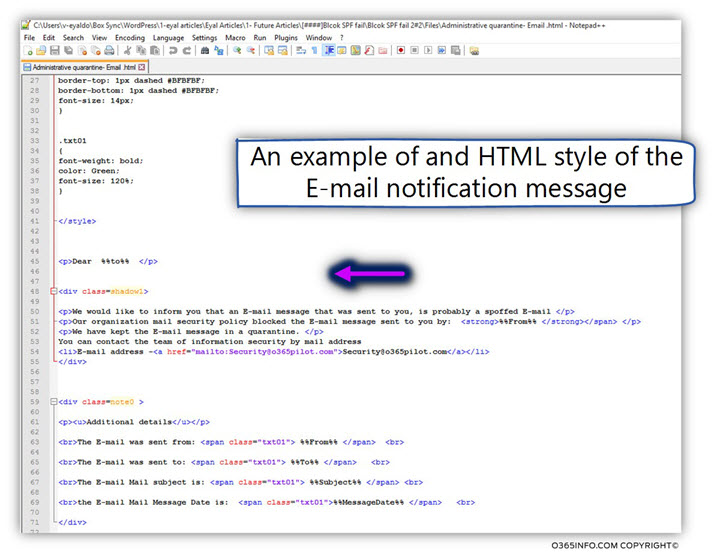
- In the text box, add the required notification text.
- Click OK to save the settings
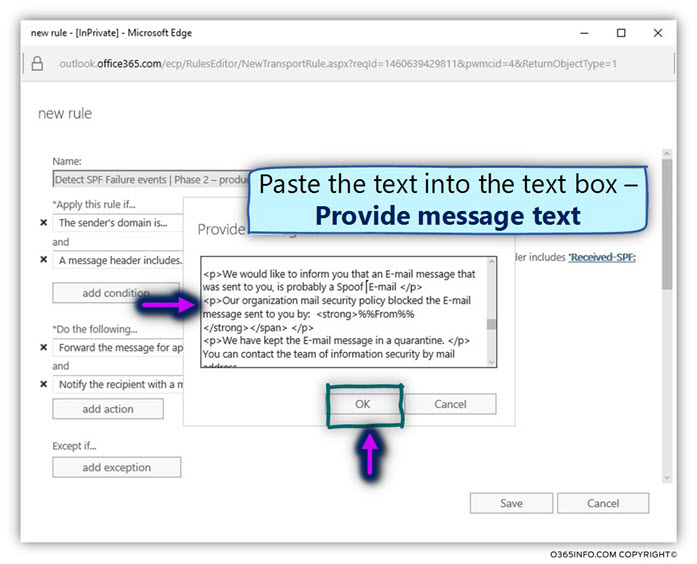
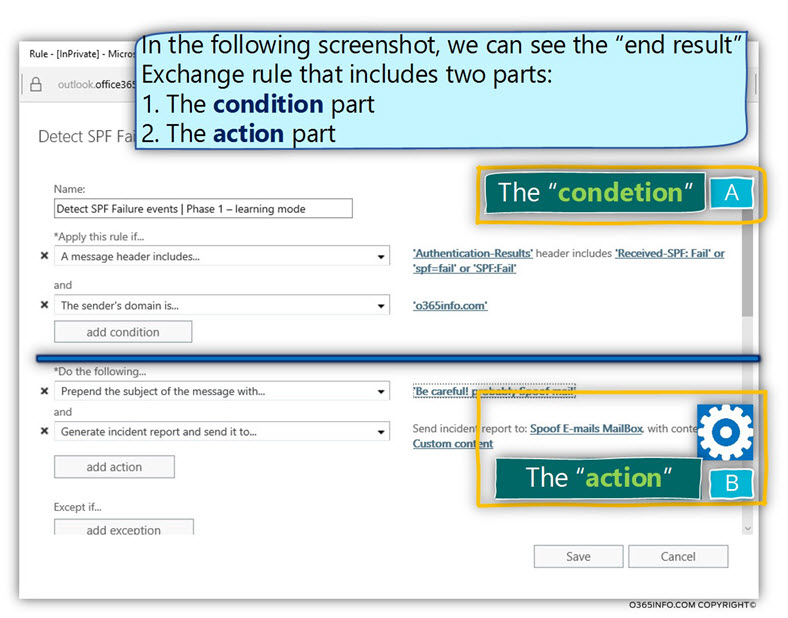
In the following screenshot, we can see he “final result” – the Exchange Online Spoof email that includes the two parts:
- The condition part
- The action part
Verify Exchange Online SPF fail rule works properly
In this phase, we would like to test the Exchange Online rule that was created in the previous step, and verify that the rule is working properly.
The expected results from the Exchange Online “SFP = Fail” rule
Our desired results are – that the Exchange rule will be activated when the following condition fulfills:
- Incoming mail that needs to be sent to one of our organization recipients didn’t pass the SPF sender verification test meaning; the SPF result is “Fail.
- The sender uses E-mail address with our domain name (the domain name o365info.com)
As a response, the Exchange rule will execute that following sequence of actions:
- Forward the E-mail message to a designated mailbox (shared mailbox) for approval.
- Send E-mail message notification to the original destination recipient which will inform him that E-mail that sent to his is probably Spoof mail that sent to further investigation.
Simulate a Spoof E-mail attack | Scenario characters
To be able to test the Exchange Online “SPF = Fail” rule is working properly, we will simulate a spoof E-mail attack that has the following characters:
We will send an E-mail message to one of our organization recipients, using a mail client that uses a public IP address that doesn’t consider as authorized IP address.
Our expectation, that the result from the SPF sender verification test will be “Fail”.
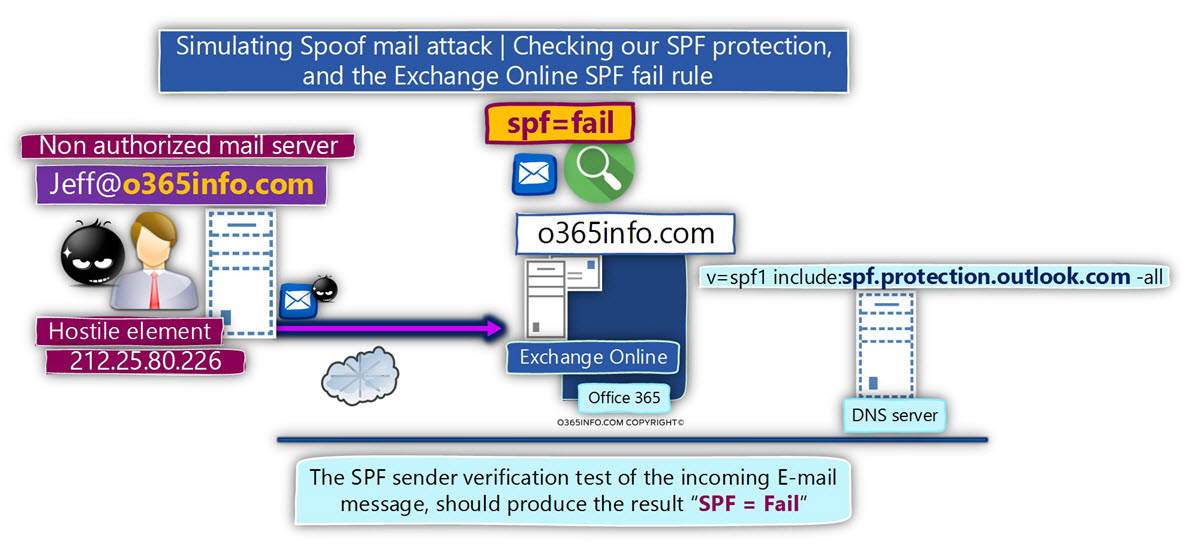
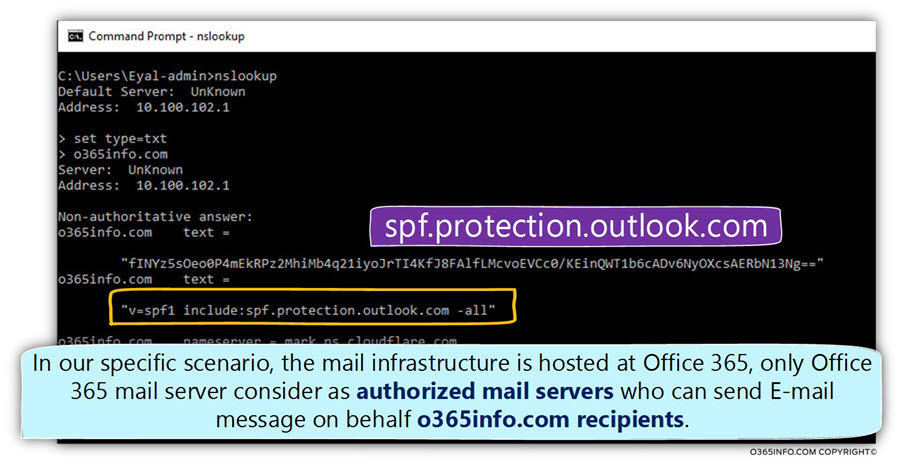
In the following screenshot, we can see the information about the SPF record that is used by the organization – o365info.com
In our scenario, the organization mail infrastructure is hosted at Office 365 (Exchange Online) mail infrastructure.
Only Office 365 mail server consider as “authorized mail servers” that can send an E-mail message on behalf of o365info.com recipients.
The source and destination recipient whom we will use are as follows:
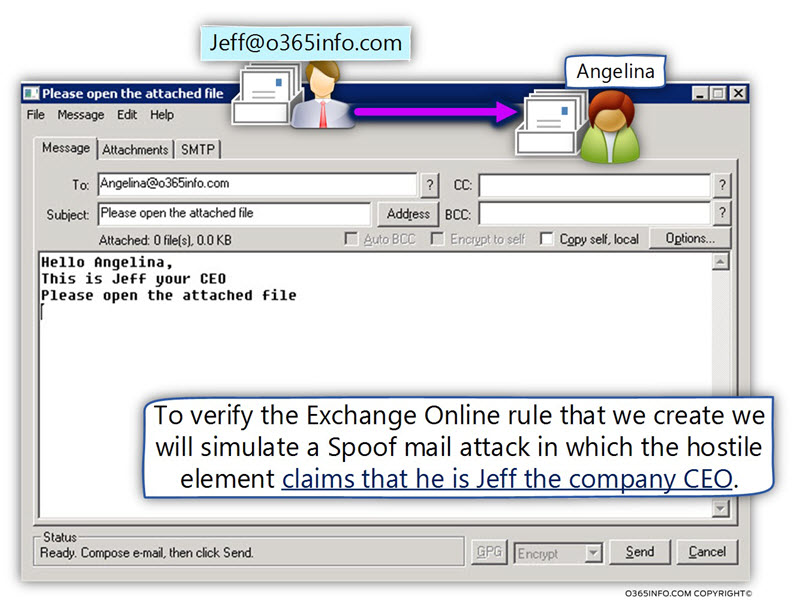
- A “hostile element,” is trying to spoof the identity of a legitimate organization recipient named –Jeff, which uses the E-mail address – Jeff@o365info.com
- The spoofed E-mail message will be sent to a legitimate organization user named Angelina, which use the E-mail address – angelina@o365info.com
In the following screenshot, we can see the mail client (jbmail) that we use for simulating the spoof mail attack.
If you like to learn about the way that we use for simulating the E-mail spoof attack, you can read the article – How to Simulate E-mail Spoof Attack |Part 11#12
1#2 – Verify that the Spoof E-mail was sent to the destination recipient
As mentioned, we want to prevent from the Spoof mail from be sent to the destination recipient. Instead of the “original E-mail”, the Exchange Online rule generates and sends a custom E-mail notification to the target recipient (Angelina in our scenario).
In the following screenshot, we can see the E-mail notification that was sent to Angelina.
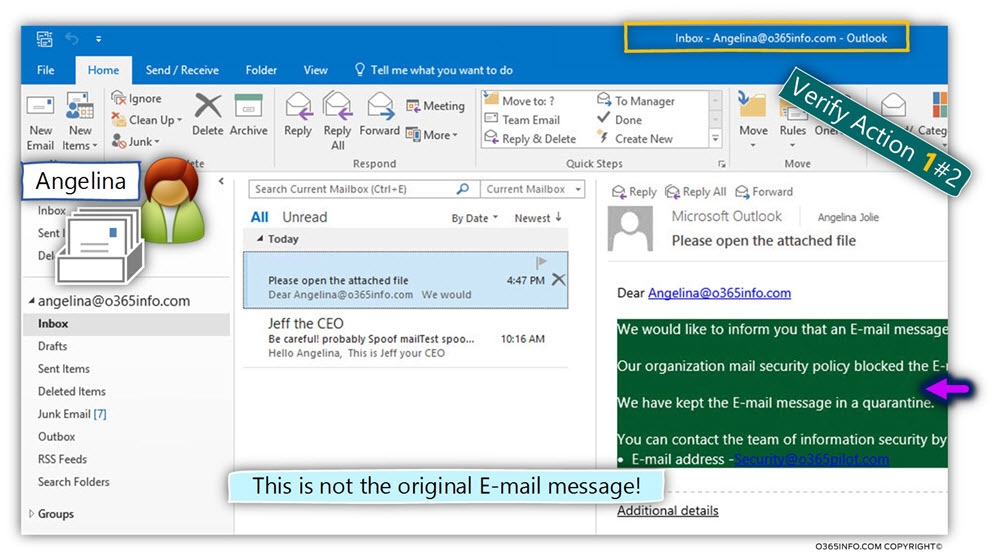
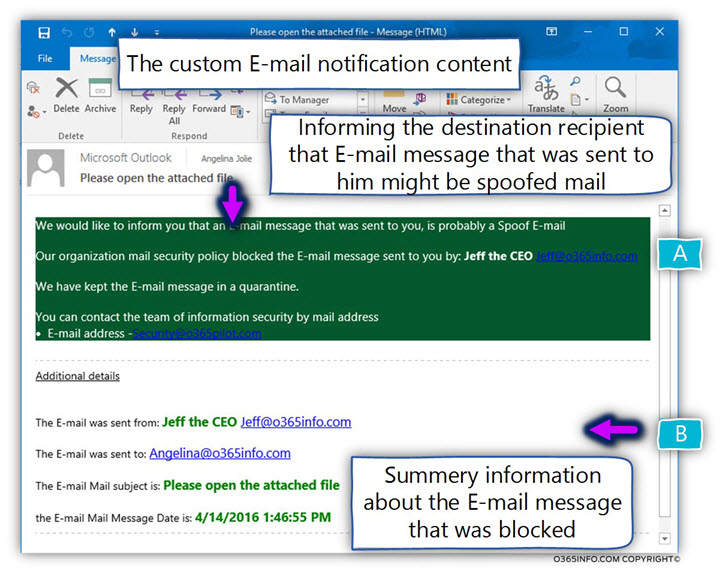
The custom E-mail notification includes two main parts:
Part A – in this part, we inform the destination recipient about the event in which E-mail message that sent to him, was identified as Spoof mail. Also, we provide the E-mail message to the security team in case that he wants to get more information about the particular E-mail message.
Part B – this part includes a summary report about the characters of the E-mail – the sender, the subject and so on.
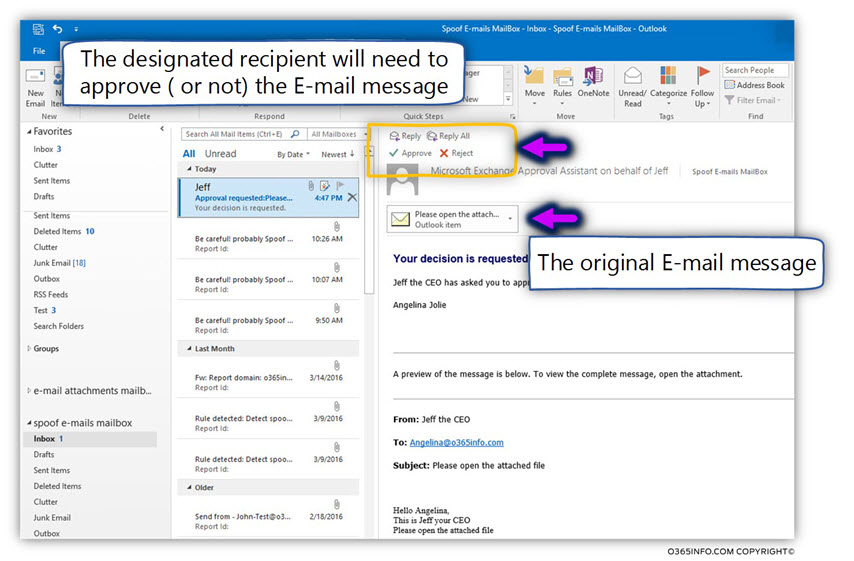
2#2 – Verify that the Spoof mail sent to the designated recipient for approval
In the following screenshot, we can see that the spoofed E-mail was “captured” and redirect to the selected mailbox. In our scenario, a shared mailbox named – Spoof E-mail Mailbox.
Our Exchange Online administrator – Brad, have full access to the shared mailbox – “spoofed emails mailbox”, and he can view the content of the mailbox.
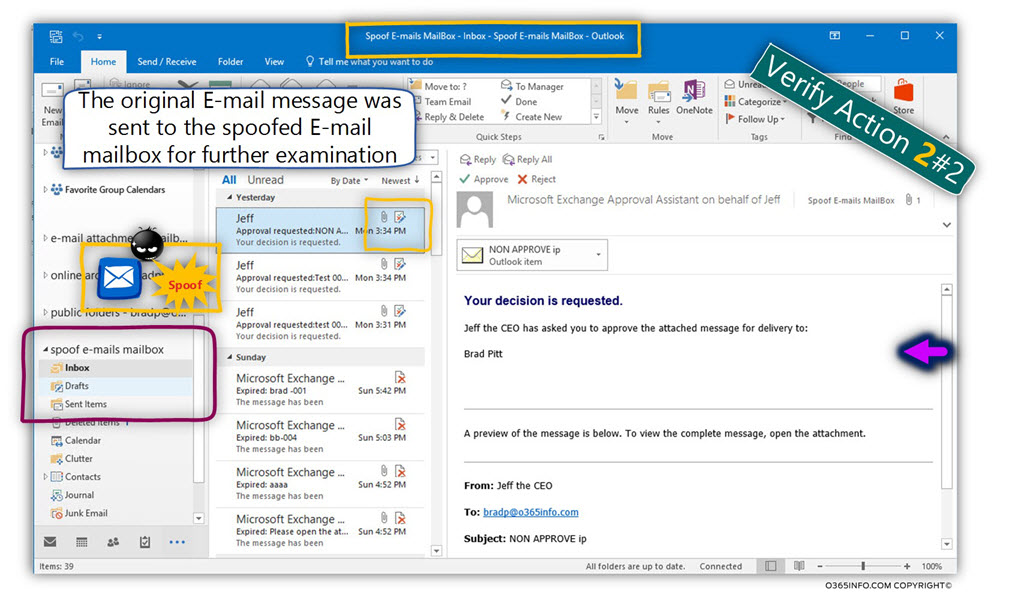
In the following screenshot, we can see an example of spoofed E-mail.
After inspecting the E-mail, Brad can decide if he wants to approve or reject the E-mail.


Also another question: in your article should there be spaces here: SPF:[space]Fail ; spf=fail ; Received-SPF:[space]Fail ?
If I want always to trust specific ‘xyz.com’ domain (that has SPF=Pass) should the rule condition syntax be like this: The sender’s domain is: ‘xyz.com’ AND A message header includes… ‘Authentication-Results’ header includes: SPF:Pass ; spf=pass ; Received-SPF:Pass
I always thought that “Inside the Organization” means authenticated users, but I just talked to Microsoft support and they told me that “Outside the Organization” means SPF = Fail i.e. all systems that are not listed in the SPF record are considered “Outside the Organization”
So probably you can have this and it should be working:
Apply this rule if
A message header includes… “from” header includes “@o365info.com”
AND
The sender is located… Outside the organization
Do the following…
What your thoughts are on this?
Hello Igor,
I’m not sure that I understand the question.
In case that you have an SPF record and in case that incoming E-mail address uses the organization domain (in my case o365info.com), the following flow will be implemented by the EOP server.
Case 1 – If the sender considers as authenticated user meaning provide credentials (user name and password), the SPF sender verification test will not be executed. The X-MS-Exchange-Organization-AuthAs value will be internal. As scenario in which the sender is authenticated described as – “Inside the Organization”.
Case 2 – If the sender considers as NON authenticated user, meaning anonymous, the SPF sender verification test will be executed. In this case, the output from the SPF sender verification test could be fail or pass.
If you want to get more information about the concept of “Inside the Organization” vs. “outside the Organization”, you can read the following article: Dealing with an E-mail Spoof Attack in Office 365 based environment | Introduction | Part 1#12.